Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Automatic Door Lock System Using Face Recognition
Authors: Asmita Nagpure, Mayuri Sonule, Surja Chauhan, Shreya Bhowate, Kunal Meshram, Prof. H. V. Gorewar
DOI Link: https://doi.org/10.22214/ijraset.2022.42183
Certificate: View Certificate
Abstract
In this paper we\'ve proposed face recognition door cinch system using jeer pi for security purpose. Perpetration of the system is for covering whether any unknown person is entering in to the door. In order to get accurate and clear picture of an meddler we\'ve proposed Haar Cascade system for face discovery. As soon as the person enters near the door, pi camera captures the image and face discovery process is done also if it matches with database images also the door is uncorked else a communication with the picture of a person will be transferred to the registered mobile through LAN network. The main aphorism of this design is to application of detector with the combination of bedded outfit for the door opening systems. The main purpose of this system is to give better security by using face recognition fashion.
Introduction
I. INTRODUCTION
Currently, as the technology is adding, installations for mortal beings are adding. In day to day conditioning, life of people has come veritably easier with the objectification of numerous technologies.. This type of approach is nothing but where conduct can be taken incontinently as soon as a security trouble occurs. Hence a smart IOT grounded face recognition system is the idea to develop, which recognizes the face of the person near by the door and compares with the uploaded faces stored in the database. On the additional hand, it also creates security issues. In overall, in order to protected home, people kind use of CCTV. Images will store trendy the database, so that the act can be taken when any guarded incident happens. This type of approach is a unresistant. But there's a need for an active approach. If person is detected also the door would open and welcomes them. However, the proprietor would be advised by communication and correspondence with an meddler image, If an unknown person enters. To develop this system, we've used servo motor, servo motor controls the function of opening and ending of the door. Further revision in the system moved to biometric security system to insure better security. Biometric security system includes point grounded system was the first biometric locking system. Using the fingerprints of a person for unleashing the door is main parameter for this system. Still, like any other systems, they also have downsides. Fingerprints of a person can be duplicated. This can main to opening of the door for unofficial person. Eventually exploration moved to image processing system. This system provides high security.
This module is used in order to shoot dispatches to the registered mobile number. When a person wants to pierce his locker, originally at the main door of locker and detector will be placed. This detector will smell the body temperature of a person, standing near the door. And also, his/ her image will be captured by the camera installed at the main gate. This image will be given to the PC where the MATLAB software will compare this image with the authentic images stored in the PC If authentic, also only he door will open else it'll remain unrestricted and the alarm will buzz for farther action near the door for recognition of face.
II. LITERATURE REVIEW
In this design we using one camera which is identify a proprietor of home and open the door in many second. However, we not suitable to go home that we need someone how take watch our love bone's but then is problem how go inside the home because face recognition system that time we use alternate option the system well shoot announcement to proprietor told some stand out of door or the person call proprietor how to get inside the home by enter OTP, If in home kiddies or aged age's in home need further attention and care that time. From decades, for wisdom society using of smart home isn't a new term. As there's an advance in technology there's a fast increase in the field of home security robotization. The control of smart systems for automatic door cinch system is done through Bluetooth, internet etc. Utmost of the laptops, tablets, mobiles have erected-in appendages which in turn reduce the cost of the system, but it controls within the Bluetooth range. The system which is grounded on SMS technology have only one
A. CNN Algorithm
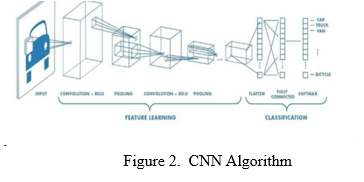
In neural networks, Convolutional neural network (ConvNets or CNNs) is one of the main orders to do images bracket. objects findings, recognition faces etc., are some of the areas where CNNs are extensively used. Technically, deep literacy CNN models to train and test, each input image will pass it through a series of complication layers with pollutants (Kernals), pooling, completely connected layers (FC) and smear soft max function to classify an thing with probabilistic values between 0 and 1. The below figure is a complete inflow of CNN to reuse an input and classifies the objects grounded on values.
.
Equations
Machine learning cnn , in short, the answer is as follows:
Output height= (input height + padding height top + padding height bottom – kernel height) / (stride height) +1.
B. Har-Cascade Classifier
Object detection using Haar feature based cascade classifiers is an efficient object detection method proposed by Paul Viola and Michael Jones!". it's a machine education founded style where a cascade meaning is trained from tons of positive and negative images. It is then used to notice objects in other pictures. Here, we are working with face detection. Initially, the algorithm needs tons of positive images (images of faces) and negative images (images without faces) to coach the classifier. Then we'd like to extract features from it. Features are nothing but numerical information extracted from the pictures which will be wont to distinguish one image from another.
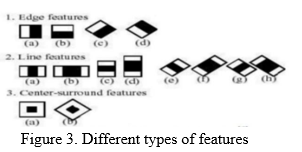
Figure 3 shows different Haar features. A simple blockish Haar like point can be defined as he differences of the sum of pixels of areas inside the cube, which can be at any position and Scale within the original image. A Haar-suchlike point considers bordering blockish regions at a specific position in a discovery window, totalities up the pixel intensities in each region and calculates the difference between these totalities. First, the pixel values inside the black area are added together also the values in the white areas are added. This result is used to classify image sub regions. An illustration of this would be the discovery of mortal face. Commonly the areas round the eyes are murkier than the areas on the cheeks!). One illustration of a Haar like point for face discovery is thus a set of two bordering blockish areas above the eye and impertinence region.
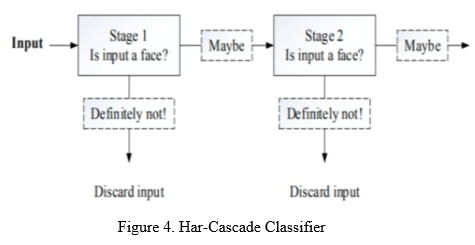
C. Proposed System
After preprocessing like resizing and cropped images, Haar waterfall classifier is used to descry whether there's a single face detected or not. Figure 4 demonstrates the flowchart for the proposed system. Edge, line, and center compass are the features of Haar which are acting as inputs. By these waterfall features the test of the image is done. The features of Haar are divided into colorful different stages. Stage thru stage the window will be tested. Generally original stages will have lower Haar-such like features. However, also it's to be discarded and the coming stages won't be tested, If the first stage window fails. However, 12, 13, If all the stages successfully passes also it's considered to be face is detected and checks with the images formerly stored in database of jeer Pi (9. The advantage of Haar waterfall classifiers is fast discovery speed compared to other classifiers.

D. Methodology
The first task is to gather the data for which we're going to train our classifier. We'll write a python law that will take 30 faces of each person using OpenCVpre-trained classifier. When the person press the button, the enforced law now called using the camera, system prisoner the image sequence and compare this image with database. However, also in operation module get the signal to the door, If the image is match. In this design, for face discovery and identification we're using machine literacy, deep literacy and python. For honor face we using camera and for controlling the locking system we are using nodemcu and all modules integrated through garçon.
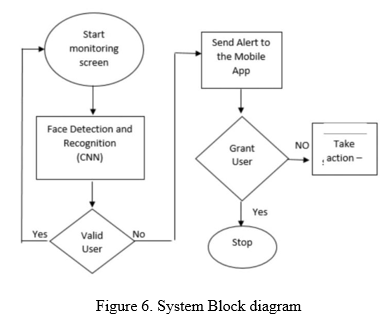
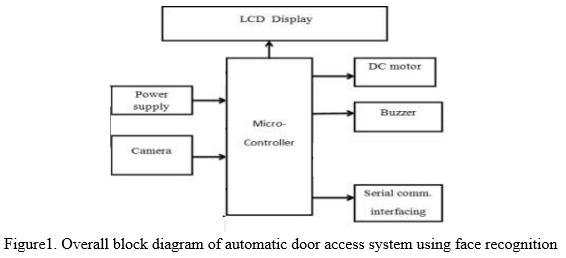
According to below block illustration shown above, first stir is detected by detector also the image is captured by camera which is input to the microcontroller, Microcontroller checks whether given input is saved within thedatabase.However, which is mechanical function done by DC motor, If so the door will open. If input image doesn't match with the database also door will remain unrestricted and Buzzer will start telephoning. The result will be demonstrated on the TV. This design uses system to shoot announcement of an unauthorized person and also to connect tackle with PC it uses periodical communication interfacing.
E. Circuit Diagram
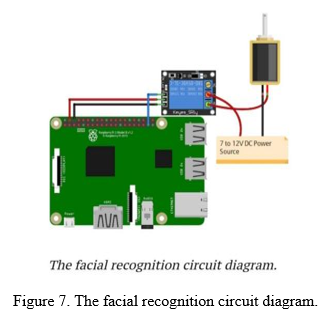
The circuit shows the design of automatic door cinch system. The factors used are nodemcu, solenoid, appendage. detector works as a main function. a live body generally emits infrared energy which is tasted by the detector from considerable distance. This seeing signal is fed to a microcontroller to operating range of the detector, it sends a logical command to open the door. The door automatically closes with fixed time detention. If there's no farther movement within the operating range. Intrude signals are used through limit switches to avoid locked rotor condition of the motor. The GPIO legs of the Jeer Pi can give an affair of3.3 V but the solenoid cinch requires 7-12V to operate. Because of this, we will need to use an external power source and relay to operate the cinch. Connect the VCC and GND of the relay unit to 5V and GND of Raspberry Pi. Also connect the indication leg of the relay element to the GPIO 26 of RaspberryPi. On the other side of the relay module, connect the negative form DC power source to the negative of the solenoid door cinch. Connect the positive from the DC power source to the common of the relay module and also connect typically open from the relay module to positive of the solenoid doorlock. machine literacy algorithm is used to avoid the complexity of computations, which is inbuilt in Open CV library. Jeer Pi processes the captured image coordinates with the being equals in the database. If it matches also it sends the signals to bear switch through GPIO legs.
III. HARDWARE DESIGN
A. I3 Processor
Established and artificial by “ Intel” and first introduced and released in 2010, The core i3 is a binary- core computer processor, Available for use in both desktop and laptop computers. It's one of three types of processors in the “ I” series ( also called the Intel core family of processors)
B. Webcam
A webcam is a videotape camera that feeds or streams an image or videotape in real time to or through a computer network, similar as the Internet. Webcam software enables druggies to record a videotape or stream the videotape on the Internet.
C. WIFI ESP8266
The ESP8266 WiFi Module is a tone contained SOC with integrated TCP/ IP protocol mound that can give any microcontroller access to your WiFi network.
D. IC 7085
The 7805 voltage checker is a three-terminal voltage regulator IC. In colorful operations, a 7805 voltage controller with fixed affair voltage is used
E. Servo Motor
A servo motor is rotary actutator or direct actutator that allows for precise control of angular or direct position, haste and acceleration. It consists of a suitable motor coupled to a detector for position feedback.

IV. IOT COMPONENTS
A. NodeMCU
NodeMcu is a low cost open source IOT platform. It originally included firmware which runs on the ESP826 wifi SoC from Espress if systems, and tackle which was grounded on the ESP-12. Latterly, support for the ESP32 32- bit MCU was added. .
B. Adapter

An adapter or adaptor is a device that converts attributes of one electrical device or system to those of an else inharmonious device or system. Some modify power or signal attributes, while others simply acclimatize the physical form of one connector to another.
V. IMPLEMENTAION
There are single corridor in this perpetration step. The perpetration of face discovery and face recognition system by using MATLAB.
A. Implementation of Face Detection And Recognition
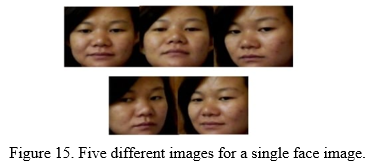
Matlab2014a is used for rendering. In the database brochure, 50 different facial part of images for ten persons are used as the training images. While making the database brochure, the captured images are applied and cropped by face discovery module in order to gain the only facial corridor of all images with different directions For case, five images of a person with different face directions are shown in figure 12.
All training images are reshaped and converted into 125x125 argentine scale images by using resize and rgb2graymatlab erected-infunction. Mean centered (or abated) images are estimated by abating average image from the original training image. The eigenvectors corresponding to the covariance matrix define the Eigen faces which look like ghostly faces. Since 50 training images are used, 50 eigen faces are obtained. Some eigen faces of the training images are shown in figure 16
The trained and test images are projected onto the face space where the eigen faces are the coordinates or confines to find their separate euclidian distance. By comparing the euclidian distance of all projected trained images with the projected test image, minimum distance between them which shows similarity to test image is attained. By this mode, the facial image gratitude was done. .
VI. SIMULATION TESTS AND RESULTS
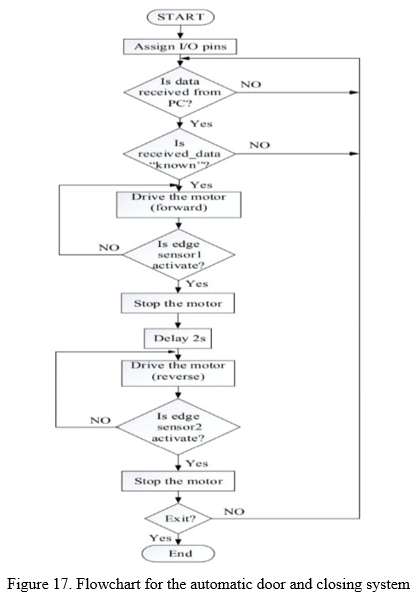
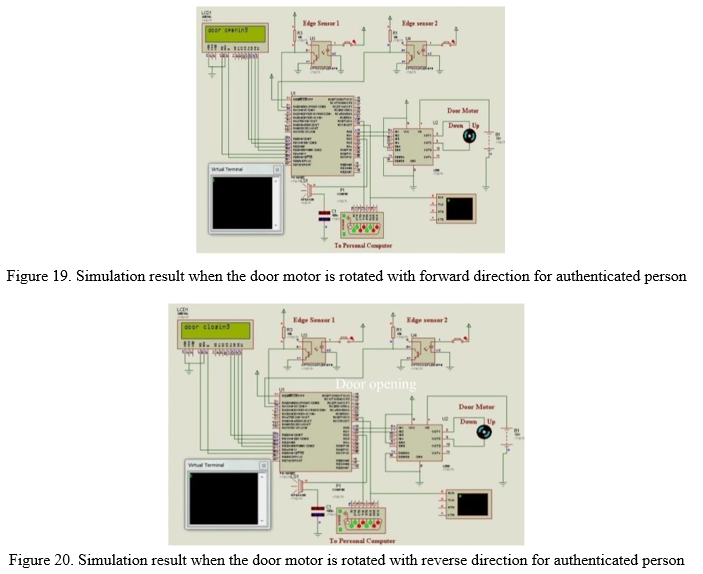
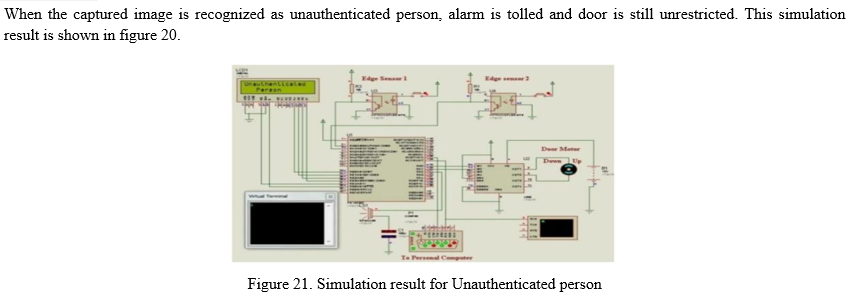
The overall automatic door access system using face recognition is dissembled by using PROTEUS software and MATLAB. VSPE software is used to produce a virtual journal communication harborage. A MATLAB GUI is created in order to perform automatic face discovery and recognition. There are two cases in this system. The first is automatic door opening for the honored person and the second is ringing the alarm for the unauthenticated person. In this scheme, input images are taken finished a web camera continuously until the‘ stop camera’ button is pressed. Figure 15 shows the MATLAB GUI affect when captured face is detected and recognized as authenticated person.

When the seized image is documented as the genuine. person, door motor is alternated with the onward direction until the edge sensor 1 is actuated. When the sensor 1 is actuated, the door motor is stopped. After 2 seconds, door motor is rotated with hinder direction until edge sensor 2 is Actuated. Figure 19 and 20 show the simulation result for authenticated person.
VII. HARDWARE RESULTS
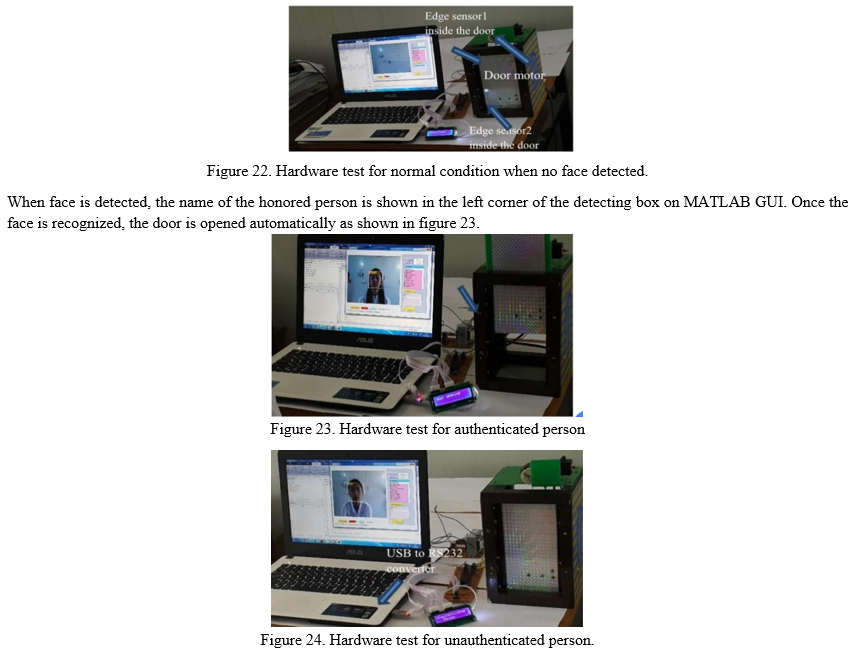
To perform involuntary door access system, specific computer (PC) is associated with the microcontroller via USB to RS232 motor. When no face is detected in front of the webcam, any signal is not transferred to the microcontroller. Since microcontroller is not entered any signal from PC, the door remains unrestricted. This circumstance is shown in figure 22.
VIII. ACKNOWLEDGEMENT
Authors would like to take this occasion to extend her deepest gratefulness to their companion Prof. Harish Gorewar, for his all round support, stimulant, guidance during the period of her design with a keen interest, enthusiam, vigor and his ever- helping nature from the starting of the design till the completion of this report/synopsis. It's all because of his unflagging trials, suitable guidance and precious suggestion, that could attend my effortsin covering the numerous different features of the design and therefore helped me for the smooth progress and success of design. Author indebeted to him for the precious time he has spared for me during thiswork. Authors would also like to thank Head Of Department Dr.S.P.khandait for furnishing the excellent installations which. she can noway forget their unconditional support and stimulant to pursue her interest. This acknowledgement would not be complete without expressing my particular belief in and gratefulness towards the almighty God. Author Thank God for carry her through this involvement to her the magnificence.
Conclusion
This face recognition system isn\'t 100 accurate, but it works well in good light conditions. The problem is it can also descry faces from filmland for case, someone can unleash it by showing your picture from his mobile phone. We can ameliorate this by training our own waterfall classifier., Face recognition grounded door locking has been developed to give better security. It\'s stoner friendly system. The use of Eigen face recognition fashion makes system more secure. This system can be used in several places where high security is needed where nonpublic information and outfit is kept. For illustration, exploration institutes, banks, forensic Laboratories. This system can also be used for national purposes. This design helps to reduce problem of thefts and frauds. In case of unauthorized person\'s entry, system cautions authorized person with SMS and at the same time the buzzer beeps to warn people. This is a cost effective and dependable door locking system. In this paper we\'ve enforced a face recognition door cinch system. Feting of faces is done by using waterfall classifiers, which gets a high delicacy and will store in the database. For this testing, we\'ve used 40 images only. Computer vision is used in the IOT. For security purpose, we\'ve enforced real time face discovery by Haar classifier. Therefore this system can useful for elderly citizens living alone and for mustered people. Hence the proposed system is virtually easy to construct and easy to track the path.
References
[1] Y. Januzaj, A. Luma, Y. Januzaj, V. Ramaj., \"Real time access control based on face recognition,\" in International Conference on Network Security Computer Science (-15), pp. 7-12, 2015 . [2] M. Sahani, C. Nanda, A. K. Sahu, B.Pattnaik., \"Home security system based on face recognition,\" 2015 Int.Conf.Circuits, Power Comput. Technol. (ICCPCT-2015), pp. 1-6, 2015. [3] G. Senthilkumar, K. Gopala krishnan, V. S. Kumar., \"Embedded image capturing system using raspberry pi system,\" vol. 3, No. 2, pp. 213-215, 2014 [4] M. R. Mulla., \"Facial image based security system using PCA,\'pp. 548-553, 2015. [5] M. H. Jusoh & F. Bin Jamali, \"Home security system using internet of things,\" 2017. [6] S. S. Liew, M. Khalil-Hani, S. Ahmad Radzi,R.Bakhteri., \"Gender classification: A convolutional neural network approach,\" Turkish J. Electr. Eng. Comput. Sci., vol. 24, No. 3, pp. 1248-1264, 2016. [7] M.Sajjad et al., \"Raspberry pi assisted face recognition framework for enhanced law-enforcement services in smart cities,\" Futur. Gener. Comput. Syst., 2017. [8] A. R.Syafeeza, S. S. Liew, R. Bakhteri., \"Convolutional neural networks with fused layers applied to face recognition,\" Int. J. Comput. Intell. Appl., vol. 14, No. 3, 2015. [9] A.R.Syafeeza, M. Khalil-Hani, S. S. Liew, R.Bakhteri.,\"Convolutional neural network for face recognition With pose and illumination variation,\" Int. J.Eng. Technol., Vol. 6, No. 1, pp. 44-57, 2014 [10] K.Syazana-Itqan, A. R. Syafeeza, N. M. Saad, N. A. Hamid, W.H. Bin Mohd Saad., \"A review of finger-vein biometrics identification approaches,\" Indian J. Sci. Technol., vol. 9, No.32, 2016. [11] Mahender K, Kumar TA and Ramesh KS PAPR 2018 analysis of fifth generation multiple access waveforms for advanced wireless communication, International Journal of Engineering and Technology (UAE), 7(3.34 Special Issue 34) 487-490 10.2147/NBHIV.S68956_old [12] Swathi N, Padmaja Ch and Navya Jyothi G 2020 Audio assistive for blind people to identify the cloth patterns and colors Journal of Critical Reviews, 7(17) 154-158 10.31838/jcr.07.17.2 [13] Sourav Roy; Md Nasir Uddin; Md Zahirul Haque; Md Jahidul Kabir, “Design and Implementation of the Smart Door Lock System with Face Recognition Method Using the Linux Platform Raspberry Pi”, by IJCSN - International Journal of Computer Science and Network, 7(6), [14] I. Aydin and N. A. Othman, \"A new IoT combined face detection of people by using computer Vision for security application,\" International Artificial Intelligence and Data Processing Symposium (IDAP), Malatya, 2017, pp. 1-6, doi: 10.1109/IDAP.2017.8090171.ecember 2018 [15] Mohammadjaved R. Mulla; Rohita P. Patil; S. K. Shah 2015.Facial Image Based Security System using PCA. [16] P. Bhatia, S. Rajput, S. Pathak and S. Prasad, \"IOT based facial recognition system for homeSecurity using LBPH algorithm,\" 2018 3rd International Conference on Inventive Computation Technologies (ICICT), Coimbatore, India, 2018, pp. 191-193, doi: 10. [17] Ishaan Sathe, Chiman Patel,(April-2017) Prasad Mahajan, Tanmay Telang, Sejal Shah,Automatic Locking Door Using Face Recognition. International Journal of Engineering Technology Science and R [18] Nadafa, Raju A., et al. “Home Security against Human Intrusion Using Raspberry Pi.” Procedia Computer Science, 167, 2020, pp. 181120. DOI. or (Crossref), doi: 10.016/ j.procs. 2020.03.200esearch(IRJET).Volume 4, Issue 4.ISSN 2394 –3386.http://www.ijetsr.com/ [19] Dipesh Vaya1, Teena Hadpawat2, (Feb- 2018).pca based efficient face recognition technique.International Journal For Technological Research In Engineering.ISSN (Online): 2347 – 4718 [20] Arti Barde1, Swapnil Bilbile2, Shubham waghmare3, Prof. J. D. Dorve4,(Feb-2018).review on door bell notify with image capture and forward through email. International Research Journal of Engineering and Technology (IRJET).Volume: 05 Issue: 02.e-ISSN: 2395-0056,p-ISSN: 2395-0072. https://www.irjet.net/
Copyright
Copyright © 2022 Asmita Nagpure, Mayuri Sonule, Surja Chauhan, Shreya Bhowate, Kunal Meshram, Prof. H. V. Gorewar. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET42183
Publish Date : 2022-05-03
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

