Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Face Recognition for Criminal Detection
Authors: K. Manideep Reddy, V. Varun Reddy, B. Vinay Goud, Dr. Y. Sreenivasulu
DOI Link: https://doi.org/10.22214/ijraset.2022.44528
Certificate: View Certificate
Abstract
In these days, assessment camera structure wins as a security system at high speed since this structure can screen from remote spots using Web camera joined to video screen by network. Besides, computerized supplies like Web camera, and hard circle drive are proficiently fabricated, and are sold for minimal price. Likewise, execution gain of these mechanized sorts of stuff improves at a fast rate. Current perception camera structure shows dynamic pictures from some oversight areas shot by various Web cameras all the while. Then, this system makes spectator\'s mind and body tired considering the way that he/she wants to watch enormous number of dynamic pictures been persistently strengthened. Moreover, this structure has a troublesome issue, which is an observer slips over mark of bad behavior. This study eliminates Motion Region from moving individual, and measures Motion Quantity for assessing his/her dynamic state. Also, this recommendation method finds the distinctive place of questionable activity, and checks the degree of risk of the questionable development.
Introduction
I. INTRODUCTION
A. Purpose Of The System
These remark camera frameworks work wrongdoing avoidance, and acquire statistics and evidence about culpability with impact. General reconnaissance digital camera frameworks comprise of Web digital set oversight place, and video screen and difficult plate pressure are in watching room. Furthermore, these automated resources are appended to the organisation with each other so an eyewitness can watch the oversight vicinity from checking room utilizing controller. Nonetheless, commentary digital camera framework has a query of significance, which is a spectator needs to observe a ton of dynamic photo shot via numerous Web cameras, because of brief dissemination of Web cameras. Likewise, Web camera can shoot in quite a while on account that tough circle power is possible to shop sizable volumes of dynamic photograph records.
B. Scope Of The System
The reconnaissance camera framework for neglecting man or woman's manner of behaving facilities consideration round aggregate or a part of human body, and tracks the motion of 1. Therefore, difficulty identification making use of Particle Filter is also called. Take away trademark tone or state of visual challenge, and tune it. Furthermore, tracks diverse topics. Movement acknowledgment makes Human Body Model, and tracks role and development of every frame part like head, middle, and appendage, with the purpose that this approach accepts stance of moving character. Following making use of 2D or 3-d human body version], identifies trademark stance of human frame from the watched character's manner of behaving, and perceives human motion.
II. EXISTING SYSTEM
Reconnaissance digital camera framework wins as a safety framework at fast because this framework can display from far flung spots utilizing Web digital camera related to video display with the aid of network. Furthermore, computerized elements like Web camera, and hard plate power are correctly synthetic, and are sold at low cost.
Furthermore, execution benefit of those automatic materials improves at a fast rate. Current observation camera framework suggests dynamic pix from some oversight regions shot by using severa Web cameras simultaneously. Then, at that point, this framework makes spectator's brain and body worn-out given that helter needs to look at significant quantity of dynamic pix been continually invigorated. Besides, this framework has a hard trouble, which is an onlooker slips over indicator of wrongdoing
III. PROPOSED SYSTEM
This take a look at extricates Motion Region from moving person, and measures Motion Quantity for estimating his/her dynamic state. Furthermore, this proposition technique reveals the figuring out factor of dubious motion, and value determinations the extent of chance of the doubtful motion.
In this assignment we need to become aware of man or woman way of behaving as dubious or now not, presently an afternoon's anyplace CCTV cameras are brought which catch recordings and shop at focused server and bodily inspecting those recordings to distinguish dubious motion from human required bunches of human endeavors and time. To defeat from such issue writer is requesting to mechanize such cycle using Machine Learning Algorithms.
To computerize that interplay first we actually need to collect getting ready model utilizing huge measure of pix (all ability images which depict highlights of dubious exercises) and 'Convolution Neural Network' utilizing TENSOR FLOW Python module.
Then we will transfer any video and in a while utility will separate edges from transferred video and afterward that casing may be implemented on train version to foresee its elegance, for example, 'doubtful or standard'. To perform above idea we actually need to introduce python 3.5 rendition in sixty four cycles PC. I will send this product with code. While programming establishment u want to select checkbox announcing add manner to framework variable. This preference will show on first or 2d display screen of established order. When you introduce programming execute underneath orders. Your framework has to interface with internet.
A. User Interface And Human Factors
This study pinpoints the distinguishing point of Suspicious Activity, and tracks down the extent of threat in a human way of behaving. The analysis estimates that watched character methodologies the preliminary entryway, and goes into the room as CASE-I. This examination result pinpoints the distinguishing focuses, and acknowledges Suspicious Activity from watched individual's way of behaving. Assuming attain distinction among every dab in Motion Quantity in determined
B. Software Requirements
- Operating System: Windows
- Coding Language: Python 3.7
C. Hardware Requirements
- System : Pentium IV 2.4 GHz.
- Hard Disk: 40 GB.
- Floppy Drive: 1.44 Mb.
- Monitor : 15 VGA Colour.
- Mouse: Logitech.
- Ram : 512 Mb.
D. Uml Diagrams
UML represents Unified Modeling Language. UML is a normalized universally useful displaying language in the field of item situated programming. The standard is made due, and was made by, the Object Management Group.
The objective is for UML to turn into a typical language for making models of item situated PC programming. In its ongoing structure UML is contained two significant parts: a Meta-model and documentation. Later on, some type of technique or process may likewise be added to; or related with, UML.
The Unified Modeling Language is a standard language for representative, Visualization, Constructing and recording the relics of programming framework, as well with respect to business demonstrating and other non-programming frameworks.
The UML addresses an assortment of best designing practices that have demonstrated fruitful in the displaying of enormous and complex frameworks.
The UML is a vital piece of creating objects situated programming and the product improvement process. The UML utilizes for the most part graphical documentations to communicate the plan of programming projects.
E. Objectives
The Primary objectives in the plan of the UML are as per the following:
- Provide clients a prepared to-utilize, expressive visual demonstrating Language with the goal that they can create and trade significant models.
- Provide extendibility and specialization instruments to expand the center ideas.
- Be free of specific programming dialects and improvement process.
- Provide a conventional reason for figuring out the displaying language.
- Encourage the development of OO apparatuses market.
- Support more elevated level improvement ideas like coordinated efforts, structures, examples and parts.
- Integrate accepted procedures.
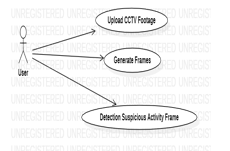
F. Use Case Diagram
A utilization case graph in the Unified Modeling Language (UML) is a kind of social chart characterized by and made from a Use-case examination.
Its motivation is to introduce a graphical outline of the usefulness given by a framework regarding entertainers, their objectives (addressed as use cases), and any conditions between those utilization cases. The principal reason for a utilization case graph is to show what framework capacities are performed for which entertainer. Jobs of the entertainers in the framework can be portrayed.
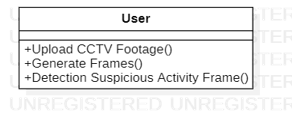
G. Class Diagram
In pc programming, a class outline inside the Unified Modeling Language (UML) is a kind of static layout graph that depicts the construction of a framework by using showing the framework's classes, their traits, obligations (or strategies), and the connections a few of the classes. It makes feel of which class contains statistics.
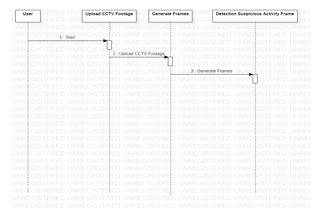
H. Sequence Diagram
A grouping chart in Unified Modeling Language (UML) is a sort of conversation define that suggests how cycles work with each different and in what request.
It is a build of a Message Sequence Chart. Grouping outlines are now and again referred to as event graphs, occasion situations, and timing charts.
IV. IMPLEMENTATION
A. Modules
- Upload CCTV Footage
- Create Frames
- Dubious Activity Frame
In the wake of executing above orders all products will be introduced. To screen I'm utilizing beneath recordings. For preparing I utilized human pictures that cover their countenances to perform dubious action and on the off chance that any video contains individual covering their faces, application will recognize it as a dubious action.
V. SOFTWARE ENVIRONMENT
A. What is Python?
The following are some realities approximately Python is currently the maximum normally applied multi-reason, undeniable stage programming language.
Python lets in programming in Object-Oriented and Procedural requirements. Python packages for the most part are more modest than other programming dialects like Java. Software engineers want to kind generally much less and space necessity of the language, makes them discernible continuously. Python language is being utilized by nearly all tech-monster organizations like - Google,
Amazon, Face book, Instagram, Drop box, Uber… and so forth. The greatest energy of Python is huge collection of general library which can be utilized for the accompanying
VI. SYSTEM TEST
The motivation at the back of testing is to discover mistakes. Testing is the maximum commonplace manner of looking for each possible shortcoming or shortcoming in a work item.
It gives a method for virtually taking a take a look at the usefulness of components, sub gatherings, congregations or doubtlessly a completed item it is the maximum commonplace manner of practicing programming with the aim of making sure that the Software framework meets its necessities and purchaser assumptions and doesn't bomb in an unsatisfactory manner. There are specific kinds of check. Each test type tends to a specific trying out prerequisite.
Kinds OF TESTS
Unit checking out
Unit trying out includes the plan of experiments that approve that the inward program cause is working as it should be, and that software inputs produce valid outcomes.
All desire branches and indoors code circulation need to be permitted. It is the attempting of man or woman programming units of the utility .It's miles completed after the fruits of a unique unit earlier than coordination.
This is an underlying checking out, that relies upon on statistics on its improvement and is obtrusive. Unit exams perform vital checks at component level and check a particular enterprise interaction, application, or doubtlessly framework design. Unit assessments guarantee that every brilliant manner of an enterprise interaction plays exactly to the recorded info and contains manifestly characterized inputs and anticipated results.
Reconciliation checking out
Reconciliation tests are meant to check integrated programming elements to decide whether or not they virtually run as one program. Testing is event driven and is extra worried approximately the vital end result of monitors or fields. Reconciliation assessments showcase that albeit the components were independently achievement, as shown by effectively unit testing, the combination of components is proper and reliable. Incorporation testing is explicitly pointed towards uncovering the troubles that emerge from the combo of parts.
Conclusion
In the examination, this proposition approach is possible to differentiate Suspicious Activity from the watched individual\'s way of behaving, and to gauge the level of danger of Suspicious Activity because of finding the figuring out factor. This statement digital framework can distinguish unsafe oversight region and dubious man or woman, and convey onlooker\'s regard for them using this proposition approach. Furthermore, an onlooker is feeling significantly better of the load of psyche and frame occurred from the matter that is a spectator ought to watch gigantic amount of photo facts shot through severa Web cameras consistent checking of controller. Then, this framework takes place tough issue, which a spectator misses good sized indicator of wrongdoing in place under reconnaissance. This proposition method pinpoints the spotting factor of Suspicious Activity, and reveals the extent of threat of Suspicious Activity with the aim that eyewitness can decrease bodily and mental weight in checking. As exam task, this takes a look at attempts to recognize signal making use of Motion Quantity so that pal robots can have regular and very actual correspondence with human.
References
[1] R.Venkatesh Babe, Patrick Perez, PatrickBouthemy, Robust following motion assessment and close by Kernelbased totally range demonstrating, Image and Vision Computing, Vol. 25, ppI205-1216, 2007. [2] Qing Zhou, Liming Ma, David Cherbourg, Adaptive item identification and acknowledgment in mild of a complaint methodology, Image and Vision Computing, Vol. 24, pp80ninety three, 2006. [3] S.J.McKenna, H.Nait-Charif, Tracking human motion making use of helper molecule channels and iterated opportunity weighting, Image and Vision Computing, Vol. 25, pp852-862, 2007. [4] Paul Barnett, Lyudmila Mihaylova, David Bull, Nissan Canagarajah, Sequential Monte Carlo following by combining numerous symptoms in video arrangements, Image and Vision Computing,Vol. 25, ppI217-1227,2007. [5] Rama Bindiganavale, Norman I. Balder, Motion Abstraction and Mapping with Spatial Constraints. Nadia Magenta - Thiemann, Springer - Verlag Berlin Heidelberg, CAPTECH • ninety eight, LNAI 1537, pp70-eighty two, 1998. [6] Ankur Agarwal, Bill Triggs, Tracking Articulated Motion Using a Mixture of Autoregressive Models, Springer - Verlag Berlin Heidelberg, ECCV 2004, LNCS 3023, pp54-sixty five, 2004. [7] Shiming Xiang, Changshui Zhang, Xiaoping Chen, Naijiang Lu, A New Approach to Human Motion Sequence Recognition with Application to Diving Actions, Springer - Verlag Berlin Heidelberg,MLDM 2005, LNAI 3587, pp487496, 2005.
Copyright
Copyright © 2022 K. Manideep Reddy, V. Varun Reddy, B. Vinay Goud, Dr. Y. Sreenivasulu. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET44528
Publish Date : 2022-06-18
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

