Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
IoT Based Emergency Button for Women Safety
Authors: Sanket Chikhale, Aniket Yadav, Faraz Shaikh, Prajakta Dounde, Ishwari Raskar
DOI Link: https://doi.org/10.22214/ijraset.2022.42620
Certificate: View Certificate
Abstract
Fundamental to IoT is the instant collaboration that happens between these smart devices. The beauty behind having a network of interconnected devices is that they can all work together to provide real solutions that are much greater than the sum of their parts. IOT based products are always connected and constantly communicating with each other. They regularly exchange information using wired and wireless networks, which helps make our lives easier and safer. When IoT based smart home security systems are used to safeguard our home or possessions, it’s akin to having our favorite reliable friend dutifully watching over our home or pets in our absence. Except it’s actually way better than that, because unlike our well-meaning friend or neighbor, smart home security systems are always present and are ready to instantly alert us of any signs of danger. Smart products, like Nest Lab’s smoke and carbon monoxide alarm, sounds an alert when it detects high levels of CO, and then warns us of the location of the danger. It’s no wonder that Google acquired Nest Labs for a whopping $3.2 billion! Other companies like Canary offer connected smart home security systems that are now a part of a growing trend: using IoT technology to create safety solutions to protect what’s most valuable to us.
Introduction
I. INTRODUCTION
Existing handheld devices that are available for women safety require women intervention to activate them such as pressing the button or shake the device etc after sensing the danger. However, for some reason if a woman has no time to activate it when she is danger, then the purpose of the safety device is not solved. In a country like India where the growth rate of crime is considered to be more than the growth rate of population, which includes burglary, murders, rapes, and many more women’s safety is believed to be one of the most important issues. According to a report by Thomson Reuters Foundation, India is ranked as a highly dangerous place for women worldwide; India has the greatest number of child brides as well. In 2016, the number of reported rapes is almost 39,000. Experts that were interviewed for the reason why India is presumed to be dangerous for women said India is on top of the list because its government has done almost nothing to provide safety to women since the rape and murder of a student in early 20’s in 2012 which prompted changes in the rape laws of the country. Most of the attacks on women happen when they are traveling alone or are in a remote area where they are not able to find any help or proper assistance. This paper proposes a IoT based solution to address the problem of women safety and that overcome the shortcomings of existing devices. The proposed design comprises of features to notify family members and nearby police station for immediate assistance when women are not safe. Moreover, a shock wave generator is a part of the proposed design which women can use to attack the perpetrator.
Women are not safe anywhere and are most vulnerable when traveling alone into lonely roads and deserted places. Existing hand held safety devices for women require human intervention for activating the device such as pressing the button or shake the device etc. after sensing the danger. We propose a solution which will try to overcome the disadvantages of the existing systems and also aim at providing false proof safety to women. The proposed work aims at designing an IoT based safety device that relies on providing security to women by fingerprint- based method of connectivity to the device and alerting nearby people and police when a women is not safe. An unsafe situation is sensed by fingerprint verification for a minute then it will automatically alert nearby people and police if the device senses no signal. Moreover, for first-hand safety, shockwave generator is also designed that women can use to attack the perpetrator. Additional features such as sending group messages, audio recording are also part of the proposed design. A mobile app is designed for women safety where safe locations from victim’s current location will be shown on the map so that women can reach the safe place from her current location which is unsafe.
II. HARDWARE USED
A. SIM800L GSM/GPRS Module
At the heart of the module is a SIM800L GSM cellular chip from SimCom. The operating voltage of the chip is from 3.4V to 4.4V, which makes it an ideal candidate for direct LiPo battery supply. This makes it a good choice for embedding into projects without a lot of space. All the necessary data pins of SIM800L GSM chip are broken out to a 0.1″ pitch headers. This includes pins required for communication with a microcontroller over UART. The module supports baud rate from 1200bps to 115200bps with Auto-Baud detection. The module needs an external antenna to connect to a network.
The module usually comes with a Helical Antenna and solders directly to NET pin on PCB. The board also has a U.FL connector facility in case you want to keep the antenna away from the board.
There’s a SIM socket on the back! Any activated, 2G micro SIM card would work perfectly. Correct direction for inserting SIM card is normally engraved on the surface of the SIM socket.
This module measures only 1 inch² but packs a surprising amount of features into its little frame. Some of them are listed below:
- Supports Quad-band: GSM850, EGSM900, DCS1800 and PCS1900
- Connect onto any global GSM network with any 2G SIM
- Make and receive voice calls using an external 8Ω speaker & electret microphone
- Send and receive SMS messages
- Send and receive GPRS data (TCP/IP, HTTP, etc.)
- Scan and receive FM radio broadcasts
- Transmit Power:
- Class 4 (2W) for GSM850
- Class 1 (1W) for DCS1800
- Serial-based AT Command Set
- FL connectors for cell antennae
- Accepts Micro SIM Card.
- Selecting Antenna
An antenna is required to use the module for any kind of voice or data communications as well as some SIM commands. So, selecting an antenna could be a crucial thing. There are two ways you can add an antenna to your SIM800L module. The first one is a Helical GSM antenna which usually comes with the module and solders directly to NET pin on PCB. This antenna is very useful for projects that need to save space but struggles in getting connectivity especially if your project is indoors.
2. Supplying Power for SIM800L module
One of the most important parts of getting the SIM800L module working is supplying it with enough power depending on which state it’s in, the SIM800L can be a relatively power-hungry device. The maximum current draw of the module is around 2A during transmission burst. It usually won’t pull that much, but may require around 216mA during phone calls or 80mA during network transmissions.

B. Neo6M (GPS BOARD)
It is a GPS board used to connect to satellite and used to give altitude and longitude without connecting to internet. The NEO-6 module series is a family of stand-alone GPS receivers featuring the high performance u-blox 6 positioning engine. These flexible and cost effective receivers offer numerous connectivity options in a miniature 16 x 12.2 x 2.4 mm package. Their compact architecture and power and memory options make NEO-6 modules ideal for battery operated mobile devices with very strict cost and space constraints. The 50-channel u-blox 6 positioning engine boasts a Time-To-First-Fix (TTFF) of under 1 second. The dedicated acquisition engine, with 2 million correlates, is capable of massive parallel time/frequency space searches, enabling it to find satellites instantly. Innovative design and technology suppresses jamming sources and mitigates multipath effects, giving NEO-6 GPS receivers excellent navigation performance even in the most challenging environments.
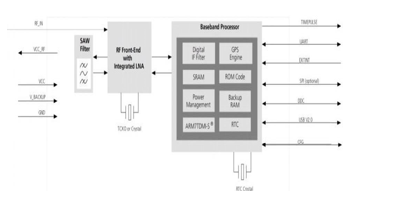
- Block diagram for Neo6m
GPS receivers are Electrostatic Sensitive Devices (ESD) and require special precautions when handling. For more information see chapter 6.4. Stressing the device beyond the “Absolute Maximum Ratings” may cause permanent damage. These are stress ratings only. The product is not protected against overvoltage or reversed voltages. If necessary, voltage spikes exceeding the power supply voltage specification, given in table above, must be limited to values within the specified boundaries by using appropriate protection diodes.
USB NEO-6 modules provide a USB version 2.0 FS (Full Speed, 12Mbit/s) interface as an alternative to the UART. The pull-up resistor on USB_DP is integrated to signal a full-speed device to the host. The VDDUSB pin supplies the USB interface. u-blox provides a Microsoft® certified USB driver for Windows XP, Windows Vista and Windows 7 operating systems.
Serial Peripheral Interface (SPI) The SPI interface allows for the connection of external devices with a serial interface,
e.g. serial flash to save configuration and Assist Now Offline A-GPS data or to interface to a host CPU. The interface can be operated in master or slave mode. In master mode, one chip select signal is available to select external slaves. In slave mode a single chip select signal enables communication with the host.

C. Arduino Nano
It is Microcontroller boards developed by Arduino.cc and based on Atmega328p / Atmega168.Arduino boards are widely used in robotics, embedded systems, automation and electronics projects. These boards were initially introduced for the students and non-technical users but now-a-days Arduino boards are widely used in industrial projects. Any kind of technical support and help is readily provided by the Arduino community. I have also designed this video tutorial on Arduino Nano basics:
- It is a small, compatible, flexible and breadboard friendly Microcontroller board, developed by Arduino.cc in Italy, based on ATmega328p (Arduino Nano V3.x) / Atmega168 ( Arduino Nano V3.x). Arduino Nano is simply a smaller version of Arduino UNO, thus both has almost same functionalities.
- Arduino Nano Pin out contains 14 digital pins, 8 analog Pins, 2 Reset Pins & 6 Power Pins. Each of these Digital & Analog Pins are assigned with multiple functions but their main function is to be configured as input or output.They are acted as input pins when they are interfaced with sensors, but if you are driving some load then use them as output.Tiny size and breadboard friendly nature make this device an ideal choice for most of the applications where a size of the electronic components are of great concern.
- It is programmed using Arduino IDE which is an Integrated Development Environment that runs both offline and online. No prior arrangements are required to run the board. All you need is board, mini USB cable and Arduino IDE software installed on the computer. USB cable is used to transfer the program from computer to board.
- No separate burner is required to compile and burn the program as this board comes with a built-in boot- loader.
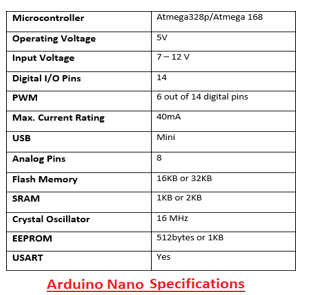
a. REF. This pin is used as a reference voltage for the input voltage.
b. PWM. Six pins 3, 5,6,9,10, 11 can be used for providing 8-pit PWM (Pulse Width Modulation) output. It is a method used for getting analog results with digital sources.
c. SPI. Four pins 10(SS),11(MOSI),12(MISO),13(SCK) are used for SPI (Serial Peripheral Interface). SPI is an interface bus and mainly used to transfer data between microcontrollers and other peripherals like sensors, registers, and SD card.
d. External Interrupts. Pin 2 and 3 are used as external interrupts which are used in case of emergency when we need to stop the main program and call important instructions at that point. The main program resumes once interrupt instruction is called and executed.
- Blynk Application Platform
Blynk is a Platform with IOS and Android apps to control Arduino, Raspberry Pi and the likes over the Internet. It's a digital dashboard where you can build a graphic interface for your project by simply dragging and dropping widgets. Blynk is the most popular IoT platform for connecting devices to the cloud, designing apps to remotely control and monitor them, and managing thousands of deployed products. It's a PaaS (Platform-as-a-Service) that helps individuals and organizations to seamlessly progress from a prototype of a connected product to its commercial launch. With over 400 hardware models support, customers can connect any device to the Internet and use suit of software products to launch commercial projects. Blynk is a new platform that allows you to quickly build interfaces for controlling and monitoring your hardware projects from your iOS and Android device.
After downloading the Blynk app, you can create a project dashboard and arrange buttons, sliders, graphs, and other widgets onto the screen. Using the widgets, you can turn pins on and off or display data from sensors.
Whatever your project is, there are likely hundreds of tutorials that make the hardware part pretty easy, but building the software interface is still difficult. With Blynk, though, the software side is even easier than the hardware. Blynk is perfect for interfacing with simple projects like monitoring the temperature of your fishtank or turning lights on and off remotely. With Blynk, you can create smartphone applications that allow you to easily interact with microcontrollers or even full computers such as the Raspberry Pi.with your phone.
2. Blynk Microcontroller Libraries
The support is implemented by means of a Blynk library that targets a device and connectivity type combination. For example, if you want to use your Arduino Uno with an Ethernet shield, you would use the library “BlynkSimpleEthernet” which contains the Blynk firmware plus the required connectivity support.
If you want to use your Arduino Uno with the Wifi101 shield, you would use the library“BlynkSimpleWiFiShield101”. Both sketches would use the same Blynk infrastructure, such as the physical pins that are part of the Arduino’s hardware, as well as the virtual pins which are implemented in software by the Blynk Platform.
This means that with a bit of planning, you can write sketches that can be easily shared among different target devices. You can potentially write a sketch for an Arduino Uno and and with minimal modification run it on an Arduino MKR1010.Blynk also supports clients that are not a microcontroller.
You can write client code is JavaScript, Python or Lua thanks to the available Blynk libraries for these languages. This means that you can have a Blynk project that interacts with an Arduino and with Python code running on a Linux virtual machine somewhere on the Cloud. The possibilities are really very exciting.
3. Blynk Server
A private Blynk server gives us additional benefits:
a. Essentially unlimited energy units, so that you can build any Blynk application you can think of.
b. Minimal latency, which is useful when your application is used in a limited geographic area and responsiveness is important.
c. Total control of your data. You can keep your own backups of your Private server, migrate your server to a new host, implement whichever security mechanisms you wish, and finely control your users.
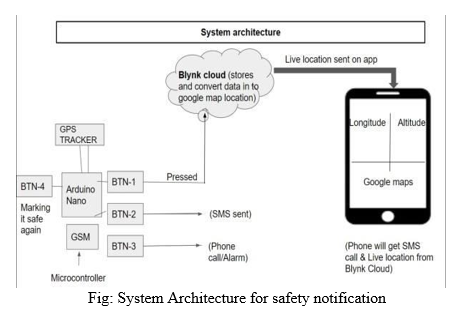
III. PROCESS IMPLEMENTATION
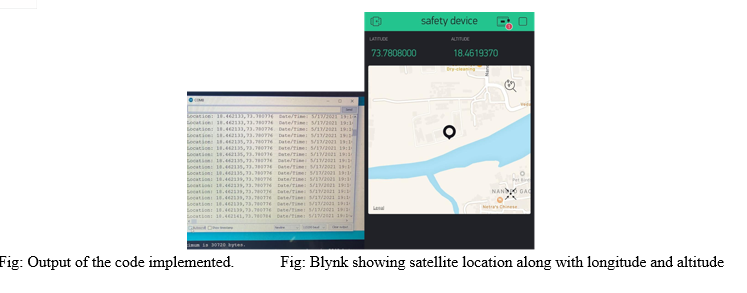
- In the beginning GPS gets connected to satellite. we do this first because it takes some time to get the raw data and to warm up the system. Antena and GPS tracker both connected to Satellite. (it will give us longitude and altitude)
- This raw data will be converted into processed/readable data by GPS tracker and then Real time data will be sent to aurdino nano (Microcontroller) the reason the data gets transferred to Micro controller by GPG is that GPS has microprocessor which is used to processed data. Microprocessor cannot store the data but microcontroller has some limit to store the data. and in this case micro controller is aurdino nano.
- To get SIM registered with our network. GSM (SIM800L) will try to connect to blynk cloud and if gets connected process runs. Later on when user gives input the call and sms will be sent to predefined users (predefined users should not be more than 3 otherwise it will take more than 2 minutes to share the live location)
- When user press the button red LED turn on until the process of sending the live location and alert get completed. Once it is fully sent the yellow LED turns on.
- LED will turn into yellow color and then we wait for blynk to ask for data for location to micro controller.(Button to be pressed only once)
- For me to know if my PDU as seen my alert or live location there is a provision made in the system. As soon as my PDU opens blynk to check live location the green LED gets turned on means user is online and i will get to know that the location is seen and alert has reached. (When PDU press play button my green LED will blynk means bynk is asking microcontroller for data and helps me reminding everything is in control.
A. Future Scope
- Storing and training the data using Machine Learning Algorithm can give notification even before she enters area.
- We may add a feature of emergency helpline numbers such as nearby police stations, Women help groups, nearby NGOs etc.
- This app can be customized and used at a workplace to address the workplace harassment.
- We can also link police dept. through this app and the notification can be sent through this app to nearby on duty police and they can be at the crime scene within minutes.
- The translation of the content can be done in Local languages.
- An offline survey can be conducted with the help of this application and testimonials of real live witnesses can be added for others to refer as a strong evidence.
Conclusion
Women in our country are unsafe everywhere. Public place safety is the need of the hour because the cases of harassment are increasing day by day. There are many reasons why women chose to keep silent when they come across any sort of harassment. The main motto behind initiating this application is to empower women and encourage them to claim their rights when injustice takes place. This application will help them express their views and make it go viral to ensure create a safe environment for others. Through this app women themselves will become self-sufficient to help each other when it comes to ensuring their safety at public place. Though this is a baby step but can turn out to be a big revolutionary step over a period of time the corresponding results were logged. The successful streaming of images of a live event on a web page was done within an intranet. The further implementation of the system will be performed in accordance with the goals mentioned in the future scope
References
[1] A Women Safety Portable Hidden camera detector and jammer S. K, R. Subhashini, S. Gowri and J. S. Vimali, \"A Women Safety Portable Hidden camera detector and jammer,\" 2018 3rd International Conference on Communication and Electronics Systems (ICCES), Coimbatore, India, 2018, pp. 1187- 1189, doi: 10.1109/CESYS.2018.8724066. [2] Development of a Wireless Safety System Based on Multiple Radiation Detector for Nuclear Facilities M. S. Muktadir, S. Islam and A. R. Alam Chowdhury, \"Development of a Wireless Safety System Based on Multiple Radiation Detector for Nuclear Facilities,\" 2019 International Conference on Robotics,Electrical and Signal Processing Techniques (ICREST), Dhaka, Bangladesh, 2019, pp. 539-542, doi: 10.1109/ICREST.2019.8644312. [3] Millimeter wave safety warning system for in-vehicle signing G. Greneker, \"Millimeter wave safety warning system for in-vehicle signing,\" in IEEE Aerospace and Electronic Systems Magazine, vol. 13, no. 7, pp. 7-12, July 1998, doi: 10.1109/62.690727. [4] A new proposal for the analysis of safety instrumented systems M. Catelani, L. Ciani and V. Luongo, \"A new proposal for the analysis of safety instrumented systems,\" 2012 IEEE International Instrumentation and Measurement Technology Conference Proceedings, Graz, Austria, 2012, pp. 1612- 1616, doi: 10.1109/I2MTC.2012.6229556. [5] Structure of Automated Railway Electric Vehicle Safety Control System A. Mor-Yaroslavtsev, A. Levchenkov and L. Ribickis, \"Structure of Automated Railway Electric Vehicle Safety Control System,\" 2010 Second WRI Global Congress on Intelligent Systems, Wuhan, China, 2010, pp. 39-42, doi: 10.1109/GCIS.2010.201 [6] An embedded system of dedicated and real-time fire detector and locator technology as an interactive response mechanism in fire occurrences S. Abaya, E. Cabico, J. Domingo, R. Diaz, H. Kojima and R. Rivera, \"An embedded system of dedicated and real-time fire detector and locator technology as an interactive response mechanism in fire occurrences,\" 2016 IEEE International Conference on Advances in Electronics, Communication and Computer Technology (ICAECCT), Pune, 2016, pp. 407-411, doi: 10.1109/ICAECCT.2016.7942622 [7] Test coverage of the safety instrumented system J. Jin, S. Zhao and B. Hu, \"Test coverage of the safety instrumented system,\" Proceedings of the 30th Chinese Control Conference, Yantai, China, 2011, pp. 4228-4231.
Copyright
Copyright © 2022 Sanket Chikhale, Aniket Yadav, Faraz Shaikh, Prajakta Dounde, Ishwari Raskar. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET42620
Publish Date : 2022-05-13
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

