Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
System for Fake Currency Detection Using Image Processing
Authors: Prof. F. S. Ghodichor, Mr. Ajay Kawde, Mr. Rushikesh Patil, Mr. Pankaj Jagadale, Mr. Mahesh Mahajan
DOI Link: https://doi.org/10.22214/ijraset.2022.39832
Certificate: View Certificate
Abstract
Counterfeit money has always existed an issue that has caused many problems in the market. Technological growth development has made it possible to create extra counterfeit items which are distributed in the mitigation market the global economy. Bangui existing banking equipment and so on trading sites to check the authenticity of funds. But the average person does not do that have access to such systems and that is why they are needed in order for the software to receive counterfeit money, which can be used by ordinary people. This the proposed system uses image processing to find out if the money is real or fake. System built uses the Python system completely language. It contains similar steps grayscale modification, edge detection, separation, etc. made using appropriate methods.
Introduction
I. INTRODUCTION
Different countries around the world use different types of currencies to exchange money for other types of goods. One common problem that many countries face is money laundering. [1] in the system. India is one of the countries facing the most problems and huge losses due to counterfeit funds. As a result there is a loss in the general economy of the country's currency. Technological advances have made it possible for funds to double so much that they can be seen more generally [2]. Advanced printers and new computer programming software are used to create counterfeit currency. Counterfeit currencies can easily slip into real money, which is how they are often distributed in the market. Commercial real estate such as banks, supermarkets, jewelry stores, etc. have a large number of daily activities. Such facilities may be able to afford and may consider it necessary to purchase equipment that uses UV light and other methods of verification. But for ordinary people it is very difficult to just find out if the money is fake or genuine and they may face losses especially during bank deposits or transactions. The system is designed in such a way that anyone can easily use it and verify the value of the currency in which it is used using the physical features of the currency [3]. This app can also be converted into an app to make it accessible to everyone. In addition, the program can be designed to generate foreign exchange as well.
The system is based on image processing where a few steps are used to process the currency picture and give the user the effect of whether the currency is real or not. The rest of the paper discusses the following details. In Section II, there is a brief overview of some of the related papers used in the review. In Phase III, a methodology is stated outlining the various steps used in the entire process of acquisition of a currency. In Section IV, the details of the proposed system are specified. Section V shows the result and conclusions. Category VI refers to referral documents and links.
II. LITERATURE SURVEY
A variety of documents are available that contain fraudulent revenue details. Some of the papers mentioned are mentioned here. In [4], as stated, no one can be 100 percent sure of the manual recognition and therefore the system was proposed to compare the images of money with the database and to determine whether the money is fake or not. This program has used to launch and execute system functions. The feature removal process is mainly focused on HSV currency values ??where the image is separated by blocks and operations are performed on the ROI. In [5], the survey paper proposes a system to develop a cash-generating system especially in commercial areas such as banks, shopping malls, etc. Here some different pre-processing techniques are referred to as Radiometric correction and Geometric correction to correct spectral errors or distortions due to sensorEarth geometric variations etc.
Different papers were compared and results were given based on an accurate measurement obtained using different methods. In [6], a system is proposed to detect counterfeit currency based on various factors that can be issued for comparison. Various methods are used in different stages of histogram measurement, using vector vectors to store extruded features, etc. Features used for currency type detection were security line, small RBI print and serial number detection.
III. METHODOLOGY
The current systems are machine-based, that is, they are for commercial purposes only. Systems that use image processing are developed in Python [4], [7]. These devices are based on visual acuity or proximity detection. In visual perception, money is stored under a machine and a UV lamp is scanned for a currency and if the currency is illuminated due to fluorescence, it means that it is a real currency. In finding the representative ink used to make a currency has ferromagnetic properties, so when the money passes the magnetic field and when it shows a certain movement it concludes that it is a real currency [8]. Figure 1 is a flowchart showing the most common methods used to obtain a counterfeit currency using image processing.
- Image Acquisition: An image of a currency that should be tested or verified as a real currency is considered a system input. Image capture can be obtained using techniques such as scanning the image or clicking the image with the phone and uploading it to the application.
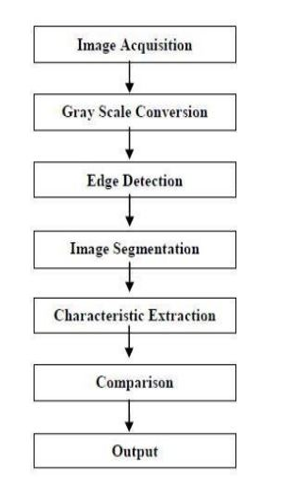
Fig.1 Flowchart to Detect Fake Currency using Image Processing
2. Grey Scale: Converting a color image to a gray image requires more information about the color image. The pixel color in the picture is a combination of three colors Red, Green, and Blue (RGB). Similarly, a Grayscale image can be viewed as a single layer image. Different techniques can be used to turn a color image into a gray image. [9]
3. Edge Detection: Edge detection is a method of image processing to determine the boundaries of objects within images [12]. It works by detecting discoloration in the light. Edge detection is used for image classification and data extraction in areas such as image processing, computer vision, and machine vision. The purpose of a radical change in image brightness is to capture important events and changes in worldly possessions. Edge discovery helps to find all the ROI edges needed to perform various tasks in the later stages.
4. Segmentation: Image fragmentation is the process of dividing an image into many parts. This is often used to identify objects or other important information in digital images. [10] shows a few examples of techniques that can be used to make a distinction. E. Output Feature A feature is a type of size reduction that best represents interesting parts of an image as a combined feature vector. This method is useful when image sizes are large and a reduced feature is required to quickly complete tasks such as image matching and retrieval. Features are extracted and used for comparison in the next step.
5. Comparison: Elements extracted from a previous step are used to compare with the deposited features and the results are presented as real or false currency.
6. Proposed Program: The proposed system uses image processing to determine the type of currency. The inserted or scanned image is provided by a system that can be .png and the output indicates whether the currency is real or not. The process consists of techniques such as pre-image processing, gray scale conversion, edge detection, separation, subtraction and comparing aspect. Figure 2 shows a sketch of the buildings belonging to the proposed system.
a. Step 1: Pre-Image Processing Pre-processing is a common term for tasks with very low output images - both input and output are dynamic images. The purpose of pre-processing is to improve image data that suppresses unwanted distortions or enhances certain image features that are important for further processing. In this program, sound filtering is performed on a pre-image processing [11]. Here, the sound of salt and pepper is removed.
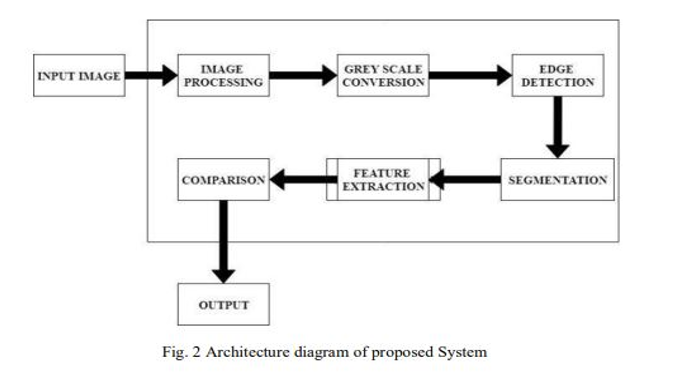
b. Step 2: Converting the gray scale image is converted to the gray scale as it reduces the complexity of coding. There are many methods that can be used to convert an RGB image to a gray image such as measurement, light method, air removal method, etc. [15]. The system uses a light method to perform grayscale conversion.
c. Step 3: Obtaining the edge The grayscale image is the inclusion in this step. The system utilizes the discovery of Canny Edge as it provides much better results compared to other techniques [13]. Canny edge detection is a way to extract useful structural information on a variety of visual objects and dramatically reduce the amount of data to be processed.
d. Step 4: Division There are various methods such as thresholding, merging methods, regional-based classification, etc. performing segmentation in image processing. Here the threshold method is used for segmentation when using the threshold values ??found in the histogram end of the first image. [14]
e. Step 5: Removal Feature and Comparison If the extracted features are carefully selected it is expected that the extracted features will extract the relevant information from the input data. The system uses the SSIM (Structure Similarity Index Method) method to compare feature.
The features that are being compared in the system are as follows for 2000 Rupees note
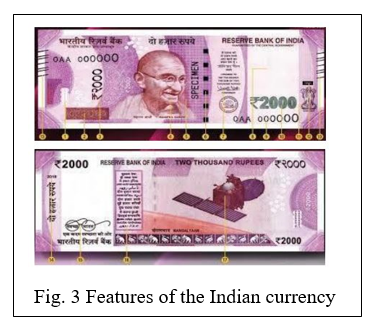
- A picture of Mahatma Gandhi in the middle
- Small letters ?RBI ‘and ?2000’ left of paper money
- A safety window with an RBI text
- Confirmation clause, Governor's Signature with Promise Clause and right RBI logo
- The denomination number with the rupee symbol in the bottom right
- Ashoka Pillar mark on the right and electrotype watermarks
- A panel of numbers that grow in size on the top left and bottom right
- Seven angular bleeding lines on the left and right sides of the coin
- Year of printing coin left Swachh Bharat logo and motto.
???????f. Step 6: Output displays the distinctly marked features that are used to extract the feature and compare. In the output, the system starts by asking the user to upload a currency picture. The output shows four different types of images. The first image is that of the first image compared to the uploaded money. The following image is of a currency uploaded by a user. The third image is a scattered image of grayscale elements. This effect helps to distinguish between the two images namely the original image and the uploaded image. The intersection of these two images shows exactly where the changes in the uploaded image are if they are false. The following image is for fragmented image fragmentation. A distinctive image of the features is made at threshold and is displayed as a result of finding the differences in the images clearly when present. Finally the program indicates whether the image is false or not true.
Conclusion
Spending money is a necessity for survival so it is important that you always keep track of its realities. Paper currencies are widely used in India so a system is needed to detect counterfeit currency. With new currencies being used in the market, the proposed system seems to be useful in determining whether the currency is real or not. This system compares more features of feature release than other proposed systems. It also shows where the difference is in money instead of simply showing the result. This system can also be used in foreign currencies such as Dollars, Euros, Taka, etc. as the scope of the future.
References
[1] Fake Indian Currency Note [Online]. Available:https://en.wikipedia.org/wiki/Fake_Indian_currency_note [2] Chinmay Bhurke, Meghana Sirdeshmukh, Prof. Mrs. M.S.Kanitkar, ?Currency Recognition Using Image Processing? International Journal of Innovative Research in Computer and Communication Engineering, Vol. 3, Issue 5, May 2015 [3] Trupti Pathrabe G and Swapnili Karmore 2011 Int. J. CompTrends Tech 152-156 [4] Eshita Pilania, Bhavika Arora, ?Recognition of Fake Currency Based on Security Thread Feature of Currency? International Journal Of Engineering And Computer Science, ISSN: 2319-7242 [5] P. Julia Grace, Ph.D., A. Sheema, ?A survey on Fake Indian Paper Currency Identification System? Grace et al., International Journal of Advanced Research in Computer Science and Software Engineering 6(7), July- 2016, pp. 340-345 ISSN: 2277 128X [6] Komal Vora, Ami Shah, Jay Mehta, ?A Review Paper on Currency Recognition System? International Journal of Computer Applications (0975 – 8887), Volume 115 – No. 20, April 2015 [7] Tushar Agasti, Gajanan Burand, Pratik Wade and P Chitra, ?Fake currency detection using image processing? 14th ICSET-2017 [8] Fake currency detectors using machines [Online]. Available: https://en.wikipedia.org/wiki/Currency_detector [9] Pramod Kaler, ?Study of Grayscale image in Image processing? International Journal on Recent and Innovation Trends in Computing and Communication, ISSN: 2321-8169, Volume: 4 Issue: 11
Copyright
Copyright © 2022 Prof. F. S. Ghodichor, Mr. Ajay Kawde, Mr. Rushikesh Patil, Mr. Pankaj Jagadale, Mr. Mahesh Mahajan. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET39832
Publish Date : 2022-01-07
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

