Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Laser Based Short Range Multipurpose Security System
Authors: Aryan Dongale, Avinash Marbhal, Ritik Matere, Prof. Ashwini Bundele
DOI Link: https://doi.org/10.22214/ijraset.2023.56803
Certificate: View Certificate
Abstract
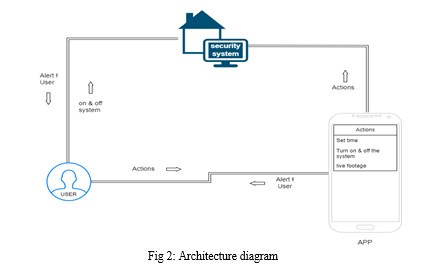
This paper presents an IoT-based Laser Security System (IoT-LSS) designed to enhance perimeter security and intrusion detection capabilities. Traditional security systems often rely on cameras and motion sensors, which can be susceptible to false alarms and environmental limitations. The proposed IoT-LSS addresses these challenges by leveraging laser technology, IoT devices The interruption of the laser beam caused by an intruder\'s movement triggers an alert. IoT integrated with the laser pairs collect real-time data and transmit it to a central control unit. This control unit acts as the brain of the system, making intelligent decisions based on the incoming data stream. Control unit identifies object and differentiation between human movement and other environmental disturbances. The implementation of the IoT LSS demonstrates its effectiveness in reducing false alarms and providing reliable intrusion detection. The fusion of IoT and laser technology not only enhances security but also minimizes maintenance efforts compared to traditional systems. By harnessing the power of IoT, laser technology, the proposed Laser Security System showcases a promising solution for modern security challenges, contributing to a safer and more connected world.
Introduction
I. INTRODUCTION
Laser Emitters and Detectors: Laser emitters are strategically placed around the perimeter to create a laser fence. These lasers emit an invisible laser beam. When the beam is interrupted by an intruder or object crossing the perimeter, it triggers the laser detectors. Laser Detectors: These detectors are positioned opposite the emitters, and they are responsible for receiving the laser beams. When an interruption occurs, they send a signal to the IoT controller. IoT Controller: This central device manages the communication between the laser detectors and other IoT devices. It collects data from the detectors, processes it, and communicates with the cloud-based platform. IoT Devices: Various IoT devices, such as cameras, motion sensors, and environmental sensors, can be integrated into the system to enhance its capabilities. These devices provide additional information and context to the system. Cloud-Based Platform: The data collected by the IoT controller is sent to a cloud-based platform where it is analysed in real-time. Advanced algorithms and machine learning models can be employed to differentiate between true security threats and false alarms. The platform also allows for remote monitoring and control.
Reliability: Laser technology is highly reliable, and the invisible laser beams are difficult for intruders to detect or circumvent. Reduced False Alarms: The combination of laser-based detection and advanced analytics significantly reduces false alarms caused by environmental factors like wind, rain, or small animals. The system can differentiate between genuine threats and harmless interruptions. Real-time Monitoring: The cloud-based platform enables real t ime monitoring and alerts. Security personnel can receive instant notifications of breaches and take immediate action. Integration: The IoT-LSS can be integrated with other security systems and IoT devices to provide a comprehensive security solution. This includes video surveillance, access control, and environmental monitoring. Scalability: The system can be easily scaled to cover large areas and adapted to various types of environments. Data Analytics: The system can collect and analyze data over t ime to identify patterns and trends in security breaches, enabling proactive security measures. Cost-effectiveness: While the initial setup may have higher costs due to the laser technology, the reduction in false alarms and improved security make it cost-effective in the long run. Remote Management: Security administrators can manage and monitor the system remotely, which is especially valuable for geographically dispersed locations. The IoT-based Laser Security System offers a robust and intelligent approach to perimeter security and intrusion detection, addressing many of the limitations associated with traditional security systems. It provides a reliable and efficient means of protecting critical assets and enhancing overall security.
II. LITERATURE WORK
Laser Security alarm is a device used for security purposes. It has a wide applica tion in fields of security and defense starting from the security of simple household material to a very high valued material of an organization. They once used to be expensive solutions for security needs. Owing to cost cutting and fast technological advancements, this form of security system is becoming more affordable. Arduino Mega, GSM Module (Simcom SIM900), Jumper Wire, Buzzer, LDR, Lazer. [1] Arduino IDE: The Arduino Integrated Development Environment (IDE) is a cross-platform ap- plication (for Windows, macOS, Linux) that is written in functions from C and C++. It is used to write and upload programs to Arduino compatible boards, but also, with the help of third party cores, other vendor development boards. The source code for the IDE is released under the GNU General Public License, version 2. The Arduino IDE supports the languages C and C++ using special rules of code structuring. The Arduino IDE supplies a software library from the Wiring project, which provides many common input and output procedures. User-written code only requires two basic functions, for starting the sketch and the main program loop, that are compiled and linked with a program stub main () into an executable cyclic executive program with the GNU toolchain, also included with the IDE distribution. The Arduino IDE employs the program argued to convert the executable code into a text file in hexadecimal encoding that is loaded into the Arduino board by a loader program in the board’s firmware. By default, avrdude is used as the uploading tool to flash the user code onto official Arduino boards. [2] Laser: A laser is a device that emits light through a process of optical amplification based on the stimulated emission of electromagnetic radiation. The term” laser” originated as an acronym for” light amplification by stimulated emission of radiation”. A laser differs from other sources of light in that it emits light coherently. Spatial coherence allows a laser to be focused to a tight spot, enabling applications such as laser cutting and lithography. Spatial coherence also allows a laser beam to stay narrow over great distances (collimation), enabling applications such as laser pointers. Lasers can also have high temporal coherence, which allows them to emit light with a very narrow spectrum, i.e., they can emit a single color of light. Temporal coherence can be used to produce pulses of light as short as a femtosecond. [4] GSM Module: A GSM Module is basically a GSM Modem (like SIM 900) connected to a PCB with different types of output taken from the board – say TTL Output (for Arduino, 8051 and other microcontrollers) and RS232 Output to interface directly with a PC (personal computer). The board will also have pins or provisions to attach mic and speaker, to take out +5V or other values of power and ground connections. These type of provisions vary with different modules. Lots of varieties of GSM modem and GSM Modules are available in the market to choose from. For our project of connecting a gsm modem or module to Arduino and hence send and receive SMS using Arduino – it’s always good to choose an Arduino compatible GSM Module – that is a GSM module with TTL Output provisions. LDR: A Light Dependent Resistor (also known as a photoresistor or LDR) is a device whose resistivity is a function of the incident electromagnetic radiation. Hence, they are light-sensitive devices. They are also called as photoconductors, photoconductive cells or simply photocells. They are made up of semiconductor materials that have high resistance. There are many different symbols used to indicate a photoresistor or LDR. Those semiconductor materials which have a direct band gap are the ones that emit photons. When a suitable voltage is applied to the leads, electrons are able to recombine with electron holes within the device, releasing energy in the form of photons. This effect is called electroluminescence, and the color of the light (corresponding to the energy of the photon) is determined by the energy band gap of the semiconductor. An LED is often small in area (less than I mm2) and integrated optical components may be used to shape its radiation pattern.
III. METHODOLOGY
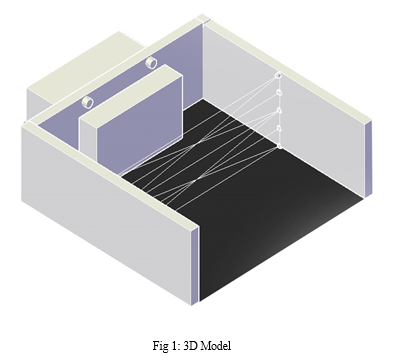
Certainly, here's a methodology for implementing the IoT based Laser Security System (IoT-LSS) designed to enhance perimeter security and intrusion detection capabilities:
- Methodology: Enhancing Perimeter Security with IoT-Based Laser Security Systems. Site Assessment: Begin with a thorough assessment of the site where the IoT-LSS will be deployed. Identify critical areas, potential intrusion points, and environmental factors that may affect the system's performance.
- Perimeter Configuration: Determine the layout of the laser emitters and detectors, ensuring complete coverage of the perimeter while accounting for any obstructions or irregularities in the terrain.
- IoT Device Integration: Plan the integration of additional IoT devices, such as cameras, motion sensors, and environmental sensors, based on site-specific requirements.
- Hardware Installation: Laser Emitters and Detectors: Install the laser emitters and detectors at designated positions, ensuring alignment and calibration to create the laser fence.
- IoT Devices: Set up and install any additional IoT devices in accordance with the site assessment and integration plan. IoT Controller: Install the central IoT controller, connecting it to the laser detectors and other IoT devices. Ensure that the controller is securely housed and protected from environmental factors.
- Software Configuration: IoT Controller Setup: Configure the IoT controller to communicate with the laser detectors and IoT devices. Set up communication protocols and establish secure connections.
- Cloud-Based Platform: Set up the cloud-based platform for data storage and real-time analysis. Configure user access and notification preferences.
8. Calibration and Testing: Laser Calibration: Carefully calibrate the laser emitters and detectors to establish a reliable laser fence. Verify that the lasers are functioning correctly and are not affected by environmental conditions.
9. Sensor Calibration: Calibrate the IoT sensors, including cameras and motion detectors, to ensure accurate data collection and response.
10. System Integration: Test the integration between the IoT controller, laser detectors, and other IoT devices to ensure seamless data flow and communication.
11. Real-Time Monitoring and Alerts: Monitoring Interface: Configure the real-time monitoring interface, allowing security personnel to access data and receive alerts remotely.
12. Alert Notifications: Establish a notification system that sends alerts to designated personnel through various channels (e.g., email, SMS, mobile apps) in the event of a breach or suspicious activity.
13. Training and User Education: Personnel Training: Train security personnel on the operation and monitoring of the IoT-LSS. Ensure they understand how to respond to different types of alerts and breaches.
14.. User Education: Educate end-users and stakeholders about the system's capabilities, limitations, and best practices for maintaining security.
15. Ongoing Maintenance and Optimization: Regular Inspections: Conduct routine inspections of the system to ensure all components, including lasers and IoT devices, are functioning correctly.
16. Data Analysis: Continuously analyse the data collected by the system to identify patterns, trends, and potential security vulnerabilities.
17. System Updates: Keep the system and software up to date with the latest security patches and improvements.
18. User Feedback: Encourage feedback from security personnel and end-users to make necessary adjustments and optimizations.
By following this methodology, organizations can effectively implement an IoT-based Laser Security System (IoT-LSS) to enhance their perimeter security and intrusion detection capabilities while minimizing the risk of false alarms. This comprehensive approach ensures the system's reliable and efficient operation, providing a robust security solution for safeguarding critical assets.
IV. ACKNOWLEDGEMENT
First and foremost, we extend our heartfelt appreciation to the benevolent God for His continuous kindness and blessings throughout the course of this project. We would like to express our sincere gratitude to the Department of Computer Engineering at Pune Institute of Computer Technology, Pune, for granting us the opportunity to undertake this endeavour. Our thanks also go out to Prof. Ashwini Bundele, guide of our project, for his invaluable suggestions and collaboration. We’d like to genuinely acknowledge our teachers for their unwavering guidance and support. The remarkable success of this project would not have been possible without the invaluable assistance of our loved ones in conducting the research and their unwavering encouragement throughout the journey.
Conclusion
The IoT-based Laser Security System (IoT-LSS) offers a reliable, intelligent, and effective approach to perimeter security and intrusion detection, addressing the limitations of traditional security systems. Its ability to reduce false alarms, provide real-time monitoring, and integrate with other security technologies makes it a promising solution for safeguarding critical assets in various settings. The IoT-LSS represents a significant advancement in the field of security technology and serves as a testament to the ever-evolving landscape of perimeter security.
References
[1] Pranava Madan, Lakshay Dhama , Rajiv Dahiya , Ruchika Doda. A Review Paper on Arduino Research Papers. [2] Suman Singha, Debasis Maji. LASER SECURITY SYSTEM. International Journal of Scientific & Engineering Research, Volume 7, Issue 4, April-2016 214 ISSN 2229-5518. After Simulation it has been seen that it is very much efficient, reliable, easily maintainable, tiny in size. Where the other devices in the market are not efficient, various hazards are the in maintenance. [3] Banerjee, M. (2017). House Security System. Retrieved February9,2019,from https://electronicsforu.com/electronics projects/hardware-diy/low-cost-lasersecurity-system. [4] Harshal Hemane, Debarati Sen. LASER BASED SECURITY SYSTEM FOR HOME. Presented here is a security system that uses an inexpensive laser torch which is usually available with a key ring. The advantage of this security lock is that you can use any laser torch or pointer that is easily available in toy shops. [5] Deepika, Rishu Bhatia. Laser Technology: A Review. The principle of a laser is based on stimulated emission within an amplifying medium and Interaction of electromagnetic radiation with matter causes absorption and spontaneous emission.
Copyright
Copyright © 2023 Aryan Dongale, Avinash Marbhal, Ritik Matere, Prof. Ashwini Bundele. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET56803
Publish Date : 2023-11-19
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

