Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Computer Vision based Surveillance System
Authors: Mrs. Naziya Farhat, Mohammad Nasiruddin
DOI Link: https://doi.org/10.22214/ijraset.2022.41512
Certificate: View Certificate
Abstract
Automated surveillance systems are surveillance systems that employ cameras to monitor the area. The observed setting is analyzed using motion detection, crowd behavior, individual behavior, and interactions between people, crowds, and their surroundings. These automated systems are capable of a wide range of tasks, including detection, interpretation, understanding, recording, and alert creation based on the results of the study. Researchers have been able to increase monitoring performance while limiting human errors by changing various features of these systems. This research looks into video surveillance systems and the components that go with them in depth. The designs that were used, as well as the most important studies in these systems, are presented. Existing surveillance systems were compared in terms of to provide a wider picture and a more holistic understanding of the system.
Introduction
I. INTRODUCTION
The term "security" refers to people's perceptions of environmental protection and means "without fear of harm." This research compiles technological breakthroughs in surveillance systems, applications, and key components into a single document, providing a literature assessment on the issue of security with an emphasis on autonomous surveillance. During our investigation, we discovered that deep learning is being utilised for surveillance, which opens up new research opportunities in an area that has seen minimal progress in the previous ten years, as well as the creation of new massive datasets to address security concerns. Surveillance and intrusion prevention has long been a bustling field. Since prehistoric times, security measures have been critical for mankind's safety and survival.. The use of them is limited because an operator is required to monitor the camera feed and make appropriate decisions. Camera-based surveillance has expanded beyond security to include tracking, environmental and threat assessments, and many more applications. It is possible to automate the procedure by utilizing the capabilities of contemporary computing and electronics. Using wireless receivers, we can monitor our signal and video feed. A surveillance camera is a type of security device that captures people's actions in order to identify, prevent, or investigate dangers to the public or criminal activity. It protects the public against dangers and aids in the investigation of crimes. It ensures public safety. Surveillance cameras are video cameras that are used to monitor a certain area continuously. Recording equipment and cameras are costly, and regular monitoring of video material necessitates people. Some automated software has made this easier. In comparison to traditional CCTV cameras, the suggested system includes more modern and successful features and functionalities. Its uses include preventing theft, weather monitoring, and property damage . We can simply integrate ESP-32 CAM , due to its low power absorption, tiny form factor, and inexpensive cost. In this circuit, we will first connect the cam to the WIFI and stream live video from the android device, after which we will be able to save images and movies with various elements . A local area network is used to operate the security camera. The Raspberry Pi is a credit card-sized computer with a cam and wireless data access that may be used as a security camera (Internet of Things). This strategy has grown more efficient and feasible for broad use with the introduction of machine learning, deep learning, and computer vision techniques. Instead of depending on people to monitor and generate insights, we might assign the task to a processor and machine learning system, which would be more efficient and error-free. If a crime occurs in a public location, higher authorities have a fair possibility of identifying the perpetrators using video recordings. If a person learns about the surveillance cameras installed in public areas, he may be less motivated to engage in unlawful activities. Security cameras, which record photos and give video footage, are the key evidence for the judicial system. Saved photographs and film aid in the speedier resolution of the case surveillance is described as the continuous observation of changing data or behavior patterns. It provides a sense of safety. Object recognition includes all computer vision-related tasks to identify physical objects in images or videos. Putting this into practice is a little more complex. However, we will see in the following that there are already simple ways to enable security cameras to recognize objects without human help. When it comes to video monitoring in public places, there are differing viewpoints. Those who dread an attack on their personal liberties on the one hand, yet do not want to be without security on the other. When firearms are used, this security is plainly jeopardised. However, this is not an easy task because firearms in video recordings are frequently difficult to identify. The image below is a snapshot from a movie that demonstrates how effectively Vision Apps in IP cameras have already mastered this. Similarly, feature extraction aids in the real-time detection and reporting of knives or clubs.
II. LITERATURE REVIEW
Various studies explain modern elements of surveillance, for example, [6], [7], which outline several important properties of surveillance systems that can be used to evaluate current systems. A set of common qualities for a surveillance system, as well as some of its uses, are listed below. Geriatric care and home hospitalisation are examples of home health care/home monitoring [8], [9]. These methods could include the use of monitoring systems to detect any anomalous behaviour in patients, as well as a more precise follow-up for those with conditions that require greater attention, such as Alzheimer's disease. It would save money on things like having a permanent nurse Intrusion detection: Detecting a person trespass-ing the property constraints would avail to take appropri-orally consumed actions such as calling the 911 emergency sys-tem, locking doors, or activating an audible alarm [10]-[11].· Animal Intrusion: Detect when a predator is on an urban property or rural, and determine if that specific animal needs a call to the police. The systems could have a list of local animals that re-quire to be reported to police departments, especially if they are predators, and this can avail the authorities to act afore any assailment occurs, incrementing the chances that the animal will survive, minimizing the human impact, and preserving people from an at-tack [1].·
Video surveillance protects both the corporation and the personnel at work. Installing a surveillance system inside or outside the workplace aids in the identification of thieves who steal or vandalise corporate property. They will be aided in their investigation and identification of the perpetrator by the camera footage Home assault: Detecting a person or group of people with the intention of assaulting a denizen of a house [8]-[9] and can avail the There is a growing need for user-friendly security solutions to preserve our privacy and secure our assets. It serves as a crime deterrent. The goal of this article is to design and build a surveillance camera with a Raspberry Pi 3, a Pi camera, a PIR sensor, and the Raspicam Remote programme. It is only utilised to record HD video if it detects motion in the monitored area, which is done via a PIR sensor. The motion in the monitored area is detected by a PIR sensor. When compared to existing conventional surveillance cameras, the suggested surveillance camera requires much less storage space.Dautov et al. [4] combine technology from the Internet of Things, the cloud, Edge Computing, and Big Data in an intelligent surveillance system, with a focus on data analysis generated by the system's sensors.[3] Shahad et al. [6] present an intelligent surveillance system that employs Complex Event Processing technology and is utilised to detect intrusions through data correlation. Furthermore, the engine employs four classifiers to forecast the occurrence of events based on the recognition of patterns in data sequences obtained from door sensors and security cameras. In Al-Nawashi et al. [7], an autonomous surveillance system for academic environments is proposed, which is based on video and capable of monitoring a scene in real time and detecting irregularities. Pre-processing, detection of abnormal human behaviour, and content-based image retrieval phase are the three modules of this system, which uses a support vector machine type classifier. The purpose of a visual surveillance system is to analyse and explain object behaviour. It includes of static and moving object detection, as well as video tracking to comprehend scene events. The primary goal of this research \ is to identify the many methods for detecting static and moving items, as well as tracking moving objects. Object detection techniques may be used to identify items in any video scene. Detected things include trees, clouds, people, and other moving objects, among others.
III. PROPOSED WORK
The following primary characteristics were identified within the algorithms evaluated within this group: people-oriented detection, identification of hidden objects, pose estimation, behaviour classification/action recognition, and facial recognition and identification. These issues are discussed in the sections below. Metrics for algorithms based on machine learning In this section, we look at how to measure the performance of several algorithms for people-oriented hidden object detection and identification, pose estimation, behaviour classification, and facial recognition and identification. In general, surveillance systems based on machine learning algorithms evaluate their performance based on the algorithms' capacity, therefore metrics that quantify their precision to categories, detect, and respond to the events to which you want the system to respond are employed in the evaluation. In the current context, object detection and tracking in surveillance systems is unavoidable, as it is impossible for a single human to continually examine video clips in real time. We present a method for recognizing moving objects in surveillance footage and predicting whether or not they are human. We employ a well-known Background Subtraction Algorithm known as Mixture of Gaussians to account for quicker object recognition. Support Vector Machine is given a collection of basic and efficient characteristics to work with. The system's performance is assessed using several SVM kernels as well as the K Nearest Neighbor Classifier's various distance measures. The ESP32 is a family of low-cost, low-power chips designed by Espressif Systems that succeeds the ESP8266 as the more powerful successor. The ESP32 is a dual-core device featuring WiFi and dual-mode Bluetooth connection that was released in 2016.
A 32-bit Tensilica Xtensa LX6 microprocessor running at 240 MHz and an ultra-low power co-processor are included in the microcontroller. The ESP32 module has 520KB of SRAM and can store programmes in 4- 6MB of external flash memory. The CPU is powered by 3.3VDC and supports WiFi 802.11 b/g/n, Bluetooth 4.2, and Bluetooth Low Energy. Power on the device with the FTDI cable or other power source, and the web server application will start. Connect to the ESP32-CAM web server by either joining the access point created by the device or finding the local IP address of the device, depending on how you configured the program. If you left the settings as default, the ESP32-CAM will create a WiFi network called “ESP32-CAM-CONNECT” with the password “InsecurePassword”. Once connected to the network, you can access the interface from http://192.168.4.1/. If the device has been configured to connect to your home network, the interface will be accessible from the ESP32-CAM's local IP address. The web interface offers simple and full modes. Simple mode only shows the live feed, while full mode allows you to configure various video settings and capture still images. You can control the integrated flash brightness and set it to auto using the interface. The resolution can also be selected which will impact the frame rate of the video stream. Various other options are available to adjust the image, including brightness, contrast, saturation, and filters.
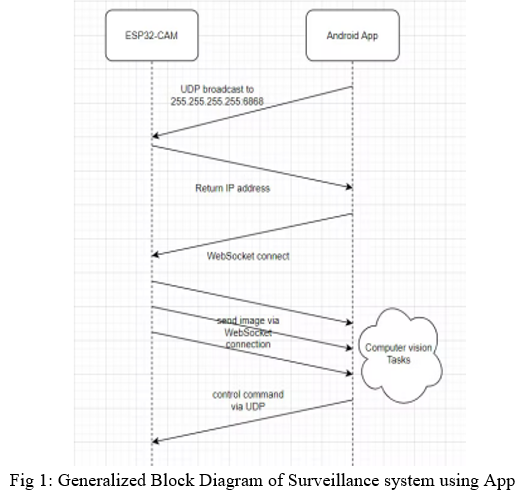
Flow ESP32-CAM and Android Phone connect to the same wifi network. ESP32-CAM act as a UDP server listens on port 6868, Android Phone sends a broadcast message to address 255.255.255.255:6868 to acquire the address of the ESP32-CAM, then create a WebSocket connection to that address port 86. After connection is established, ESP32-CAM will stream images to Android phone, then the image processing is done there. Android phone can also control the ESP32-CAM GPIOs via UDP package
A. Methods of Employing Camera Video and Image Acquisition
The three real-time implementation techniques proposed for configuring, interfacing, and networking the IP camera are:
- Using the WANSCAM or XXCAM vendor software to access the IP-based camera,
- Using the Firefox® web browser to access the IP-based camera, and 3) using MATLAB with SIMULINK on an internet system to access the IP camera.
The user of an IoT-based security system can monitor activity from a remote place and collect images based on his preferences. When an incursion is detected, the Android app allows the user to receive notifications and examine the image from a remote location. PIR motion detectors are used to detect movement. In order to avoid frequent interruptions, the system functions in both Auto and Manual mode. Notifications are provided to the user only when Auto mode is enabled.
The ability to operate the Raspberry Pi from a window has been established, which means that the user can alter the position of the camera from an Android phone window and record a fresh image.
B. Techniques for Analyzing
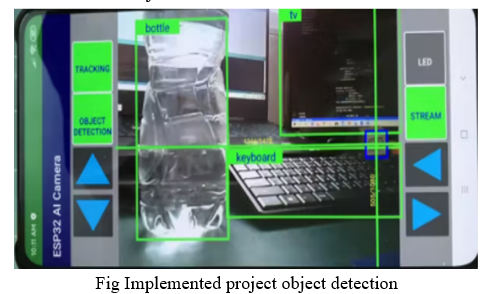
Image categorization frequently necessitates feature extraction; there are a variety of feature extraction approaches that work well for various visual recognitions. Histograms and the patterns method are two examples of methodologies that need domain expertise to identify features and manual coding depending on the domain and data format. While deep learning eliminates all of the drawbacks of earlier techniques, it does necessitate the development of a feature extractor. The most effective and efficient technique to identify photos is to utilise a convolution neural network (CNN). CNNs can be trained on a large-scale database and then their learnings can be refined and applied to different tasks with less training material. Depending on the quantity of training data available, training a CNN can take several days or weeks. There are pre-trained models that are publicly available and that have been trained by research teams. A CNN's architecture is entirely dependent on the domain area, and it can be designed by a domain specialist. Although a CNN can have numerous hidden layers, the complexity of the CNN grows as the number of hidden levels increases. Haar Cascade to recognise items in a crowded background in a variety of settings, including lighting, position, object size, and position. The library which we have used has classification algorithms embed into it, which then checks for the problem and identifies a best suited algorithm to detect the objects.
Conclusion
Extracting the feature, background removal, and identification of the extracted item are the fundamental components of tracking for surveillance systems. In recent years, video surveillance, object identification, and tracking have attracted a lot of attention. Item tracking is a process for identifying the distinct locations of an object in each frame of a video. It is described as the issue of discovering the path (i.e. trajectory). We expand the notion of single detection using a single stationary camera to enable tracking of object detection under moving camera and to maintain a security based system by employing numerous cameras to monitor people in an interior setting. We covered data collection, storage, and analysis techniques for CCTV camera surveillance in this research. Object detection is an important parameter in video surveillance hence it is very effective to have object detection in this surveillance system
References
[1] Kosba, Ahmed E., and Moustafa Youssef.”RASID demo: A robust WLAN device-free passive motion detection system.” Pervasive Computing and Communications Workshops (PERCOM Workshops), 2012 IEEE International Conference on. IEEE, 2012. Sanjana Prasad et al, / (IJCSIT) International Journal of Computer Science and Information Technologies, Vol. 5 (6) , 2014, 7107-7109. [2] Robson, Clyde, et al. ”High performance web applications for secure system monitoring and control.” Nuclear Science Symposium and Medical Imaging Conference (NSS/MIC), 2012 IEEE. IEEE, 2012. [3] Bandi Narasimha Rao, Surveillance Camera using IoT and Raspberry Pi, Proceedings of the Second International Conference on Inventive Research in Computing Applications (ICIRCA-2020) IEEE Xplore Part Number: CFP20N67-ART; ISBN: 978-1-7281-5374-2 [4] Luca, Gabriele, et al. ”The use of NFC and Android technologies to enable a KNX-based smart home.” Software, Telecommunications and Computer Networks (SoftCOM), 2013 21st International Conference on. IEEE, 2013. [5] Michael F.Adaramola ,Michael.A.K.Adelabu “Implementation of Closed-circuit Television (CCTV) Using Wireless Internet Protocol (IP) Camera” 1.School of Engineering, Lagos State Polytechnic, Ikorodu, P.M.B. 21,606, Ikeja. Lagos. Nigeria [6] Tan Zhang, Aakanksha Chowdhery, Paramvir Bahl, Kyle Jamieson, Suman Banerjee “The Design and Implementation of a Wireless Video Surveillance System” University of Wisconsin-Madison, Microsoft Research Redmond, University College London [7] C M Srilakshmi1, Dr M C Padma2 “IOT BASED SMART SURVEILLANCE SYSTEM” International Research Journal of Engineering and Technology (IRJET) Volume: 04 Issue: 05 | May -2017 [8] Mrs. Prajakta Jadhav1, Mrs. Shweta Suryawanshi2, Mr. Devendra Jadhav3 “Automated Video Surveillance eISSN: 2395 -0056 | p-ISSN: 2395-0072” International Research Journal of Engineering and Technology (IRJET) Volume: 04 Issue: 05 | May -2017 [9] Pawan Kumar Mishra “A study on video surveillance system for object detection and tracking” Nalina.P, Muthukannan . K [10] Jian Liang “Camera-Based Document Image Mosaicing” 18th International Conference on Pattern Recognition (ICPR\'06) [11] Akanksha Rastogi, Abhishesh Pal, Beom Sahng Ryuh “Real-Time Teat Detection using Haar Cascade Classifier in Smart Automatic Milking System” 2017 7th IEEE International Conference on Control System, Computing and Engineering, 24–26 November 2017, Penang, Malaysia [12] Paul Viola, Michael Jones “Rapid Object Detection using a Boosted Cascade of Simple Features” 2001 IEEE [13] Rahul Chauhan, Kamal Kumar Ghanshala, R.C Joshi “Convolutional Neural Network (CNN) for Image Detection and Recognition” 2018 IEEE [14] Le Kang, Jayant Kumar, Peng Ye, Yi Li, David Doermann “Convolutional Neural Networks for Document Image Classification” 2014 IEEE [15] Nadia Jmour, Sehla Zayen, Afef Abdelkrim “Convolutional Neural Networks for image classification [16] ” 2018 IEEE
Copyright
Copyright © 2022 Mrs. Naziya Farhat, Mohammad Nasiruddin. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET41512
Publish Date : 2022-04-16
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

