Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Digital Forensics based Defence Security System
Authors: Akhil Patil, Aditya Sakhare, Amiruddin Samani, Mahesh Prajapati
DOI Link: https://doi.org/10.22214/ijraset.2022.41883
Certificate: View Certificate
Abstract
This project addresses the structure, implementation and application of digital forensics security System with the assistance of face recognition and fingerprint identification which might be employed in Military Bases and other defence bases. Forensics munition using face and fingerprint recognition may be a system during which tracking of daily activity of officers is in an automatic manner and done by the program itself which is finished by the popularity and identification of the face with the assistance of a camera module which is connected with the system. The camera module helps the system with the initial a part of the program which is initialization of the camera on which the system can perform its operation. When the face comes before of the camera and provides their fingerprints, the program compares the face within the camera with the photographs and detect the fingerprint within the database and recognizes it. These image data are basically known data for the system and is that the data on which the system is trained. The system, if recognizes the face after the comparison with the database, displays the name of the person’s face as an alternative displays “UNKNOWN” if the faces don’t match. Then it tracks the identity of the person file of only the matched faces. This data is stored in an excel file format safely
Introduction
I. INTRODUCTION
Face detection and Fingerprint detection based security systems evolution creates the optimized security system which restricts the entry of unknown. there have been such a big amount of new technical instruments like door intercoms but the protection was still the question of matter because it isn't that much compact and haven't any storage. So to enhance the prevailing security and reduce the risks we include this advance Haarcascade algorithm for face detection based security. A Face recognition System could be a system which usually automatically identifies or verifies the identity of an individual from digital images or a frames from a video source and permit the user to interface with scenario. The image capitulation and identification is completed by OPEN CV and stores in database. the essential work structure of the face recognition system is: - the camera captures the image. After this, using advance Haarcasacade algorithm, system compares the captured images with data base images which give the result as image matched or not. The patterns of those ridges on each finger are inimitable and unassailable which formulate fingerprint a particular variety of identification for every individual. The Raspberry PI 3 Model B may be a third generation embedded system that maintains the identical popular board format of the private computer with low cost and lesser size embedded devices. It doesn't comprise an integrated hard-disk or but uses a SD card for booting and continual storage. the muse of Raspberry PI provides Debian and Arch Linux ARM distributions for download. Researchers are occurring to develop systems utilizing a mix of biometrics and low cost embedded systems with IoT capability like Raspberry PI 3.
II. LITERATURE SURVEY `
The author Akshay N. Patil and etl. [1] describes the working of the face recognized door unlocking system in which they use the raspberry pi along with the GSM module. This module contains a secured face recognizer for automatic door opening. In this project they have the facility of the informing to the user regarding the door unlocking. But, this system lags the feature of making the door unlocking for known persons to the user. This system uses the basic PCA algorithm to execute the process, but still lacks in many feature; hence need to improve. The author SarathChanduGaddam and etl. [2] describes the working of face recognized attendance system in which they use raspberry pi along with GSM module and Ethernet cable. In this project the automatic attendance of the students can be possible without wasting the time and send the attendance to the respective student after 24 hours. But, this system lags the feature of making the latecomers attendance available. In this system they have used the Eigen algorithm to execute the system, but due to huge mathematical calculation there may be chance of failure. Hence need to improve. The author K.ShivaPrasd [3] describes the working of the technique for real time human face detection and tracking using a modified version of the algorithm by using the raspberry pi module along with USB camera. In this project Simulation results of this developed algorithm shows the Real time human face detection and tracking supporting up to 50 human faces. This lags the feature of the making more than 50 faces storage in the database. This system uses the viola jones algorithm for the execution but this system lacks the efficiency in the harsh backlighting and occlusions.
The author Mr. Ashwin K Kashyap and etl. [4] describes the working of face recognition using raspberry pi module by using the python language. In this project the saved faces are detected using OPEN CV simulation. But, this project lags the feature of informing the user regarding the any unknown intruder and hence any burglary. This system uses the HAAR algorithm for execution but this system to depend on the OPEN CV simulation. The author Akshay Kumar C and etl. [5] describes ORB-PCA based face extraction Research Article Volume 8 Issue No.3 International Journal of Engineering Science and Computing, March 2018 16410 http://ijesc.org/ technique for face recognition to overcome the problems of SIFT-PCA and SURF-PCA techniques. It improves the efficiency in face detection and also reduces the face detection time in comparison to other PCA techniques. But this technique is very much complex and much may produce the errors while combining the results of ORB and PCA techniques. Hence need to improve. The author Hemant Makwanaand etl. [6] describes comparisons in various types of face detection algorithms such as geometry based and face appearance based algorithmjs. This kind of comparison will be helpful in the construction of this project. The author Sungyoung Lee and etl. [7] describes improvement in the PCA algorithm for face recognition which shows that the PCA algorithm can be improved and some of this improved features will be used for our project. The author Ms. Varsha Gupta and etl. [8] describes study of various face detection methods which focuses on the adaptations in various face detection algorithms such as Viola-Jones, LPB, Adaboost, SQMT. This kind of literature will be helpful. The author Liton Chandra Paul and etl. [9] describes face recognition using principle component analysis method which shows the statistical approach to reduce the variable based on the eigen values. This paper shows the image identification along with changes in poses. This system will help to produce a good face detection result. But this system only deals with the eigen values and if this values may get mismatch for huge amount of images hence need to improve. The author Santosh Kumar and etl. [10] describes advance approach for faced detection using PCA algorithm and region based colour segmentation which Eigen values and noise removal in image. This system may get failed if there may have any noise disturbance. Practically this system is for testing captured images with stored images in database and based on that it will give result. This technique achieves much higher efficiency and execution time reduces but don?t have ability to provide self-storage as well as reduction in errors. Hence need to improve. The author Sougata Das and etl.
III. RELATED WORK
There are multiple places where Face Recognition system have their application. Each type of system used have their own various features and process of building the system. Samridhi Dev, Tushar Patnaik published an IEEE paper. In this paper, they have described a simple face recognition and trained a model on the same. They have also stated how the system responds to different camera angles. Nandhini R, Duraimurugan N, S.P. Chokkalingam published paper in IJEAT. In this paper they have compared different security system. They have stated the advantages of using biometric recognition system over the traditional system and also proposed an easy way to develop automatic attendance system. Mayank Srivastava, Amit Kumar, Aditya Dixit, Aman Kumar published paper in IEEE. In this paper they have developed security system using python programming language. They have used OpenCV for developing the system. They used data science technique for training the model. Smitha, Pavithra S Hegde, Afshin published paper in IJERT. In this paper they have described various steps for creating security system. They have used Haar-Cascade algorithm for image detection. They have developed the system in which the generated identity detection of person and saving in database and send it to person via E-mail.
IV. BLOCK DIGRAM
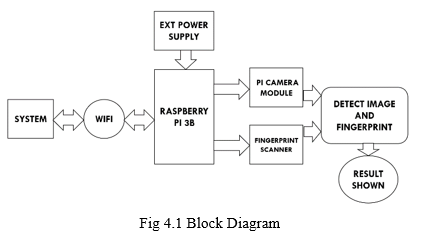
V. BLOCK DESCRIPTION
Face recognition involves accuracy that if the image of any person’s face matches correctly any of the face image data that are being stored in a database. Face recognition system is natural and does not need any individual assistance to work. The program takes the face recognition approach for automating the attendance tracking of the person. A camera or a web cam is used as a device for the initial process capturing the images of students or employees. The faces in the captured images are detected and checked with the images in database by the program. Then, finally, the attendance is tracked. As shown in Figure the model (Raspberry Pi 3B) is given a power supply and switched on. Then, through Wi-fi, the model is connected to the program. After this step, the model runs and initially it accesses the camera and then detects the face. Fingerprint scanner connect to system through the USB UART module for detection. Once Fingerprint scanner module is connected then through SSH terminal will check the whether connections is successful or not. Then from commands given the output will be shown.
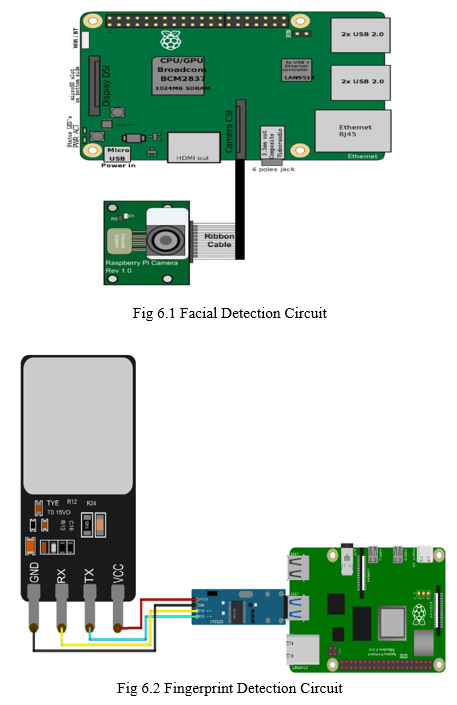
VI. CIRCUIT DIAGRAM
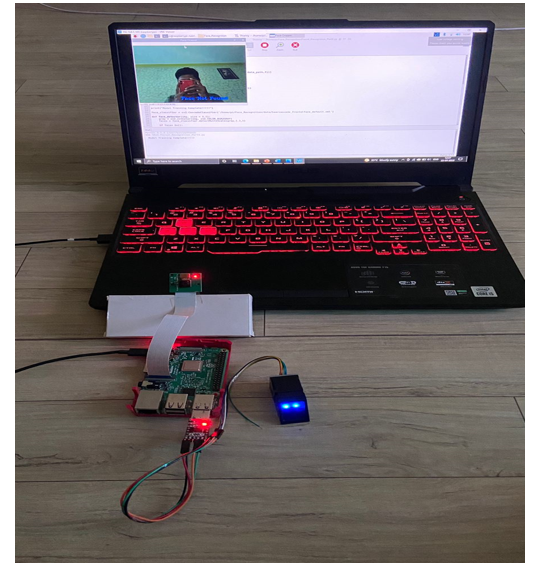
VII. IMPLEMENTATION
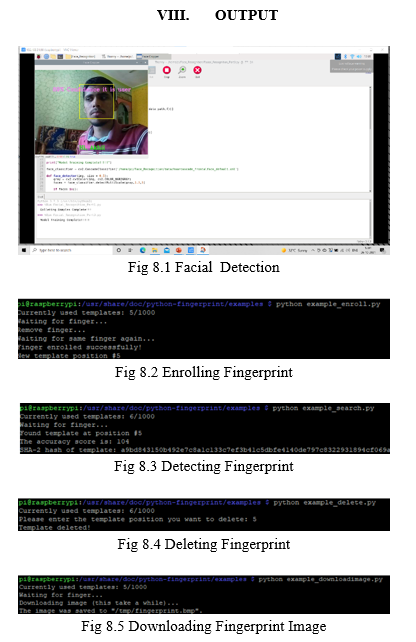
This system is based on face recognition which involves image processing. This system is based on OpenCV library. The library is open source library supported by Python as well as JAVA. When the software first runs it opens the camera connected to controller. When the camera is turned on it will scan the face that is which is in front of the camera. The image captured by camera will then be compared with the pre stored images in the system. When a face or multiple faces are in front of the camera, it starts to locate faces visible in the screen. This is done using the OpenCV and face-recognition libraries. The OpenCV is an open-source library built in python for working on image processing and computer vision related problems. The library is used at the initial stage of the program at which the data processing is done. The data used here majorly are image data. Through the library, we can perform multiple operations such as accessing the camera, image reading, image cropping, conversion of image from BGR(Blue-Green-Red) to RGB(Red-Green-Blue) format for faster and efficient performance of the software, drawing rectangles around faces and adding text as well, and various other operations. The face-recognition library, on the other hand, is primarily used for locating faces and their identification. Using this library, we can find the faces in an image by finding their locations and also find their encodings. Once the software has found the face, it checks the face with the images stored in the database (known images) by comparing the encodings of the face seen in the screen with the encodings of the face in the images in the database. If the face matches with one of the faces in the database, it shows the name of the person’s face as a label in the webcam itself. If the face doesn’t match with the database images, then it labels the image as “UNKNOWN”.
Fingerprint Scanner initialized through SSH command. A total of up to 1000 different fingerprints can be stored. A finger can also be used several times for example. It can be stored in different positions so that they are detected more quickly / more clearly. The following should appear, which allows you to display the positions under which an imprint is stored by selecting a page (0-3). Attached are sample files for storing a new fingerprint, reading out and deleting stored fingerprints. Put your finger on the glass surface, wait for the instruction in the terminal and remove your finger as soon as it is written there. Afterwards you have to put your finger a second time for the verification and the imprint is stored in the next number.
IX. FUTURE SCOPE
There are many future scopes regarding this project such as follows: -
- If the condition improved, we can implement this system by using multimedia GSM module in future.
- To achieve more sound security, we can use the iris scan method.
- To improve the system peformance, we can use the advance versions of the raspberry pi module as per requirement.
- If user needs to operate this system through android application, it is possible.
Conclusion
The system will be employed in several places like banks, hospitals, labs and other sophisticated automated systems, which dramatically reduce the hazard of unauthorized entry. Evidence are often given to the protection department if any robbery issue occurs. The design of the face recognition system using Raspberry pi can make the smaller, lighter and with lower power consumption, so it\\\'s more convenient than the PC-based face recognition system. Because of the open ASCII text file, it\\\'s freer to try and do software development on Linux.. The system was programmed using Python programing language. Both Real time face detection and face detection from specific images, i.e. visual perception, was dispensed. The efficiency of the system was analyzed in terms of face detection rate. The analysis revealed that the current system shows excellent performance efficiency and may be used for face detection even from poor quality images
References
[1] Akshay N. Patil ,Rohit B. Ranavare, Dayasagar V. Ballal: “Raspberry pi based face recognition system for door unlocking”,International journal of innovative research in science and engineering vol.no.2,issue 3 march 2016. [2] SarathChanduGaddam, N. V. K. Ramesh and Hemadhanekula:“facerecognition based attendance management system with raspberry pi 2 using eigen faces algorithm”, ARPN Journal of Engineering and Applied Sciences vol. 11, no. 13, July 2016 [3] K.ShivaPrasd: “Human Face Detection and Tracking Using Raspberry PI processor”,International Journal & Magazine of Engineering, Technology, Management and Research,Volume No: 2 (2015), Issue No: 8 (August) [4] Mr.Ashwin K Kashyap, Mr.Abhishek S, Mr.Abhishek S A, Ms.Ratnakumari. C: “Face Detection using Raspberry Pi and Python”, National Conference on Product Design (NCPD 2016), July 2016. [5] Vinat A., Akshay Kumar C., GauravShenoy, K.N. Balasubramanayam Murthy, S. Natarajan: “ORB-PCA based features extraction technique for face recognition”, second international symposium on computer vision and internet-2015. [6] Hemant Makwana& Taranpreet Singh: “Comparison of Different Algorithm for Face Recognition”,Global Journal of Computer Science and Technology Graphics & Vision Volume 13 Issue 9 Version 1.0 Year 2013 [7] Vo Dinh Minh Nhat and SungyoungLee : “An Improvement on PCA Algorithm for Face Recognition”, J. Wang, X. Liao, and Z. Yi (Eds.): ISNN 2005, LNCS 3496, pp. 1016.1021, 2005. © Springer-Verlag Berlin Heidelberg 2005 [8] Ms.Varsha Gupta, Mr.Dipesh Sharma: “A Study of Various Face Detection Methods”,International Journal of Advanced Research in Computer and Communication Engineering Vol. 3, Issue 5, May 2014 [9] Liton Chandra Paul1, Abdulla Al Sumam2: “Face Recognition Using Principal Component Analysis Method”, International Journal of Advanced Research in Computer Engineering & Technology (IJARCET) Volume 1, Issue 9, November 2012 [10] Santosh Kumar, Ajmer Manish Mathuria, AtulChaudhary, Ajmer KailashRathore: “An Advance Approach of Face Recognition Using PCA and Region Base Color Segmentation”, International Journal Of Computer Applications (0975 – 8887) Volume 89 – No 17, March 2014 [11] Sougata Das, NilavaDebabhuti, Rishabh Das, Sayantan Dutta, ApurbaGhosh:-“Embedded SystemFor Home Automation Using Sms”, International Conference On Automation, Control, Energy And Systems(Aces),Feb 2014,978- 1 -4799- 3732 – 5/14@2014 IEEE [12] Kuan – Min Lee, Wei-GuangTeng,Ting Wei Hon:- “ Point-N –Press: An Intelligent Universal Remote Controlsystem For Home Appliances” , Ieee Transactions On Automation Science And Engineering , 1545-5955@2016 IEEE. [13] MrutyunjayaSahani, AvinashNayak, RishabhAgrawal, DebhanshuSahu:- “ A Gsm, Wsn And Embedded Web Server Architecture For Internet Based Kitchen Monitoring System” , International Conference On Circuit, Power And Computing Technologies(Iccpct ), 978-1-4799 -7075-9/15@2015 IEEE. [14] BiplavChoudhary,TameemS.Choudhary,AniketPramanik, WasimArif ,J. Mehandi:- “ Design And Implementation Of An Sms Based Home Security System”,978-1-4799-6085- 9/15@2015 IEEE.
Copyright
Copyright © 2022 Akhil Patil, Aditya Sakhare, Amiruddin Samani, Mahesh Prajapati. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET41883
Publish Date : 2022-04-26
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

