Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Cloud-Based System for Identifying Vaccinated Individual
Authors: Ankesh Raj, Mohd Tajammul
DOI Link: https://doi.org/10.22214/ijraset.2022.41237
Certificate: View Certificate
Abstract
In Covid\'s predicament Many colleges, companies, healthcare facilities, and universities have only permitted students who have obtained vaccinations, as required by Indian government regulations. Even so, checking all of the pupils\' covid vaccinations one by one will take a long time, needing more than two or three employees. As a result, the project\'s mission is to support the institution by delivering an automated status that shows whether or not student has been vaccinated[30]. Organizations will use a web app to collect information on the immunisation status of students and workers. Students or staff members will be required to input their name, phone number, USN number, and whether or not they have indeed been vaccinated, as well as a backend end for face recognition in raspberry pi with a camera and database as MYSQL database. Abstract.
Introduction
I. INTRODUCTION
Personal staff are required to have a relevant system for authorising and successfully managing the history of attendance record on a regularly in order to authenticate whether such a person or staff participant of the institution or firm has been vaccinated or not. Two sorts of frameworks that may be utilised for this are the Conventional based Verification System (CVS) or Manually based Verification System (MVS), as well as the Automated Verification System (AVS) (AVS). If we use MVS, the member of staff would find it extremely difficult to Make note of and save all verification records for all students and employees throughout all times. [6]. When there are a huge number of staff or students in a workplace or college, seeing each individual gather their covid reports and preserve their records every time they visit the school or office becomes a highly tedious, dull, and uninteresting task., and there is a considerable chance of human mistakes. Their accuracy will also be low, therefore we may use them to defend our system, process, or system. With the help of Human Facial Recognition, our upcoming framework will identify the person and determine whether he or she has been vaccinated. If the individual has been vaccinated, the system will allow the individual and will also label the logging time in which the employee comes into to the office and for a student for their attendance (HMR). In most cases, this system featured an image of all of the employees/students who were involved in the HMR, regardless of whether they had been vaccinated or not. To deal with the HFR system, we'll use two separate methodologies: the first is a feature-based approach, and the second is a brightness-based technique. The computation part of this process enclosed some of the portions of the image provided into the framework that were taken into the structure up, and the next is feature-based methodology, that also makes advantage of unique characteristics of the face, such as that of the eye, nose, mouth, and other special features, and thus the arithmetic part of this procedure covered some of the segments of the photo provided into the system that had been taken into the structure up, and the next is feature-based technique, which uses special features introduce on the face, in which we must combine and integrate all segments of the It is also described as a holistic-based or image-based approach, and it is a type of technique that uses special features found on the face such as the eyes, nose, and chin. Because any and every picture is carefully considered and should be analysed, inspected, and examined using the Brightness-based methodology, it took longer to finish and became more complicated [6]. To make the procedure proceed as smoothly as possible, the image must be transformed into an indisputable object. model
II. PROPOSED STATEMENT
The purpose of the system is to establish a highly efficient consumer system that can help identify or recognise whether or not a particular individual has been vaccinated, and that may be accessed from any location on the globe .. All of the approaches discussed on this site are automated utilising multiple kinds of AWS cloud services. It's simply expandable and reachable from everywhere.. In our current article, we have been using high-level algorithms such as PCA and Face detection and recognition identification using LDA might be as accurate as 93 percent. AWS recognition, AWS S3 bucket, AWS lambda, AWS ec2 instance, and AWS SES are among the services that have been implemented. The suggested system's main goal is to evaluate the existing system, which is the covid-19 report detection technique. To develop a more advanced and effective method for detecting Covid-19 reports. To teach and practise an advanced method for the covid-19 identifying assessment. report.
III. SYSTEM DESIGN
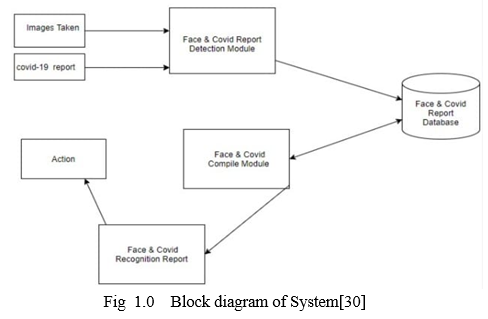
In the preceding proposal, the client must enter his or her information into a web portal provided by the firm. As illustrated in the diagram, our procedure consists of four parts. fig. 1.0 [30]
A. Creating a Database
In the above proposal, the client must provide information such as their name, roll number, recent photo, and two options for whether they are vaccinated or not. In the second option, the user must choose between these two options and provide a yes or no answer, as well as their covid-19 vaccinated report, Databased would save all this information in a Mysql. The application will require a photo of both the student, as well as a covid report if the student has indeed been vaccinated.. For security reasons, they will be instructed to write their covid report no, so that no other report will have two covid reports on it.
???????B. Face Detection
We utilized a technique called as Haar-Cascade Classifier with AWS recognition and Open cv for face identification in this work. This algorithm is necessary to teach for recognizing human face identification so that it may be utilized earlier for human facial detection, which is known as feature extraction the instructing data used in this algorithm is an XML file-haarcascade_ frontalface_ default [2]. We'll use the detect Multiscale module from OpenCV in this system [which we'll get from open cv][3]. There are three main categories of elements to think about, including flow scale. Factor, minNeighbors, and reduction are all terms that might be used to describe anything. The image scale feature is used to figure out how much the picture size should be shrunk in each tiny image scale. Neighbors define that each rectangle neighbor can have extremely high-quality values. They generally obtain a certain face, but they can see the quality in the image. min The size of an item determines its minimal size. The mechanism operates automatically. is turned off (30,30) [2].
???????C. Face Recognition
The command data and the human face viewer are the two elements of face recognition. Instructions data is gathered from an existing picture production database, such as Amazon Rekognition's Image Rekognition API, which allows users to see images online. In[9].We can quickly recognise objects, people, text, scenes, and functions in photos with the assistance of Amazon Rekognition, and it also has facial research and face search skills which can be used to locate, evaluate, and compare faces to verify user, persons, computations, and situations of public safety usage.. The lambda function is triggered with the submitted picture and covid-19 report to direct the images to a dedicated Amazon Rekognition collections for archiving, and the same function is put in Mysql as index-based metadata alongside data within Mysql to trigger the email. that the student has submitted the form [8].
???????D. Entry of the staff
During this procedure, any staff or student is permitted to peek up into the campus camera. It will then be mirrored with a face in the dataset, which will trigger the second part of the process, which is facial recognition. If the person is allowed, it will display in next system that the individual is permitted to enter the college, as well as updating the data in the authorised column in the MySQL database.
IV. LITERATURE REVIEW
In [3], The author has recommended Paradigm as the default presence system. Face recognition and radio frequency identification (RFID) were used to illustrate how credentialed students and enumerators might be identified as they entered and exited the classroom. The Paradigm saves the information of each enrolled student. The programme also keeps track of each student's attendance in a certain topic and populates the attendance record with the relevant information. In [4] describes how the authors discovered, created, and deployed iris-based biometrics-based travel systems. Initially, attendees were asked to register their personal information as well as their unique iris template. A robot system photographed each eye of those in attendance who were viewing and pointing their iris, as well as doing similar searches in the built area, during the event. A web-based prototype was included. We'll have to look at a different type of topics in this article. In [5]The authors presented a visual perception-based presence system. The system was operated using a different algorithm, incorporating Viola-Jones features, the Histogram of Oriented Gradients (HOG), and the vector Machine (SVM) section. The authors evaluated a wide range of real scenarios, including measurement, brightness, closure, and condition. The MATLAB GUI has been used to begin and execute volumes analysis, PSNR (Peak Signal to Noise Ratio) data was used. The researchers demonstrated an appearance system based on visual perception In [6]. The system was controlled by algorithms such as Viola-Jones features, the Histogram of Oriented Gradients (HOG), and the SVM section. The writers looked at real-world scenarios such as measurement, brightness, closure, and condition. The MATLAB GUI was used to start and finish the volume analysis, which was based on Peak Signal to Noise Ratio (PSNR) data. In this application, the student's connected face qualities were eliminated, and the Radial Basis Function (RBF) was used to detect facial features. . The method was able to reach an accuracy of up to 82 percent. In [7]
The writers of this work have discussed the growth and development of facial recognition, normalization, facial recognition, and emotional networks were all examined in the field of technology they had employed. Face recognition is done using History of Oriented Gradients, face alignment is utilized for landmarks, face extensions are done using Convolutional Neural Networks, According to the authors, anchoring is produced afterward when. Regardless of the fact, their algorithm made a small percentage of inaccurate predictions, researchers were able to achieve a predictive performance of over 95%.
The author of [1] aims to develop a system for creating an automated attendance monitoring system for students in a class utilising facial recognition techniques such as Eigenface values, Principle Component Analysis (PCA), and the Convolutional Neural Network (CNN) The article explained what it is (PCA) as well as the Convolution Neural Network and its real-time existence algorithm in this study. The author of this work meant a system in which a person's face is found in a live broadcast of a student campus and its existence is noted if the facial expressions observed on their faces are in this instance described in four steps.. The author of [11] has devised a way of Max-Margin Face Detection (MMFD) methodology using face detection, and the model is educated using the Inception-V3 CNN method of recognizing students, and they have learned accuracy of up to 97.6 percent using TensorFlow in their study However because the experiment only lasted until the 20th, the accuracy may vary if we use larger data In [12], the author proposes an image processing-based implant system for accessing patient health information via facial recognition. Instead of a unique ID number, face recognition is employed. A Raspberry Pi 3 CPU and a webcam are used in this software to take images. It also employs two distinct algorithms: the Local Binary Pattern and the HAAR Cascade Algorithm In[13] The authors of this study have devised a system for content-based picture retrieval that can be used in a big image gallery desktop application to allow fast browsing with the aid of two independent search processes: found significant based on image and text or ticket retrieval. This application is linked with MPEG-7, and the Edge Directivity Descriptor is applied to eliminate the characteristic of a set of vectors for a certain image from the image database. In [15-20], The writers have provided numerous concepts of cloud computing as well as security procedures. In[10] The author of this research built a system that employs Image Processing methods and an automated travel system to systematically determine student attendance by recognising their faces. When an unknown face is spotted within the classroom, the system recognises it as an invader and saves it, and the author explored methods like Viola-Jones and Local Binary Patterns of Histograms (LBPH). In [14]
The author of this research proposed a system in which AWS DeepLens, a machine learning device, would execute deep learning for AI-trained modules. can distinguish between normal and abnormal The device's output will provide user sound with face expression information. The success of the system Deep learning algorithm is assessed in a confusion matrix, with an average rate of 76,16 percent throughout the task. In [21] The study uses Image Processing techniques to automatically construct a presence system in which the existence of students is recorded by their faces. archived Their objective, utilizing the Viola-Jones method and LBPH, will be to use deep learning in image processing and obtain more accurate results for a greater number of students in the future work of this paper.
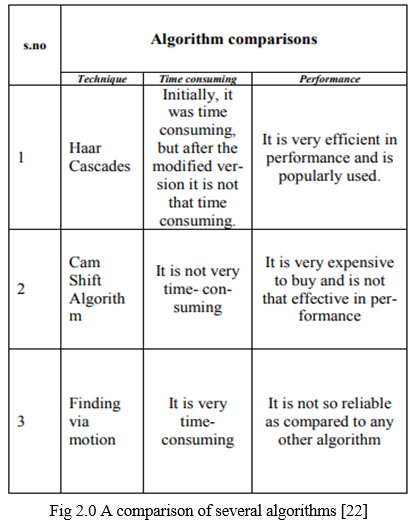
The proposed system is limited in [23] to a user-friendly institutional level application that exists in a three-layered hierarchical structure for having role-based access that is Admin level, Level of Intelligence / Staff, and student level algorithm used in this Viola-Jones Algorithm and Key Component Analysis (PCA). The entire method is compared in terms of space and time paradigm in [22]. By using open cv and MATLAB, Haar cascades are identified as the most effective approach to detect faces and differences in facial recognition. The advantages and disadvantages of both systems are examined. as well as the drawbacks of certain algorithms as well as its efficiency
The many types of algorithms discussed in this study include flow-based algorithms .are as flow -
In [24] In this example, the author attempted to utilise Haar Classifier with Raspberry Pi BCM2835 CPU processor, a combination of SoC and GPU based on its Architecture, to perform Real-Time Face identification and head tracking from high-definition video. Face detection and head tracking are accomplished using the SimpleCV and OpenCV packages. Results of computer-assisted testing utilising computer vision Simple CV and OpenCV draught libraries, as well as above computer programme results obtained at 30 frames per second under 1080p resolutions, demonstrating your great efficiency, accuracy, and speed in face identification and head tracking. In [25] this research, a board algorithm is used to implement a semantic search engine, which is a cloud - based platform that employs semantic technology to extract relevant user data and explains semantic analysis and Big Data correlations and processing performance.
In [26] In this research, the author developed a homomorphic encryption mechanism that provides integrity of data against selected plain text on cloud data. Homomorphic cryptographic algorithms have the property of performing tasks on encrypted data while saving time by not only decrypting the encrypted data each time. In this execution, the Paillier algorithm, which is a stochastic algorithm, was also used to meet the goals of data ensuring the integrity.
The author of [27] was aiming for system types that use two coding methods: detection and face recognition using the Haar Based Cascade separator as well as recognition using Principle Component Analysis. It is built on Deep-Learning Concepts and the DLIB application algorithm, and it is capable of providing 95 percent accuracy on a specific user photo. It can identify people even if their haircuts have changed. The database includes a variety of different faces that can be identified.
In[28] In this paper, we propose to use composite features based on the Viola-Jones algorithm to improve the aforementioned problems, and we demonstrate the feasibility of this technique through experimentations, as well as a process by which the face image is processed through a face detection based on the Viola-Jones algorithm using composite features to ensure that the face recognition rate is not harmed and a certain degree of detectability is maintained..
In [29] The author of this research wanted to create a system that uses a YOLO network to recognise faces. The YOLO identification technology is utilised to recognise a person's face in this software. The test findings revealed that the YOLO-based facial identification system was strong, durable, and had a fast visual acuity. Nonetheless. Simultaneously, acquisition speed can match real-time acquisition needs.
In[30] in this the author has given explained process verifying a vaccinated people with the help of cloud computing
V. IMPLZMENTATION
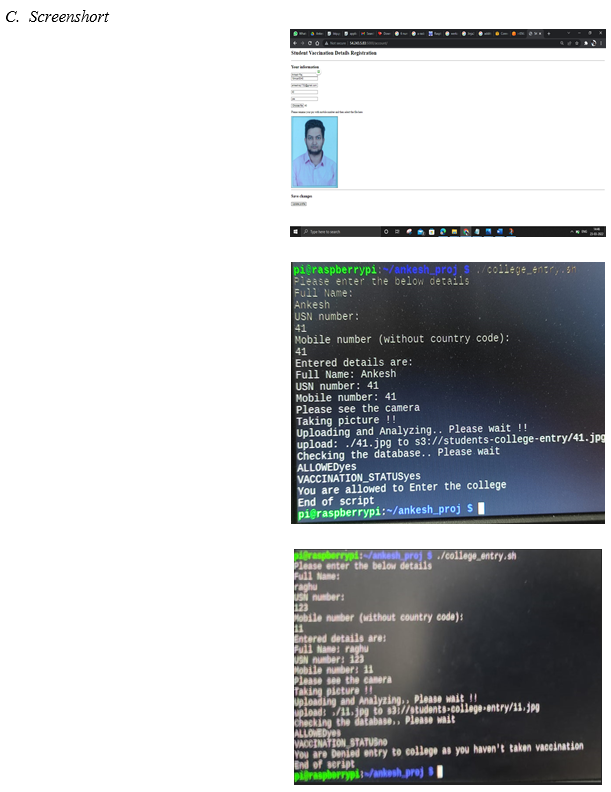
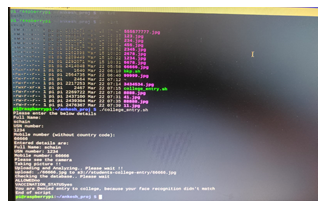
In this project we had use two types of frame work that is Front end in which the user data will be collected and will be submitted on student reg bucket and then it will called create index face in Aws lambda function and with the help of it with we had use a another types of lambda called as search face which will use to search the face whether the person face is matched or not if it is not matched it will give a message the that person doesn’t matched and if the person told that the person told that if he had not taken a vaccinated it will also not allowed him the searching part will search for face id which is generated at the time of image given by the student.
It is important to note that phone number should same as the image name as we had taken the phone number as prime number and college part is done by another function of lambda called as college entry .
???????A. Algorithm
- Step-1 in the first step we will be create a frontend in which the user will add their data and their data will be saved in college registration
- Step-2 in this step will be creating a database in which we will store the data for this I had use MySQL server
- Step-3 In this step we had created four different function as create_collectionID, create_indexfaces, search faces and test_mail in phyton in Aws lambda
- Step-4 The create_collectionID is used for only ones a time for creating a collection which helps in trigging the create_indexfaces which is responsible for the creation of the face id which is done with the use of another feature as Amazon Rekognition.
- Step-5 In this step the face id along with the user basic information will be uploaded and then a mail will be send to the admin the that which student has register themselves this ids done with the help of AWS SES service present inside the AWS
- Step-6 In this step when a student comes to college he had to see his face on camera and their the search faces of lambda will work to verify whether he is allowed or not if not the system will tell that this student is not allowed to come in the college as his face doesn’t matched or he had not taken vaccinated .
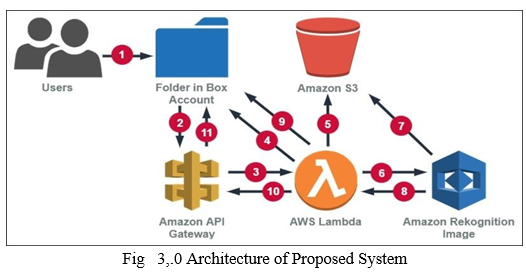
???????B. Architecture Of Proposed System
The flow of our program will follow from the front end which we had make in which we had make with the help of flask,Jinja2, Werkzeug will be create a frontend in which the user will add their data and their data will be saved in college registration of AWS s3 bucket then will be creating a database in which we will store the data for this I had use MySQL server and connect with s3 bucket we had created three bucket reg-pic-bucket,student-reg-covid-bucket,student college entry we had also createdfour different function as create_collectionID, create_indexfaces, search faces and test_mail in phyton in Aws lambdaThe create_collectionID is used for only ones a time for creating a collection which helps in trigging the create_indexfaces which is responsible for the creation of the face id which is done with the use of another feature as Amazon Rekognition.
After that the face id along with the user basic information will be uploaded and then a mail will be send to the admin the that which student has register themselves this ids done with the help of AWS SES service present inside the AWS all of this process happen automatically when a user uploaded its information when the student or employee come to college he had to see his face on camera and their the search faces of lambda will work to verify whether he is allowed or not if not the system will tell that this student is not allowed to come in the college as his face doesn’t matched or he had not taken vaccinated .
VI. FUTURE SCOPE
This project's future scope is that it may be upgraded with new types of algorithms, such as PCA and LDA hybrid algorithms. Our future research will focus on using deep learning in image processing to produce more accurate results for a greater number of students. We believe that our findings will make colleges more concerned about student safety in the classroom and attendance automation. This system may be extended and enhanced so that it can be used in multi-national firms to keep track of a much larger database that contains a large number of entries from people working for a certain company. This will be beneficial in terms of preserving security.
Conclusion
We successfully implemented a software system that will identify whether or not people have been vaccinated. Our paper demonstrates that it can help replace manual methods of identifying people with greater accuracy and efficiency. In this paper, we have some AWS features such as Aws rekognition, ,AWS S3 bucket Aws Lambda, Aws EC2 instance and Aws SES.,
References
[1] Sawhney, S., Kacker, K., Jain, S., Singh, S. N., & Garg, R. \"Real-time smart attendance system using face recognition techniques\", 2019 , 9th International Conference on Cloud Computing, Data Science & Engineering (Confluence),IEEE,522-525 [2] Smitha, Pavithra S Hegde, Afshin Face Recognition based Attendance Management System,2020, International Journal of Engineering Research & Technology (IJERT),vol-05 ,1190-1192 [3] Akbar, M. S., Sarker, P., Mansoor, A. T., Al Ashray, A. M., & Uddin, J \"Face Recognition and RFID Verified Attendance System.\" 2018, In International Conference on Computing, Electronics & Communications Engineering (iCCECE). IEEE, 168-172 [4] Okokpujie, K. O., Noma-Osaghae, E., Okesola, O. J., John, S. N., & Robert, O \"Design and implementation of a student attendance system using iris biometric recognition.\" ,2017 ,In International Conference on Computational Science and Computational Intelligence (CSCI). IEEE, 563-567 [5] Rathod, Hemantkumar, et al. \"Automated attendance system using machine learning approach.\" 2017 ,In International Conference on Nascent Technologies in Engineering (ICNTE). IEEE, 1-5 [6] Lukas, S., Mitra, A. R., Desanti, R. I., & Krisnadi, D “Student attendance system in classroom using face recognition technique.,2016, International Conference on Information and Communication Technology Convergence (ICTC) , IEEE,1032-1035 [7] N. M. Ara, N. S. Simul and M. S. Islam, \"Convolutional Neural Network Approach for Vision Based Student Recognition System,\" 2017 ,In 20th International Conference of Computer and Information Technology (ICCIT), IEE ,1-6 [8] https://aws.amazon.com/blogs/developer/authenticate-applications-through-facial-recognition-with-amazon-cognito-and-amazon-rekognition/ [9] https://aws.amazon.com/rekognition/image-features/ [10] Shrestha, R., Pradhan, S. M., Karn, R., & Shrestha, S \"Attendance and security assurance using image processing 2018, Second International Conference on Computing Methodologies and Communication (ICCMC) 548-588 [11] Sujit Kumar Gupta, Ashwin T S, Ram Mohana and Reddy Guddeti “CVUCAMS: Computer Vision based Unobtrusive Classroom Attendance Management System”, 2018,In 18th International Conference on Advanced Learning Technologies IEE ,101-102 [12] S.Jayanthy1 , J.B.Anishkka2 , A.Deepthi3 ,.Janani “Facial Recognition And Verification System For Accessing Patient Health Records” 2019 ,Proceedings of the International Conference on Intelligent Computing and Control Systems ,IEE ,1266-1271 [13] Meenaakshi N. Munjal and Shaveta Bhatia \"A novel technique for effective image gallery search using content based image retrieval system.\"2019, In 2019 International Conference on Machine Learning, Big Data, Cloud and Parallel Computing (COMITCon),IEE,25-29 [14] Rafael, G., & Kusuma, H. (2020, November). . \"The Utilization of Cloud Computing for Facial Expression Recognition using Amazon Web Services.” 2020 International Conference on Computer Engineering, Network, and Intelligent Multimedia (CENIM) ,IEEE.366-370 [15] Tajammul, M., Parveen, R., & Tayubi, I. A. (2021, March). Comparative Analysis of Security Algorithms used in Cloud Computing. In 2021 8th International Conference on Computing for Sustainable Global Development (INDIACom) (pp. 875-880). IEEE. [16] Tajammul, M., Shaw, R. N., Ghosh, A., & Parveen, R. (2021). Error Detection Algorithm for Cloud Outsourced Big Data. In Advances in Applications of Data-Driven Computing (pp. 105-116). Springer, Singapore. [17] Tajammul, M., & Parveen, R. (2020, December). To Carve out Private Cloud with Total Functionality. In 2020 2nd International Conference on Advances in Computing, Communication Control and Networking (ICACCCN) (pp. 831-835). IEEE. [18] Tajammul, M., & Parveen, R. (2020). Auto encryption algorithm for uploading data on cloud storage. International Journal of Information Technology, 12(3), 831-837. [19] Tajammul, M., & Parveen, R. (2019). Algorithm for Document Integrity Testing Pre Upload and Post Download from Cloud Storage. International Journal of Recent Technology in Engineering, 973-979. [20] Tajammul, M., & Parveen, R. (2019). Two pass multidimensional key generation and encryption algorithm for data storage security in cloud computing. International Journal of Recent Technology in Engineering. [21] Shrestha, R., Pradhan, S. M., Karn, R., & Shrestha, S. (2018, February). Attendance and security assurance using image processing. In 2018 Second International Conference on Computing Methodologies and Communication (ICCMC) (pp. 544-548). IEEE. [22] Goyal, K., Agarwal, K., & Kumar, R. (2017, April). Face detection and tracking: Using OpenCV. In 2017 International conference of Electronics, Communication and Aerospace Technology (ICECA) (Vol. 1, pp. 474-478). IEEE. [23] Sumita, C., Patange, M., Deshpande, H., Maredia, S., & Bagwe, P. (2016). A Prototype of Automated Attendance System Using Image Processing. International Journal of Adva nced Research in Computer and Communication Engineering, 5(4). [24] Kumbhar, P. Y., Attaullah, M., Dhere, S., & Hipparagi, S. (2017). Real time face detection and tracking using OpenCV. International journal for research in emerging science and technology, 4(4). [25] Das, N. N., Chowdhary, M., Luthra, R., & Garg, S. (2019, February). Semantic Big Data Searching in Cloud Storage. In 2019 International Conference on Machine Learning, Big Data, Cloud and Parallel Computing (COMITCon) (pp. 351-355). IEEE. [26] Sawant, S., & Devmane, V. (2017, August). Towards privacy preserving for dynamic data in cloud storage. In 2017 International Conference on Energy, Communication, Data Analytics and Soft Computing (ICECDS) (pp. 296-299). IEEE. [27] Patel, V. G., & Suthar, A. (2018). Human Face Detection and Tracking. International Journal of Computer Engineering & Technology, 9(4), 187-195. [28] Lu, W. Y., & Ming, Y. A. N. G. (2019, June). Face detection based on Viola-Jones algorithm applying composite features. In 2019 International Conference on Robots & Intelligent System (ICRIS) (pp. 82-85). IEEE. [29] Yang, W., & Jiachun, Z. (2018, July). Real-time face detection based on YOLO. In 2018 1st IEEE international conference on knowledge innovation and invention (ICKII) (pp. 221-224). IEEE. [30] Ankesh Raj, Dr. MohammedTajammul (2022-feb)Indetifying Vaccinated People System Using Cloud International Journal for Research in Applied Science & Engineering Technology (IJRASET) Volume 10 Issue II Feb 2022
Copyright
Copyright © 2022 Ankesh Raj, Mohd Tajammul. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET41237
Publish Date : 2022-04-05
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

