Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
A Brief Overview: Computer Network Based on Physical and Logical Topology
Authors: Muhammad Arif Bin Jalil
DOI Link: https://doi.org/10.22214/ijraset.2022.40833
Certificate: View Certificate
Abstract
The classification of network topologies according to how they are implemented is examined in depth from a variety of perspectives. Each type of topology is used to accomplish a certain purpose and capture the system\'s structure at varying levels of detail. Distributed computer systems have been an important and popular topic in computing in recent years. It provides high-end performance at an affordable price .In a distributed computing environment, autonomous computers are connected via a communication network that is arranged in a geometrical shape known as network topology.
Introduction
I. INTRODUCTION
Distributed computing systems have become a critical component of the rapidly evolving information technology and computer networking industries. The technology that we use to make network linkages and how data is communicated determines the performance of any distributed system. The technology for arranging various computer elements such as links, nodes, and so on is known as network topologies [1-2, 8-9].The topological structure [5] of a computer network is referred to as network topology. Topology is a branch of mathematics that deals with the connectedness of things, which is one of space's most fundamental features. The manner that a network of computers [5, 6-7] is connected is referred to as network topology. Each topology is optimised for various activities and has its own set of benefits and drawbacks. LAN [3-4, 8-9] is a very simple and good example of network topology, where the LAN has one or more physical connections to other network devices. Physical topologies [8-9] and logical topologies [8-9] are the two most common types of network topologies nowadays. The hardware involved with the system, such as workstations, remote terminals, servers, and the accompanying wiring between assets, is referred to as Physical Network Topology. Logical Network Topology, on the other hand, stresses the representation of data flow between nodes.
A. Data Communication.
Data communications have become so ingrained in our lives that we often take them for granted, Despite the fact that they are the foundation for much of what we do in the twenty-first century. Data communications are critical to a company's performance in the marketplace, especially with the growing trend toward globalisation. Individuals and teams can use communications networks to interact more quickly and effectively, eliminate the need for frequent in-person meetings, and even transfer payments online .Individual computers or workstations can be joined together to provide data sharing and communication via local, metropolitan, or wide area networks. Networks can also be joined together to better satisfy the organization's needs and the growing need for data and communication established by the use of either directed (wired) or wireless media. The transmission/exchange of digital data between a source and a receiver is referred to as data communication. Guided or wireless media are used to make a physical link between networked computing units. The Internet is the most well- known computer network.
When communicating devices are in the same building or a similar geographical area, data communication is said to be local. There are three different kinds of data communication networks .Local area networks, metropolitan area networks, and wide area networks are the three types. Multiple desktop computers that are close to one other and linked into a network that allows users to exchange data and peripheral devices such as printers, fax machines, and storage devices make up a local area network. The metropolitan area network is a second form of network that many firms use. This network sends data and information across the city (up to 30/40 miles) at higher speeds than a local area network. Metropolitan area networks, in contrast to local area networks, are geared for both voice and data transmissions, allowing them to carry more types of data than local area networks. These contain speech, data, picture, and video data in combination. Metropolitan area networks are usually connected through a city- wide fibre optic cable network. The wide area network is the third type of network. Multiple computers that are widely separated and linked into a network make up these networks. To connect the computers in a wide area network, high-speed long-distance communications networks or satellites are often used.
II. PHYSICAL TOPOLOGY
The hardware involved with the system, such as workstations, remote terminals, servers, and the accompanying wiring between assets, is referred to as Physical Network Topology.The physical topology of the systems determines how they are physically connected .It refers to the configuration of devices on a computer network using the real data-transmission connections. There are eight different types of topologies.
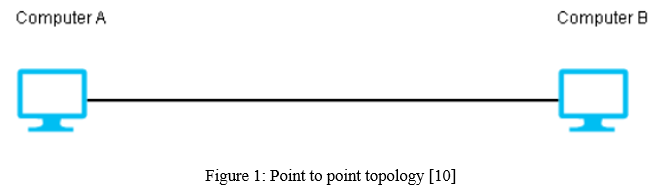
A. Point to point topology
The value of a permanent point-to-point network is unhindered communications between the two endpoints. A point-to-point topology is a direct link between two devices (nodes).A PC linked to a printer is one example of this. A mainframe terminal attached to a mainframe front-end processor is a more prevalent example.
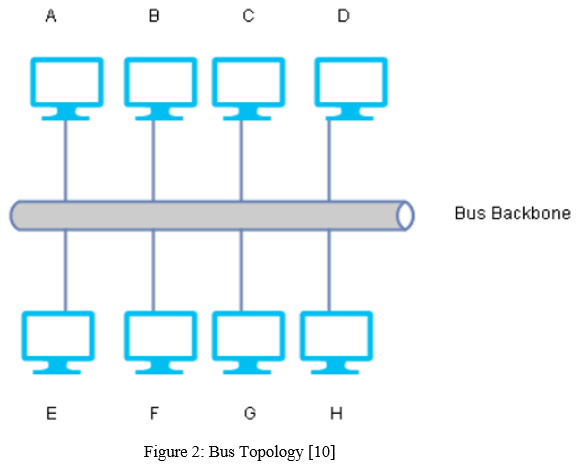
B. Bus topology
The transmitted message is carried over the cable by the bus topology. When a message arrives to a device (node), the node verifies the destination address to determine whether it matches its own. If the addresses do not match, the node does not do anything else. One of the key drawbacks of this network structure is that if the node address in the message matches the node address in the message, the message is processed by the node. The message is sent along the cable and is visible to any devices that are connected to it. Because data is disseminated over the network, there are security concerns, as well as the possibility of a single point of failure if the hub or backbone goes down.
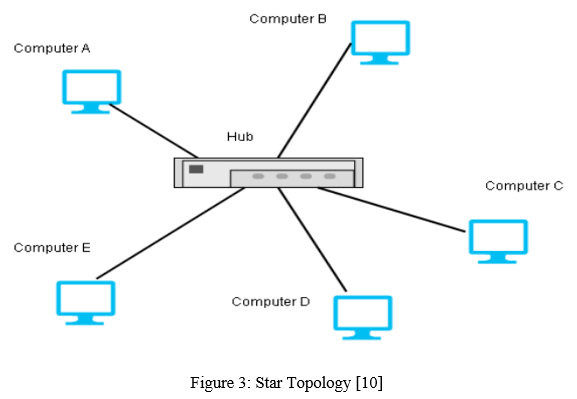
C. Star topology
Each of the devices or nodes on a network links to a central hub in a star topology, which is one of the most prevalent network configurations. The fact that if the central hub fails, all computers connected to it will be disconnected is a fundamental downside of this network structure. The system's strong reliance on the central hub's operation is a fundamental disadvantage of this network structure. The network becomes unusable if the central hub fails.
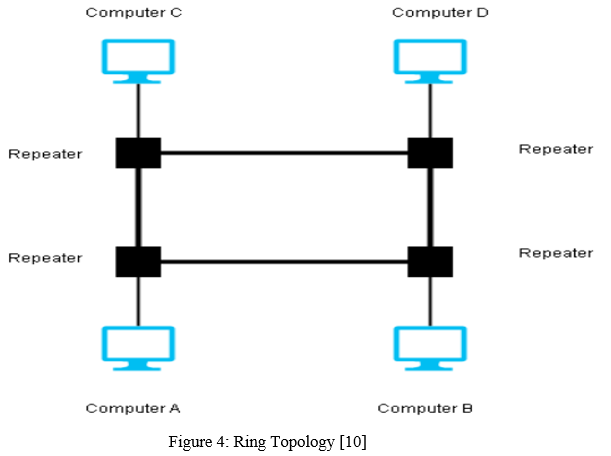
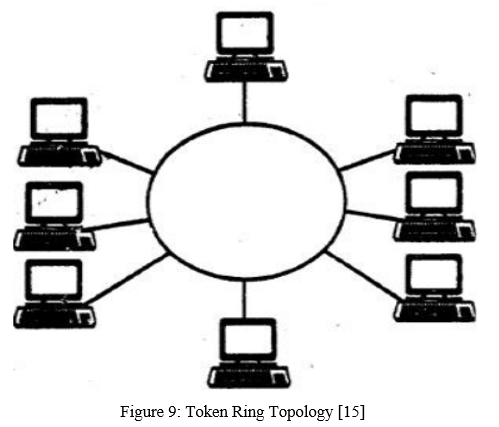
D. Ring Topology
The nodes or devices in a ring topology are all connected to one another in a circle. The data is passed from one device to the next, and so on, until it reaches the destination node. One significant downside is that if a single device is turned off, the network ceases to function.
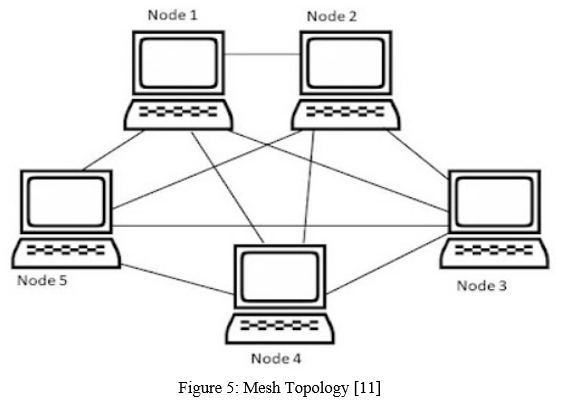
E. Mesh Topology
Each device in this topology is connected to the others, allowing most transmissions to be spread even if one of the connections fails. A key downside is the high likelihood of redundancy in many network connections, as well as the overall cost, which is excessively high when compared to other network topologies.
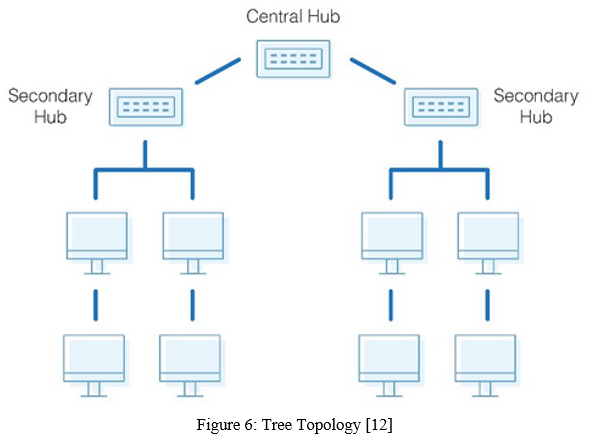
F. Tree Topology
When the network is dispersed and substantially separated into many branches, the Tree Structure works well. A tree topology is formed by connecting two or more buses and the Star Topology. Each star network is a local area network (LAN) in which all connected nodes are directly linked to a central computer or server. The star networks' central computers are linked by a major cable known as the bus. The length of the network is based on the type of cable used, and tree topology networks are fully reliant on the trunk, which serves as the network's fundamental backbone. If that fails, the network as a whole will fail.
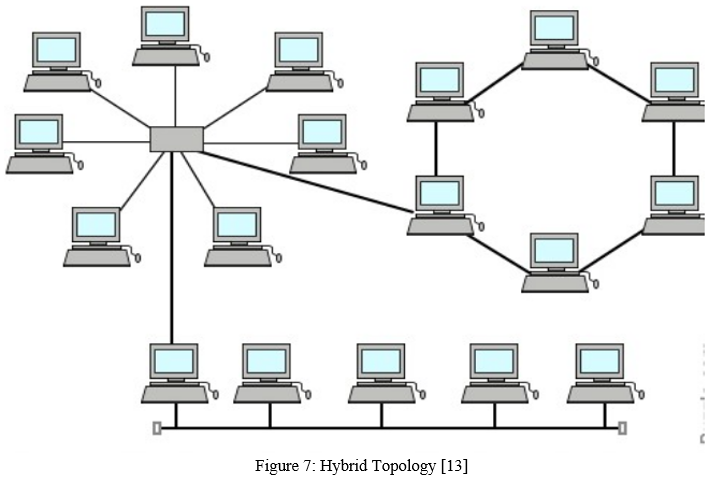
G. Hybrid Topology
A hybrid topology is a network topology made up of one or more interconnections between two or more networks with different physical topologies, or a type of network topology made up of one or more interconnections between two or more networks with the same physical topology, but where the physical topology of the network resulting from such an interconnection does not meet the definition of the original physical topology of the interconnection. Because it harnesses the properties of its component topologies, it is often more expensive than other networks. Other types of network topologies demand more cabling between their hardware units. Hybrid networks are challenging to set up and maintain.
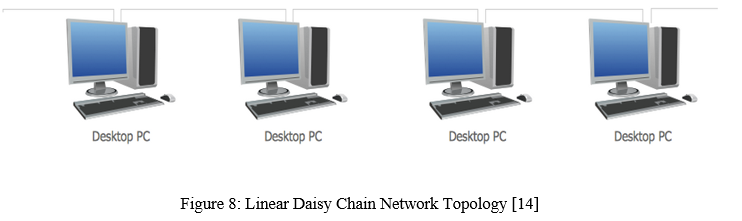
H. Daisy Chain
All of the devices are connected in a chain-like or ring way in a daisy-chained network configuration.The master controller communicates with a slave device, which communicates with yet another slave device, which communicates with yet another slave device, and so on.If a link in the ring fails, transmission can be routed over the reverse direction, ensuring that all nodes are always linked in the event of a single failure.A key disadvantage is that if a component or cable fails in the centre of the network, the entire network will be disabled, and if we wish to add a device in the middle of the chain or ring, the network will be down during the process. Because the cabling for these networks is typically installed in open areas, it is more susceptible to accidental disconnections and breakdowns.
III. LOGICAL TOPOLOGY
The representation of data flow between nodes is emphasised in logical network topology.The layout of devices on a computer network and how they communicate with one another is referred to as logical topology.The basic purpose of logical topology is to allow various systems to communicate across physical topologies.Shared media topology and token-based topology are the two types of logical topologies.
A. Shared Media Topology
The systems in a shared media topology have unrestricted access to the physical media, which means that any system in the network can access the physical layout whenever they need it. Collision is the fundamental downside of this topology because when multiple systems send data out across the cable at the same time, the packets collide and the packets are killed. A shared media topology is exemplified by Ethernet. As a result, several large networks have been divided into smaller ones. To limit the amount of collisions, certain ethernet uses the Carrier Sense Multiple Access protocol.
B. Token Based Topology.
In a token-based architecture, a token is used to access physical media and moves throughout the network. If a node wants to send a packet to another, it must first wait for the token, which travels clockwise or anti-clockwise around the network. After receiving the token, a node can transmit the packet to the network, and all nodes along the path from the sender node to the destination node, as well as all intermediate nodes, should validate the destination address, accept the packet, and generate an acknowledgement packet if it matches anyone. The acknowledgement packet should be sent in the opposite direction to inform the sender node that the packet has been received by the destination node.
Conclusion
This overview of computer network topologies for data communication provides a logical way for network engineers to learn about topologies and consider their properties and priorities as they engineer complex, large, and interdisciplinary systems of systems, with the goal of assisting in the design of data communication interconnection systems. The performance of various topologies is explored and studied in this paper. This paper also discusses some of the inherent benefits and drawbacks of computer network topologies for each system under consideration. This research has given some insight into analysis methods for dealing with network topology issues. The ideas discussed in this article can be used to a variety of computer network applications. As a result, we may deduce that there is a strong desire for study in this area, and it can be concluded that a standard topology is required to meet stakeholder expectations and to facilitate high-end data transmission in the construction of successful communication systems.
References
[1] Banerjee, S., Jain, V., Shah, S., \"Regular multihop logical topologies for lightwave networks\", Communications Surveys & Tutorials, IEEE, On page(s): 2 - 18 Volume: 2, Issue: 1, First Quarter 1999. [2] Cem Ersoy, Shivendra PanWar \"Topological Design of Interconnected LAN-MAN Networks\", IEEE INFOCO, pp. 2260- 2269, 1992. [3] F. Backes, ?Transparent Bridges for Interconnection of IEEE 802 LANs,? IEEE Network, pp. 5-9, January 1988. [4] Li Chiou Chen \"The Impact of Countermeasure Propagation on the Prevalence of Computer Viruses\" IEEE Transactions on Systems, MAN, and Cybernetics PartB; Cybernetics Volume 34, Number 2, pp. 823-833, April 2004. [5] Geon Yoon, Dae Hyun Kwan, Soon Chang Kwon, Yong Oon Park, Young Joon Lee \"Ring Topology-based Redundency Ethernet for Industrial Network\" SICE-ICASE International Joint Conference, pp. 1404 – 1407, 18-21 Oct. 2006. [6] Nicholas F. Maxemchuk, Ram Krishnan \"A Comparison of Linear and Mesh Technologies---DQDB and Manhattan Street Network\" IEEE Journal on Selected Areas in Communications, Volume 11, Number 8, October 1993. [7] Bannister, J.A., Fratta, L., Gerla, M., \"Topological design of the wavelength-division optical network\", INFOCOM, Ninth Annual Joint Conference of the IEEE Computer and Communication Societies. The Multiple Facets of Integration. Proceedings, IEEE, On page(s): 1005 - 1013 vol.3, 1990. [8] C. M. Harris, Fundamentals of Queueing Theory, Wiley Series in Probability and Statistics, John Wiley & Sons, Hoboken, NJ, USA, 4th edition, 2008. [9] D. Bertsekas and R. Gallager, Data Networks, 2nd ed. Englewood Cliffs,.NJ: Prentice-Hall, 1992. [10] https://notesformsc.org/network-topology/ [11] https://www.propatel.com/what-is-mesh-topology/ [12] https://www.dnsstuff.com/what-is-network-topology [13] http://generalnote.com/Computer-Network/Computer-Network-topologies/Hybrid-Topology.php [14] https://www.conceptdraw.com/How-To-Guide/daisy-chain-network-topology [15] https://ecomputernotes.com/computernetworkingnotes/computer-network/ring-topologies
Copyright
Copyright © 2022 Muhammad Arif Bin Jalil. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET40833
Publish Date : 2022-03-17
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

