Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Mitigating Sink-Hole Attacks for IoT Security using Probe Routing
Authors: Mr. Venkatesh Prasad B. S., Amir Ahmed Khan, Bhavani K S, Syed Nayamathulla B, Kavya K R
DOI Link: https://doi.org/10.22214/ijraset.2022.45957
Certificate: View Certificate
Abstract
Internet of Things (IoT) applications have been filling altogether as of late, be that as it may, the security issue has not been all around read up in the writing for the IoT environment. The sinkhole assault is one of serious disastrous assaults for IoT as it is not difficult to send off the assault and hard to shield it. In this paper, a Probe Route based Defence Sinkhole Attack (PRDSA) conspires is proposed to oppose Sinkhole assault and assurance security for IoT, which is the primary work that can recognize, sidestep and find the sinkhole simultaneously. The PRDSA plot proposes a directing instrument joining the far-sink invert steering, equivalent bounce steering, and least jump directing, which can successfully evade the sinkhole assaults and track down a protected course to the genuine sink, with the goal that the plan can accomplish better sinkhole discovery. All the more significantly, the PRDSA conspire beats the restriction of past plans that they can\'t find the sinkhole. During the discovery of the sinkhole assault, the PRDSA plot requires the hubs and the sink hub to return the mark of the data (e.g., IDs, and so on), so the area of the sinkhole not entirely set in stone. Moreover, the PRDAS plot basically uses the qualities of organization energy utilization. The test course of sinkhole assault predominantly happens in the district where the excess energy exists. Subsequently, the PRDSA plot little affects the organization lifetime.
Introduction
I. INTRODUCTION
The Internet of Things (IoT) is the organization for structures, gadgets, vehicles, instruments, actual articles as well as different thing installed with circuits, hardware, sensors, programming as well as organization availability that allows items to gather as well as information trade. The Internet of Things allows the identifying and regulator of articles across the ongoing association. System, setting out open entryways for more clear coordination into PC based structures and augmentation adequacy and accuracy for the genuine world. When 1982, the possibility of an association for splendid contraptions was inspected, with a changed Coke machine at Carnegie Mellon University transforming into the principal web related device to report its stock. As well as the coldness of as of late stacked drinks. Kevin Ashton is a British trailblazer in innovation who is known for creating the expression "Web of Things" to depict a framework where the Internet is associated with the actual world through omnipresent sensors. Without human intercession, IoT interface. Some primer IoT applications in the medical services, transportation and auto ventures have proactively been created. IoT advances are in their baby stages; notwithstanding, the reconciliation of items with sensors on the Internet has created numerous new turns of events. IoT improvement includes various issues like framework, correspondences, connection points, conventions and norms. Nonetheless, during the time spent framing this is dependent upon the points of view taken, the specific definition for IoT remains. As a rule, IoT was classified as "dynamic worldwide organization framework with standard-based self-setup capacities and correspondence conventions". The aim of this paper is to give an overall idea to engineering, IoT as well as different layers in IoT, a few fundamental terms related to it as well as the administrations gave.
II. RELATED WORK OR LITERATURE STUDIES
- Liu In misfortune and-postpone delicate remote sensor organizations (WSNs), particularly when the obligation patterns of hubs are very low, it is a test to guarantee that information can be sent to sink hubs with high unwavering quality and low deferral. To resolve this issue, in this paper, we propose an information assortment plot named Adaptive Virtual Relaying Set where a bunch of hand-off hubs with additional dependable associations with the source hub is chosen to shape its Virtual Relaying Set to assist with communicating parcels. In ring-based WSNs, every hub in a VRS sends parcels thusly to the upper ring before the transmission is effective, or the bundle is dropped on the off chance that they all come up short. Thusly, the bigger the VRS (inferring more retransmission risks), the higher the bundle transmission unwavering quality and the lower the defer will be. Then again, as the shipper hub needs to remain dynamic during the transmission stage, having an enormous VRS will cause immense energy utilization.
Joined with the way that the energy utilization of various pieces of WSNs is unequal, hubs in the close sink region (i.e., areas of interest) have very high energy cost while hubs in the far-sink region (i.e., non-areas of interest) actually have adequate energy remaining when the organization bites the dust. The principal thought of the AVRS is the accompanying guideline.
2. AD. Wood Sensor networks hold the commitment of working with huge scope, continuous information handling in complex conditions, assisting with securing and screen natural, military, wellbeing basic, or home grown frameworks and assets, Denial-of-administration assaults against such organizations, in any case, may permit genuine damage to general prosperity and prosperity.
Without authentic security components, organizations will be restricted to restricted, controlled conditions, nullifying a large part of the commitment they hold.
To recognize forswearing of-administration weaknesses, the creators investigated two compelling sensor network conventions that didn't at first think about security. These models display that idea of security at setup time is the best method for ensuring productive association course of action.
3. H. Wang The IoT is quite possibly of the main late development in data advancements, which has drawn in broad consideration from both industry and the scholarly world because of its expected effect on different systems administration related fields. The fast improvement in IoT advances has brought about far and wide utilization of this arising organizing worldview in different disciplines. Then again, IoT faces a few difficulties that should be completely managed, among which versatility and energy productivity are two basic issues.
Geography control offers a promising way to deal with planning a huge scope and energy-effective IoT. In this article, we first present a scientific categorization of as of now accessible geography control calculations, and afterward propose a methodical way to deal with geography development in IoT to accomplish versatility and energy productivity. We plan to furnish specialists and experts with a 10,000 foot view of the momentum research status around here, and trust that this article might persuade more scientists to take part in enormous scope IoT plan, improvement, and sending.
III. MOTIVATION
- Any system which is required to be secured might have weakness or vulnerabilities which would be targeted by an attacker.
- Algorithm that performs better compared to current security algorithms in IOT devices.
IV. PROBLEM DEFINITION
Sinkhole is a very unsafe assault in WSNs and no viable .Sink-opening alludes to the accompanying assault: WSNs are self-coordinating organizations, where sink assumes a critical part in correspondence.
As a general rule, the information of all hubs in the organization will be sent to the sink by means of multi-bounce steering. Consequently, any assault that can hinder the correspondence courses of sensor hubs to the sink can actually hurt the WSNs.
The Sink-opening assault is such an assault that impedes the correspondence between the sensor hubs and the sink. In WSNs, the steering from sensor hubs to sink is normally founded on bounce by-jump directing component that is, every hub records the base builds up to the sink from its own and its neigh-exhausting hubs.
At the point when the information should be directed to the sink, the sensor hub chooses the neighbour hub with least jump build up to the sink to advance the information.
Without even a trace of a sinkhole assault, every hub records the right bounce build up to the sink. In any case, under such directing plan, the sinkhole can send off the append as follows: the foe hub (otherwise called sinkhole) erroneously publicizes its bounce build up to the sink which is more modest than its genuine jump build up to the sink. Different hubs that are close to the foe hub will imagine that they have found a more limited course to the sink through the foe hub, and afterward they course their information to the foe hub.
The recognition and guard of the assault depend on the current steering instrument. Accordingly, it is hard for the security discovery plot in view of traditional directing component to identify the sinkhole assault.
V. PROBLEM STATEMENT
The proposed guard plot in view of test course in this paper is chiefly utilized for the location and protection of sinkhole assaults. The security objectives of the proposed plot are to distinguish, keep away from sinkhole and decrease information misfortune for a minimal price.
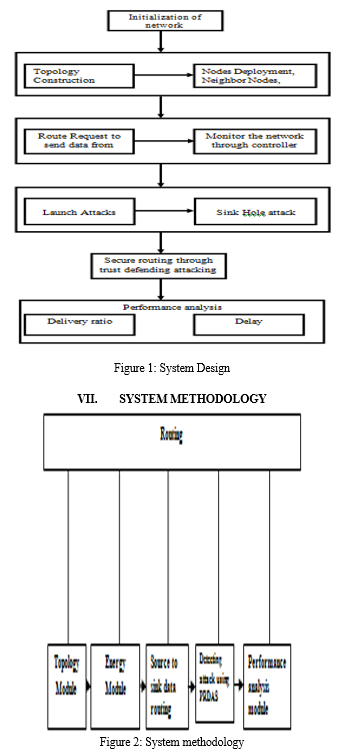
VI. SYSTEM DESIGN
VIII. IMPLEMENTATION
The execution period of any task advancement is the main stage as it yields the last arrangement, which takes care of the front and canter concern. The execution stage incorporates the genuine appearance of the contemplations, which are conveyed in the assessment document and made in the arrangement stage. Execution should be ideal preparation of the arrangement record in a sensible programming language to achieve the crucial final product. Every now and again the thing is obliterated as a result of wrong programming language picked for execution or prohibited procedure for programming. It is better for the coding stage to be clearly associated with the arrangement ease in the sense if the arrangement is the extent to which thing arranged terms, execution should be undeniably conveyed in an article arranged way. The execution stage in a situation project by its own doing. It includes
- Careful arranging
- Investigation of the on going framework and the imperatives on execution.
- Training of staff in the recently evolved framework.
Execution of any product is constantly gone before by significant choices in regards to determination of the stage, the language utilized, and so forth these choices are in many cases affected by a few factors, for example, genuine climate in which the framework works, the speed that is required, the security concerns, and other execution explicit subtleties. There are three significant execution choices that have been made before the execution of this task. They are as per the following:
a. Selection of the stage
b. Selection of the programming language for improvement of the application.
c. Coding rule to be kept.
IX. SYSTEM IMPLEMENTATION
X. COMPARISON OF RESULT
Cross breed based interruption identification approach utilized the blend of both peculiarity and mark based. This approach distinguished sinkhole assault however was intended for static WSN. It created less bogus positive rate. A non-cryptographic is another methodology which recognized sinkhole assault yet it made high organization above. Every one of the methodologies figured out how to recognize, distinguish and gave protection from sinkhole assault. The significant downsides produce by those approaches incorporates high organization and memory above, make high misleading positive rate and some couldn't deal with portable WSN.
XI. FUTURE WORK
The future arrangement ought to zero in on decreasing high organization above, computational power, Increment identification rate and that framework should be approved in genuine sensor organization. Through this sort of approval, it will be not difficult to check in the event that their answers meet the accessible assets, like memory limit.
Conclusion
The Internet of Things (IoT) biological system empowers consistent network in various applications and has a splendid future. In any case, security subject has not been a lot of perused up in the composition for the IoT climate. Likewise, with the wide utilization of the IoT climate, the issue of security is ending up being progressively critical. The Sinkhole is notable assault and has not been all around concentrated on in the writing. The damage of sinkhole assault lies in that: regardless of whether they went after hub can detect the assault, it can\'t send the assault data to the genuine sink. In spite of the fact that there are various examinations against sinkhole assault, there have not been some great and proficient recognition and area strategies for sinkhole assault. The creative savvy techniques for network protection are earnestly required for such arising patterns and exploration challenges. In this dad per, a test course based sinkhole assault safeguard conspire was proposed, which can successfully recognize and find sinkhole at-tack. The primary commitment of the proposed PRDSA plot is that it gives a powerful means to sidestep the sinkhole assault, which isn\'t accessible in existing plans.
References
[1] A. Liu, Z. Chen, N. Xiong, \"An Adaptive Virtual Relaying Set Scheme for Loss-and-Delay Sensitive WSNs,\" Information Sciences, vol. 424, pp. 118-136, 2018. [2] AD. Wood, JA. Stankovic, \"Denial of service in sensor networks.\" Computer, vol. 35, no.10, pp. 54-62, 2002. [3] J. Huang, Q. Duan, CC. Xing, H. Wang. \"Topology control for building a large-scale and energy-efficient internet of things,\" IEEE Wireless Communications, vol. 24, no. 1, pp. 67-73, 2017. [4] Ganeriwal,Saurabh,Balzano,Laura K.,Srivastava Mani B.,“Reputation-based framework for high integrity sensor networks”. ACM Transactions on Sensor Networks (TOSN), 2004, 4.3: pp. 1-37. [5] Yao, Zhiying, Kim, Daeyoung, Doh, Yoonmee Plus, “Parameterized and localized trust management scheme for sensor networks security”,IEEE International Conference on Mobile Ad Hoc and Sensor Systems. IEEE, 2006. pp. 437-446. [6] Atakli, Idris M., “Malicious node detection in wireless sensor networks using weighted trust evaluation”, Proceedings of the 2008 Spring simulation multiconference, pp.836-843. [7] Challa, S.; Wazid, M.; Das, A.K.; Kumar, N.; Reddy, A.G.; Yoon, E.; Yoo, K. Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications. IEEE Access 2017, 5, 3028–3043. [8] Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener.Comput. Syst. 2013, 29, 1645–1660. [9] Messerges, T.S.; Dabbish, E.A.; Sloan, R.H. Examining smart-card security under the threat of power analysis attacks. IEEE Trans. Comput. 2002, 51, 541–552. [10] Ryoo, J.; Han, D.; Kim, S.; Lee, S. Performance Enhancement of Differential Power Analysis Attacks with Signal Companding Methods. IEEE Signal Process. Lett. 2008, 15, 625–628. [11] Rajan, A.; Jithish, J.; Sankaran, S. Sybil attack in IOT: Modelling and defenses. In Proceedings of the International Conference on Advances in Computing, Communications and Informatics (ICACCI’17),Udupi, India, 13–16 September 2017; pp. 2323–2327.
Copyright
Copyright © 2022 Mr. Venkatesh Prasad B. S., Amir Ahmed Khan, Bhavani K S, Syed Nayamathulla B, Kavya K R. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET45957
Publish Date : 2022-07-24
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

