Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Attendance System Based On Facial Recognition
Authors: K . Shivam, Ms. Bhanu Bharadwaj
DOI Link: https://doi.org/10.22214/ijraset.2022.43018
Certificate: View Certificate
Abstract
The face is the most important part of a person\'s identity. This physical characteristic has undergone a major change in methodology. Since the advent of image-processing technology, the goal of recognizing people is the only thing you can accomplish with a face recognition system. After recognizing someone, you can use more detailed processing to identify them. Traditional face recognition systems are not as accurate as you might want them to be. The system described in the present document is intended to deviate from this point of view. Introduce a traditional system to track students\' faces and a new, more modern approach to identifying students.
Introduction
I. INTRODUCTION
With rapid development in the field of Pattern recognition and its use in various fields. Signature recognition, face recognition, The Importance of Using These Technology Various areas of a large organization. This is mainly Because these applications help top management take over. With decisions to improve performance and organizational effectiveness. On the other hand, to be effective, the organization must be accurate and quick A way to record the performance of people inside This organization.
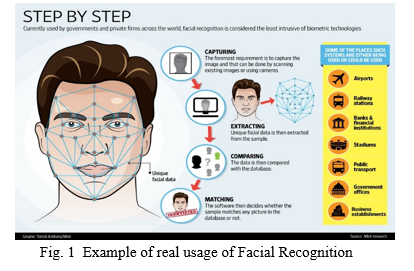
Biometrics may do so it will be an irreplaceable part of many identifications A system for assessing these performances People who work within an organization. but Biometric technology is used in many areas Warranty promises have not yet been redeemed Automatic human detection. Face recognition is a biometric technology recognition. It's the most successful application of image analysis Processing; that's the main reason behind the big ones in recent years, he has been the focus of attention. The face recognition process is similar to that Common face-based biometric process Biometric system detection; placement, function Extraction and matching are done. The face recognition process can be split into two main phases: pre-detection processing, where Face recognition and alignment are done (localization) And normalization) and then detection is done through feature extraction and matching steps.
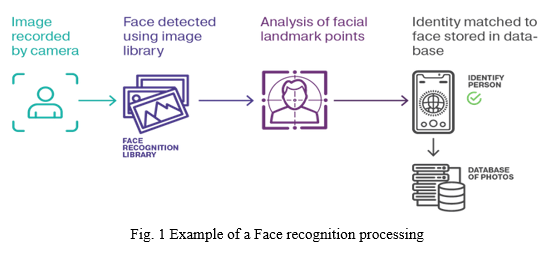
A. Face Detection
This process separates the facial area from the rest background image. For video streams, Faces can be tracked using the face tracking component.
B. Face Alignment
This process is optimal localization and Face normalization; where the detection steps This step to roughly estimate the position of the face Overview of facial components such as Face contour, Eyes, nose, ears, and mouth. Then normalize from the perspective of geometric transformations such as size and size Pose, in addition to such photometric characteristics Lighting and grayscale are done.
C. Feature extraction
After the previous two steps, feature extraction is done. It will be executed and effective information will be obtained. Useful for distinguishing different faces People and geometric and Photometric variations.
D. Feature Matching
They are compared to the saved features Database, and decisions are made according to Enough confidence in the outcome of the game.
Automatic face recognition technology has been used in many applications in recent years.
- Human-computer Interaction: Video games, virtual reality training Programs, proactive computing.
- Smart Card and Face ID: User authentication prepaid security, Driver's license, ID card, passport, voters register.
- Security: TV parental controls, device logins, applications Security, database security, file encryption, Secure trading terminals, medical records, Internet and intranet security, and terrorism warnings.
- Law and Video Surveillance: Stop warning crimes and suspects, suspects Tracking and investigation, suspicious background Check, post-event analysis, shoplifter recognition.
- Other: Time tracking and monitoring.
Face recognition applications are becoming more and more popular and expected to be used more and more and continue to grow widely used on both small- and large-scale applications. This research aims to try to provide one Automatic attendance system to recognize students' use of face recognition technology by Image/video stream for recording attendance at lectures or a section and its performance rating correspond. The goal behind this survey is Thoroughly studying the field of pattern recognition (details) Especially face recognition), this is very important and used in various applications such as identification and identification recognition.
II. BASIC SURVEY
The Basic ideal for Attendance System based on Facial Recognition came to my mind after reading the following IEEE papers:
- Rapid Object Detection using a Boosted Cascade of Simple Features
- Attendance Management System using a Mobile Device and a Web Application
- Web-Based Services – Useful or Not?
III. PROBLEM STATEMENT
Every time a lecture, section, or lab begins, the instructor or teaching assistant postpones the lecture. Record student attendance. This is a time-consuming process, especially in lectures with many students. It also causes a lot of confusion or interruption during the exam. In addition, the attendance list gets corrupted. Transmission loss between different faculties and staff students and the number of registered students is also there. Of course, teachers tend to call couples randomly named students, it's not a fair student. No evaluation process is done. Finally, these Records are used by staff to monitor students’ attendance rates. This process is simple and effective for a small number of students. On the other hand, it handles a large number of records. Students often lead to human error.
IV. PROPOSED SOLUTION
Suggested solutions for the above issue mentioned is by providing an automated attendance system for all students. A specific lecture, section, lab, or specific exam. Save time, time and effort, and reduce distractions and disorder. Another benefit of the exam When the instructor or counsellor accidentally loses one of the exam papers or the student is caught lying about taking the exam, an attendance list will be created for the student Current exams to protect both faculty and student rights. In addition, the automated services' ratings will be more accurate and reliable as a result of avoiding human error. The main goal of the system is deployed. It is a practical and dependable automatic attendance system. traditional interference and wasted time with attendance systems. Another goal is a system that can accurately score students’ performance based on registered attendance evaluation
V. REQUIRED SYSTEM
An analysis of user requirements and needs is an important task in all system development processes and is then concluded. The user must be the main concern of the system designer. Create something valid, useful, and user-satisfying. In this section, different requirements and needs are possible. The end-user of the system.
A. Student Requirements
The student must keep track of his or her attendance. This would necessitate him logging into the system with his ID and password. If his ID and password are valid, the system will accept him. Passwords are identical to those saved in the database and a page will be displayed under the Viewing his progress is one of the student's privileges, course and outcome.
B. Teaching Staff Requirement
The teaching staff requires an automated system that is efficient and dependable for documenting student attendance throughout lectures, sections, laboratories, and examinations. This system should be able to calculate and process student performance based on attendance rates. The teaching staff must maintain track of their courses and the attendance of their pupils. This would require them to enter their ID and password into the system, and if the ID and password entered are the same as the ones saved in the database, the system will accept them, and a page will appear according to their privileges, which are viewing their student's progress, course, and attendance reports. If the information supplied does not match what is in the database, an error page will show, prompting them to input the ID and password again. If the user forgets his password, the system will display a notice instructing him to go to the administration department to obtain a new password or to receive it via his email.
C. Administrator Requirements
The administrator must be able to enter them all. Users (students, teachers, and teaching assistants) create information with their ID and password. Access the system. Teacher placement and education Course support when accepting new teachers' systems. responsible for providing a new password for the percentage of users who have forgotten their login credentials. Add new Students can register for a course each semester.
VI. IMPLEMENTATION
We used a variety of techniques to try and recognize faces, including using colour-based detection and Principal Component Analysis (PCA). For skin colour detection, colour-based technology is implemented, but this is only for the detection of human skin colours. The photo is segmented and passed through the recognition process in various ways. We will use the classic machine learning pipeline, which involves importing libraries and data, performing exploratory data analysis and pre-processing, and training models before making predictions. The only additional step we will need to take before training our models is to perform PCA.
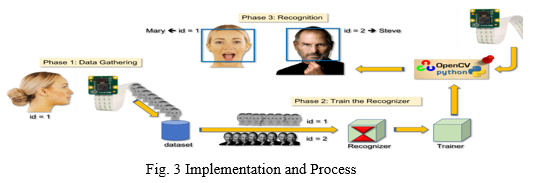
The classifier is designed in such a manner that it can be easily "resized" to be able to find the objects of interest at different sizes, which is more efficient than resizing the image itself. The classifier outputs a "1" if the region is likely to show the object (i.e., face), and a "0" otherwise.
OpenCV's Learn() function performs PCA on the training data to find a subspace. The PCA subspace is calculated by calling the built-in OpenCV function for doing PCA. The data for the learned face representation is saved as an XML file using OpenCV’s built-in persistence functions.
The call to loadFaceImgArray() loads the face images into the faceImgArr and stores the ground truth foreperson ID number in personNumTruthMat. The call to cvEigenDecomposite() projects the test image, which is similar to the face-projection code in the learn() function. The findNearestNeighbor() function computes the distance from the projected test image to each projected training example.
VII. ACKNOWLEDGEMENT
I would like to express our special thanks of gratitude to our research guide Ms Bhanu Bhardwaj Department of Computer Science and Engineering of Dronacharya Group of Institutions, Greater Noida who gave us the golden opportunity and motivation to do this wonderful project on the topic ATTENDANCE SYSTEM BASED ON FACIAL RECOGNITION.
Conclusion
The Facial Recognition Attendance System project aims to develop, comprehend, and automate an attendance system (clock in and clock out time) as well as keep track of students and staff in the classroom and at work. Django was used as a framework for web development during the implementation. The main detection and recognition processes used OpenCV, Viola-Jones Algorithm, and the Haar Cascade dataset. The open-source facial recognition library, bootstrap, and Dlib were utilised as resources.
References
[1] Y. S. Kulkarni, “Facial Recognition Attendance System,” ResearchGate, May 07, 2022. https://www.researchgate.net/publication/360449159_Facial_Recognition_Attendance_System (accessed May 19, 2022). [2] K. Rao, J Thirupathi, D. Naga, and O Kranthi Kumar, “Facial Recognition Attendance System with User Interface,” ResearchGate, Nov. 11, 2021. https://www.researchgate.net/publication/357206583_Facial_Recognition_Attendance_System_with_User_Interface (accessed May 19, 2022). [3] P. Dave, J. Agarwal, and T. Metta, “Face Detection using Principal Component Analysis (PCA),” ResearchGate, Jun. 18, 2014. https://www.researchgate.net/publication/272863602_Face_Detection_using_Principal_Component_Analysis_PCA (accessed May 19, 2022). [4] unknown, “Figure 1 Face recognition processing 3.3 In a linear subspace...,” ResearchGate, May 2015. https://www.researchgate.net/figure/Face-recognition-processing-33-In-a-linear-subspace-Euclidean-distance-and-Mahalanobis_fig1_275715187 (accessed May 19, 2022). [5] A. Jha, “Class Room Attendance System Using Facial Recognition System,” 2013. https://www.semanticscholar.org/paper/Class-Room-Attendance-System-Using-Facial-System-Jha/6740f4918d594094f5eca3c0c65006c9c6d6c1d4 (accessed May 19, 2022). [6] T. D. Russ, M. W. Koch, and C. Q. Little, “3D Facial Recognition: A Quantitative Analysis,” 38th Annual 2004 International Carnahan Conference on Security Technology, 2004. [7] P. Sinha, B. Balas, Y. Ostrovsky, and R. Russell, “Face Recognition by Humans: Nineteen Results All Computer Vision Researchers Should Know About,” in Proceedings of the IEEE, vol. 94, Issue 11, 2006. [8] F. IR, V. RR, J. S, J. M, and K. C, “Attendance Monitoring Using Face Recognition with Message Alert,” SSRN Electronic Journal, 2020, DOI: 10.2139/ssrn.3529319. [9] Zama Makhubu, “Class Room Attendance System Using Facial Recognition System,” Academia.edu, Sep. 22, 2015. https://www.academia.edu/16022060/Class_Room_Attendance_System_Using_Facial_Recognition_System (accessed May 20, 2022). [10] K. Nahar, “Twins and Similar Faces Recognition Using Geometric and Photometric Features with Transfer Learning,” ResearchGate, Jun. 21, 2021. https://www.researchgate.net/publication/352560413_Twins_and_Similar_Faces_Recognition_Using_Geometric_and_Photometric_Features_with_Transfer_Learning (accessed May 20, 2022). [11] J. Katona, “A Review of Human-Computer Interaction and Virtual Reality Research Fields in Cognitive InfoCommunications,” ResearchGate, Mar. 16, 2021. https://www.researchgate.net/publication/350117336_A_Review_of_Human-Computer_Interaction_and_Virtual_Reality_Research_Fields_in_Cognitive_InfoCommunications (accessed May 20, 2022). [12] Ren Honglei, Y. Song, and S. Yang, “An automated student attendance tracking system based on voiceprint and location,” ResearchGate, Aug. 25, 2016. https://www.researchgate.net/publication/320627662_An_automated_student_attendance_tracking_system_based_on_voiceprint_and_location (accessed May 20, 2022). [13] Vitomir Štruc and Nikola Pavesic, “Photometric Normalization Techniques for Illumination Invariance,” ResearchGate, 2010. https://www.researchgate.net/publication/283135495_Photometric_Normalization_Techniques_for_Illumination_Invariance (accessed May 20, 2022). [14] “Facial recognition 2021 and beyond - trends and market,” i-SCOOP, Feb. 03, 2020. https://www.i-scoop.eu/facial-recognition/ (accessed May 20, 2022). [15] N. Kar, M. K. Debbarma, A. Saha, and D. R. Pal, “Study of Implementing Automated Attendance System Using Face Recognition Technique,” International Journal of Computer and Communication Engineering, pp. 100–103, 2012, DOI: 10.7763/ijcce.2012.v1.28.
Copyright
Copyright © 2022 K . Shivam, Ms. Bhanu Bharadwaj. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET43018
Publish Date : 2022-05-20
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

