Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Detection and Prevention of Phishing Attacks in DDoS Using Collaborative Learning Algorithm
Authors: Ms. Cheena, Dr. S. Radha Rammohan
DOI Link: https://doi.org/10.22214/ijraset.2023.48906
Certificate: View Certificate
Abstract
Threat to cyber security are significant in providing phishing attacks with huge industry area with anti phishing simulations. Thus it minimizes risk taken infuses attacks with phishing. Large scale phishing training participates various simulations based on phishing attacks. In our proposed system phishing attacks will be analysed based on its credentials and simulated with training data results. They are developed along with data driven models for classification of users perceiving such phishing attacks. Besides analyzation of results based on huge attacks on phishing and training them against those phishing data users most clicking behaviour will be monitored regularly. Cyber phishing attacks in DDoS are significant in IoT are threat in internet environment and predicts attacks through collaborative learning algorithm. Attacked systems connected through onine processes malicious actions without any authorized or authenticated attacks. Further phishing techniques will be predicted using training data and updated on machine learning using Collaborative Learning Algorithm.
Introduction
I. INTRODUCTION
Humans are often stated to be the weakest hyperlink in IT security. It is, therefore, not surprising that e mail phishing remains visible as one of the most big threats in cyber safety. Malware attack like Emotet have confirmed that emails are still an effective approach to supply malicious invaders to cease customers and that credential stealing attacks and ransomware regularly work hand in hand [1]. Organizations have long realized that phishing is a hazard to be taken severely and that conventional countermeasures like electronic mail filters and two-component authentication cannot entirely prevent such attacks. One of the ultra-modern tendencies in phishing countermeasures is to work on the weakest hyperlink, the human, by means of applying anti phishing schooling. Companies that specialize in anti-phishing training offer their clients services in simulated phishing [2].
Attacks and invaders malicious trick details, its effectiveness, method, and ethics of anti-phishing training are controversially mentioned inside the research network. Several researchers have centered on estimating the impact of anti phishing [3]. One manner to triumph over this hassle is by way of sending out numerous attack simulations to the users and taking a feasible technique. The uncertain inclusion where number of simulations are essential to estimate a base recognition degree and groups observe different approaches. Similarly, some organizations might use the users performance for their choice system on the way to progress with the anti-phishing training and learning techniques. Every other way of eradicating this trouble is through sending out the same attack simulations to all users, which may work in some cases whilst the range of customers is exceedingly small, and the email content material is normally in line with the person’s expectancies. Unluckily, in practice, this method consequences inside the problem that for large user corporations, the content material and shape of the e-mail regularly cannot completely be aligned with the expectation of all of the users [4]. Therefore, the effects of attack simulations do no longer completely represent the actual sub speciality stage of the users, for instance, in cases in which need to be evaluate the person’s ability to hit upon most phishing emails.
II. LITERATURE SURVEY
The company which is involved publicly apologized for sending deceptive emails, and these examples demonstrate that anti-phishing training is often an ethical grey spot. An critical component is how customers are handled when falling for anti-phishing simulations. Several researchers have investigated the aspects of poor and wonderful feedback on users falling for anti-phishing simulations [5]. In decreasing the quantity of users clicking on phishing emails. But, punishment can have bad organizational side effects, such as customers now not reporting actual phishing incidents due to the fact they sense they did something wrong and will get chastised. On the other hand, some industry specialists recommend fantastic reinforcement studying because, from their perspective, it encourages users to report phishing emails more regularly.
In common content material of anti-phishing simulations play a crucial position in how users perceive and react to phishing threats. Other elements just like the interest of the users, the content material alignment to the user’s expectation or the alignment of the sending time seem to be influential elements [6]. Thoughts to estimate a phishing mail’s issue had been mentioned the usage of clue-based scales. But, to our knowledge, none of the proposed problem scales have been ever used in massive-scale studies.
To discover the efficient ability answer in the framework in evaluation using the IoT dataset. The dataset into train and test units for system evaluation and preparation [7]. To teach our set of rules, given it the 90% complete dataset, and it will put together it earlier than making predictions at the check set, which makes up 10% of the entire dataset. The technical information of the proposed and modern algorithms are deployed [8]. The table lists each hybrid algorithm’s layers, neurons, epochs, optimizer, batch size, and activation functions.
III. PHISHING ATTACK DETECTION USING COLLABORATIVE LEARNING
The attacks on anti-phishing forced on cyber information, there are 66% of users do no longer fall victim to credentials primarily based on phishing threats even after being uncovered to phishing simulations [9]. In addition to enhancement of the phishing focused on training effectiveness, evolving a novel manifold gaining knowledge of powered machine learning knowledge of version that can expect how many people would fall for a phishing simulation on attacks using the numerous structural and contemporary NLP features extracted from the emails. On this way a scientific technique for the attack implementers to estimate the common attacks of the emails prior to process attack prediction. Furthermore the most important elements within the model affords huge benefits over conventional rule-based methods in classifying the problem of phishing simulations is known as Collaborative Learning Algorithm.
Training results actually show that anti-phishing training must be captured on the training of character users in preference on huge consumer attacks [10]. Additionally presenting a promising phishing detection system training model for predicting phishing susceptibility. Cyber-threats consisting of bottleneck, Dos, DDoS, and botnets are still considerably threats in the IoT surroundings. Botnets are presently the maximum huge danger at the internet.
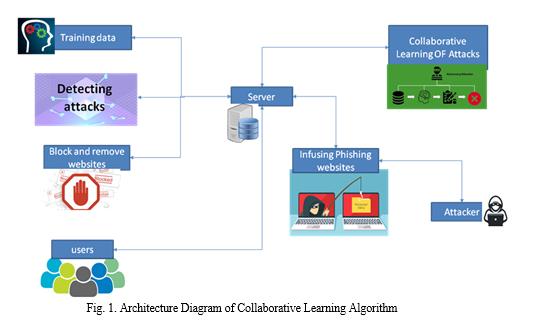
Systems linked on line and directed via an adversary to carry out malicious movements with out authorization or authentication is called a botnet [11]. A botnet can compromise the system and steal the information. It may additionally perform attacks, like Phishing, spamming, and greater attacks. To overcome the crucial problem of a novel botnet attack detection approach that might be applied in fog computing conditions to dispense with the attack using the programmable nature of the Software Defined Network (SDN) environment.
The most current dataset for our proposed technique, fashionable and prolonged performance evaluation measures, and current data learning models. To further illustrate average overall performance, our findings are go proven. The proposed technique plays better than preceding ones in efficiently figuring out multi-version state-of-the-art bot attacks. Moreover, the time of our advised method indicating suitable speed efficiency results.
The selection of models used in paintings is mounted at the most version of phishing uses data training strategies to provide a adaptable, dependable, and particularly accurate botnet antimalware approach. The proposed detection approach detects benign and malicious behavior by using designing data learning in machine language based on system. The optimizer, activation, and loss functions considered for the implementation are machine learning with attacks that has categorical move-entropy respectively. The choice of parameters is dependent upon our rigorous experimentation and interactively determining the ultimate numbers of layers and neurons alongside with different parameters.
IV. RESULT ANALYSIS AND MACHINE LEARNING
In the result analysis, managing unlabeled or unstructured statistics in one of these advanced networks most essential applications. The machine learning, prevention of attacks wherein innovation makes use of a part of artificial machine learning attempts to organization and question information in approaches that move beyond basic statistics/performance conventions. Making use of a machine learning of data method has the gain of being able to automatically becoming aware of the crucial functions from information with out the requirement for a function selection technique using collaborative training results.
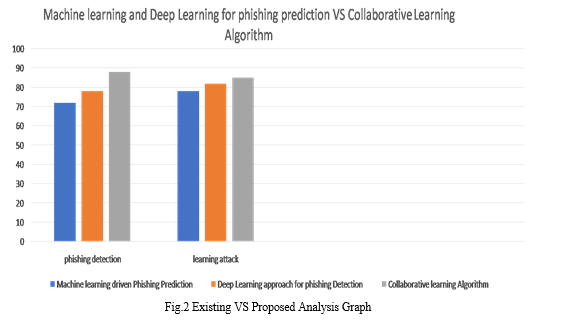
Furthermore, machine learning of phishing and its detection techniques have proved to be reliable and generalized, if designed nicely, able to detecting less threats. Few among them are convolutional layers. The outcomes are converted into innovative layers using calculational models to reproduce a section of the human interaction within the innovative layer. When a complicated version stimulates the development of the capability of artificial intelligence and proposes a structure that accurately reproduces the kinds of human interaction this is an real instance of intensity perception. The essential purpose of criminals to perform along with the advantage of acting Denial of service Provider attacks, Phishing, spamming, and other attacks. Software development network is an open, programmable rising paradigm that permits simple enhancement among the manipulate plane and network system and techniques. The innovation and deployed techniques are added in machine learning progresses towards Obtaining safety to software based computing architectures.
Conclusion
The paper confronts the efficient ability of preventing phishing attacks in DDos using collaborative learning for predicting further attacks. The proposed work evaluated using IoT dataset then involve them into training and testing datasets for evaluation of system process. The complete dataset will put together to check set of data and predicts entire training dataset. The phishing detection paradigm recognises significant pishing and analysis based on machine learning technique.
References
[1] Z. Hussain, A. Akhunzada, J. Iqbal, I. Bibi, and A. Gani, ‘‘Secure IIoT enabled industry 4.0,’’ Sustainability, vol. 13, no. 22, p. 12384, Nov. 2021. [2] R. K. Barik, H. Dubey, K. Mankodiya, S. A. Sasane, and C. Misra, ‘‘Geo Fog4Health: A fog-based SDI framework for geospatial health big data analysis,’’ J. Ambient Intell. Hum. Comput., vol. 10, no. 2, pp. 551–567, Feb. 2019. [3] S. Khan, S. Parkinson, and Y. Qin, ‘‘Fog computing security: A review of current applications and security solutions,’’ J. Cloud Comput., vol. 6, no. 1, pp. 1–22, Dec. 2017. [4] J. Malik, A. Akhunzada, I. Bibi, M. Talha, M. A. Jan, and M. Usman, ‘‘Security-aware data-driven intelligent transportation systems,’’ IEEE Sensors J., vol. 21, no. 14, pp. 15859–15866, Jul. 2021. [5] Z. Ning, X. Hu, Z. Chen, M. Zhou, B. Hu, J. Cheng, and M. S. Obaidat, ‘‘A cooperative quality-aware service access system for social internet of vehicles,’’ IEEE Internet Things J., vol. 5, no. 4, pp. 2506–2517, Aug. 2018. [6] X. Wang, Z. Ning, M. C. Zhou, X. Hu, L. Wang, Y. Zhang, F. R. Yu, and B. Hu, ‘‘Privacy-preserving content dissemination for vehicular social net works: Challenges and solutions,’’ IEEE Commun. Surveys Tuts., vol. 21, no. 2, pp. 1314–1345, 2nd Quart., 2019. [7] Z. Ning, Y. Li, P. Dong, X. Wang, M. S. Obaidat, X. Hu, L. Guo, Y. Guo, J. Huang, and B. Hu, ‘‘When deep reinforcement learning meets 5G enabled vehicular networks: A distributed offloading framework for traffic big data,’’ IEEE Trans. Ind. Informat., vol. 16, no. 2, pp. 1352–1361, Feb. 2020. [8] X. Wang, Z. Ning, and L. Wang, ‘‘Offloading in internet of vehicles: A fog enabled real-time traffic management system,’’ IEEE Trans. Ind. Informat., vol. 14, no. 10, pp. 4568–4578, Oct. 2018. [9] H. Dubey, J. Yang, N. Constant, A. M. Amiri, Q. Yang, and K. Makodiya, ‘‘Fog data: Enhancing telehealth big data through fog computing,’’ in Proc. ASE BigData Socialinform., 2015, pp. 1–6. [10] W. U. Khan, T. N. Nguyen, F. Jameel, M. A. Jamshed, H. Pervaiz, M. A. Javed, and R. Jäntti, ‘‘Learning-based resource allocation for backscatter-aided vehicular networks,’’ IEEE Trans. Intell. Transp. Syst., early access, Nov. 18, 2021, doi: 10.1109/TITS.2021.3126766. [11] A. M. Rahmani, T. N. Gia, B. Negash, A. Anzanpour, I. Azimi, M. Jiang, and P. Liljeberg, ‘‘Exploiting smart e-health gateways at the edge of healthcare Internet-of-Things: A fog computing approach,’’ Future Gener. Comput. Syst., vol. 78, pp. 641–658, Jan. 2018.
Copyright
Copyright © 2023 Ms. Cheena, Dr. S. Radha Rammohan. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET48906
Publish Date : 2023-01-29
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

