Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Anomaly based Intrusion Detection using Neural Networks in 5G Network
Authors: Thota Guna Durga Prashanth, Pendli Rishith Reddy
DOI Link: https://doi.org/10.22214/ijraset.2021.38691
Certificate: View Certificate
Abstract
Ensuring the organizations of tomorrow is set to be a difficult space due to expanding digital protection dangers and enlarging assault surfaces made by the Internet of Things (IoT), expanded organization heterogeneity, expanded utilization of virtualisation innovations and circulated structures. This paper proposes SDS (Software Defined Security) which is a method gives mechanized, adaptable and versatile framework. SDS will tackle momentum progresses in AI to plan a CNN (Convolutional Neural Network) utilizing NAS (Neural Architecture Search) to distinguish irregular organization traffic. SDS can be applied to an interruption location framework to make a more proactive and start to finish protection for a 5G organization. To test this presumption, ordinary and irregular organization streams from a mimicked climate have been gathered and examined with a CNN. The outcomes from this strategy are promising as the model has recognized harmless traffic with a 100% exactness rate and irregular traffic with a 96.4% identification rate. This exhibits the viability of organization stream investigation for an assortment of normal pernicious assaults and furthermore gives a suitable alternative to discovery of encoded vindictive organization traffic.
Introduction
I. INTRODUCTION
In the course of the last decade, dramatic expansions in processing power has permitted AI models like neural organizations to work with more noteworthy effectiveness and convey progressively precise outcomes. This thusly has prompted numerous original utilizations of AI to be imagined from customary spaces of examination like discourse acknowledgment and PC vision. In this paper one such clever application will be explored, the use of a CNN to investigate network traffic determined to give a versatile security answer for the assorted danger scene of 5G organizations. This application will be executed by gathering harmless and bizarre organization stream information from a reenacted climate and utilizing these streams as the info information for a CNN. A strange organization stream can be characterized as conduct that is surprising or doesn't fit with ordinary traffic designs for a specific client, business or element. This paper will accept irregular organization streams as malevolent for testing purposes, but in a true situation bizarre traffic may not be vindictive however is as yet commendable for investigation because of potential future business impacts. The format of this paper is as per the following, initially the 5G security scene will be explored, this incorporates looking at the current climate corresponding to the security models that 5G can acquire from LTE (Long Term Evolution) and current 3GPP (third Generation Partnership Project) advancements in 5G security. Future security worries for 5G organizations will then, at that point, be inspected, these incorporate how the dramatically developing number of IoTdevices is changing the security scene, dealing with numerous innovations, expanded virtualisation dangers, overseeing conveyed models and organization cuts. An answer will then, at that point, be proposed through the execution of a SDS framework which uses AI to a 5G organization. The framework is intended to get to traffic from both the backhaul connect into the center organization and from the interconnect interface out of the center organization to identify start to finish dangers and effectively update fitting security approaches. Also the uses of AI will be explored as far as current advances in abnormality recognition. These flow progresses around here of exploration will be talked about and uses of neural organization design will be contrasted with show the advantages of Cnn's. Further conversation will incorporate surveying the plan of a CNN with NAS and the use of autoML (Automated Machine Learning) to investigate the gave informational collection to deliver a particular CNN model design. At last the format of the gathered informational index will be analyzed and the information will be pre-handled into pictures which are satisfactory to the model. Results will then, at that point, be gathered from applying the model (Appendix A) to the informational collection and these outcomes will be assessed for their practicality and application to 5G and IoT security use cases. The objective of this undertaking is to give some knowledge into the viability of AI in interruption location applications and show how this arrangement can be totally characterized through programming permitting more prominent adaptability, versatility and movability in a 5G organization.
II. 5G NETWORK SECURITY ENVIRONMENT
Ecological necessities and danger models are changing as pernicious entertainers become further developed and organizations become more mind boggling and heterogeneous. IoT gadgets are likewise anticipated to increment from the current number of 27 billion gadgets to 75 billion by 2025, this is a further reason for worry in guaranteeing these gadgets can not be utilized in assaults against versatile organizations . Generally portable organizations have been worked in view of safety starting from the earliest stage, using various protections carried out in all layers of the organization. This is a decent sign for the plan of future 5G organizations, but organizations will turn out to be progressively heterogeneous as heritage, LTE and 5G organization traffic must be upheld all the while and have expanded dependence on programming based and virtualisation advances. The huge distinction in 5G organizations in contrast with LTE organizations will bring a lot more noteworthy security hazards and is a reason for worry for network administrators in keeping a safe, steady and solid help.
A. Current Threat Landscape
Media transmission organizations can be separated to incorporate four significant intelligent components these are the radio access organization, center organization, transport organization and between interface organization. Each of these organization components comprises of three planes which are each liable for conveying various kinds of traffic. A graphical outline of how these components communicate is displayed in Figure 1.
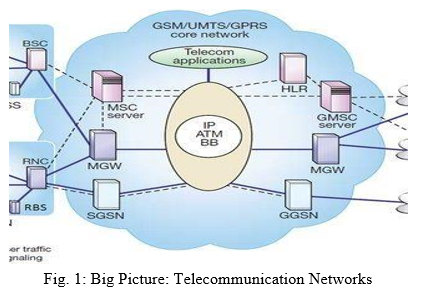
These are characterized as the control plane which conveys flagging traffic, the client plane which conveys the payload (real traffic) and the administration plane which conveys the managerial traffic . According to a security point of view every one of the three of these planes are presented to interesting dangers and furthermore uniform dangers which identify with security each of the three planes can be presented to one of a kind dangers and there are additionally uniform dangers which can influence each of the three planes all the while. Organization security is executed into media transmission networks in the accompanying four stages :
- Standardisation: Operators, merchants and partners set principles for how networks all around the world will work. Norms are likewise characterized comparable to securing networks against a noxious entertainer.
- Network Design: Network merchants configuration, create and execute the concurred principles into practical organization components and frameworks, guaranteeing the final result is both useful and secure.
- Network Configuration: During the organization sending stage, networks are designed to accomplish a set security level, this is basic in setting security boundaries and further fortifying both organization security and flexibility.
- Network Deployment and Operation: This is the functional period of the organization, accomplishing characterized security levels is subject to suitable organization sending and activity.
As far as 5G, this innovation can be characterized as not just giving one more steady redesign as far as speed and inactivity yet rather an empowering agent of another arrangement of administrations and use cases, with the most remarkable selling reason behind 5G being the acknowledgment of a genuine IoT and between organized climate that will affect all pieces of society . Anyway the primary factor that will decide if 5G can satisfy its latent capacity is the subject of how secure and stable can 5G convey these new administrations?
Traffic sensors and Vehicle To-foundation administrations are one use instance of IoT gadgets and it is important that even these essential gadgets are ensured as they are profoundly powerless against DDoS (Distributed Denial of Service) assaults. An unmistakable illustration of compromised IoT security is the Mirai assault that figured out how to control 600,000 weak IoT gadgets in a botnet, applying monstrous DDoS assaults on high profile administrations like OVH and Dyn . Luckily past media transmission networks have guaranteed that security is a top building concern, which is uplifting news for 5G. For instance comparable to LTE security the 3GPP Release 8 mixed it up of cutting edge security and validation systems through hubs, for example, the administrations ability worker, while Release 11 gave extra capacities to the center organization for secure access . These worries of trust and verification inside the organization additionally extend to 5G organizations as 3GPP Release 15 adds two compulsory validation alternatives for5G and constructs a trust model through key partition . In this manner LTE network security gives an establishment to empowering future 5G security measures. As far as actual layer remote security the media communications industry is respected in contrast with other remote innovations, even a cell phone's utilization of authorized range adds extra layers of safety to support forestalling listening in on information, voice and video traffic . Notwithstanding this top to bottom degree of safety plan there are still regions which should be tended to in the 5G security model. This incorporates new assault surfaces presented by the more noteworthy utilization of cloud and edge figuring, just as the union of 5G with conventional organizations making new assault vectors. The methodology taken in this paper by applying irregularity discovery is the endeavor to identify all traffic that is bothersome in the organization, this implies that malevolent traffic that impacts both the organization and potential end clients can be distinguished before to limit antagonistic impacts. Malevolent assaults can be summed up into two classes zero-day assaults and the very beginning assaults. Zero-day assaults are dangers that don't have a current finger impression or mark, dayone assaults are dangers that have a mark or finger impression and can be viably relieved. The ultimate objective of abnormality location is to give a quicker and more proactive reaction to already concealed (multi day) dangers and proper alleviation.
B. Future Security Concerns
Notwithstanding the new administrations and abilities that 5G organizations will give to clients, 5G will bring a large group of new security concerns and contemplations. These security challenges for 5G can be stalled into four primary categories,the the executives of IoT/V2X/M2M (Vehicle to X, Machine to Machine), conveyed designs, virtualisation and numerous advancements . IoT gadgets themselves are modest gadgets intended for a particular use and security is typically a bit of hindsight, the vast majority of these gadgets don't have their own IP stack, not to mention an inbuilt security framework. Correspondence to an end client from the IoT gadgets is additionally one more reason for worry because of distributed correspondence having no regulator between parties, this is a significant danger surface. Circulated design identifies with the partition of control and client plane. For instance customarily a bundle center organization is made out of all equipment parts situated in a server farm and these parts have known boundaries and interfaces. Anyway with 5G, center parts can be conveyed on the edge and because of the idea of 5G being a cloud local design these parts are likewise now on cloud workers. This makes new danger surfaces because of the additional trouble of dealing with an appropriated bundle center. The weighty utilization of virtualisation implies that correspondence between parties is online and achieved using API's (Application Programming Interfaces), these API's don't have set interfaces and characterized normal conventions in contrast with a LTE organization, accordingly this makes an extra danger surface. 5G likewise turns into one more organization to oversee in the heterogeneous blend of organizations presently in activity. Security measures likewise need to address getting the availability components between 3G, LTE and 5G organizations. A general perspective on the 5G danger scene is displayed beneath in Figure 2, featuring these security difficulties and organization portions that are in danger. Dangers can be broken into classes dependent on what portions of the organization they are affecting:
- User Equipment Threats: Mobile botnets can dispatch DDoS assaults on various organization levels affecting 5G framework, web workers and client gear. The objective is to bring administrations disconnected.
- Cloud Radio Access Network Threats: Rogue base station danger to work with a MITM(Man in the Middle) assault, this assault can think twice about data, alter data, track clients or cause DoS assaults. Take advantage of 5G/LTE between systems administration and dispatch downsize assault.
- Core Network Threats: Vulnerable to IP (Internet Protocol) based assaults from the web, a botnet can dispatch client plane and control plane assaults to corrupt or put basic center foundation disconnected.
- Network Slicing Threats: virtualisation based dangers because of the dependence on the security of the hypervisor. Need to guarantee segregation of cut capacities and assets from different cuts, additionally validation from client hardware working on a cut.
- SDN (Software Defined Networking) Threats: Separation of control and client plane permits a noxious client to assault the connection among control and client plane, a DoS (Denial of Service) assault could be performed or control could be acquired over network components.
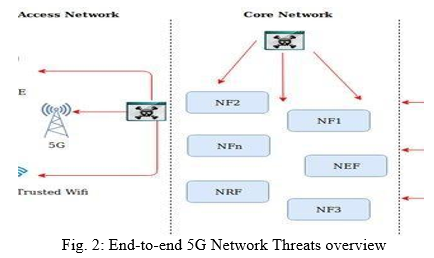
6. Center Network Elements: Network Function (NF, NFn), Network Exposure Function (NEF), Network Repository Function (NRF) Managing start to finish encoded traffic is one more thought in the advancing 5G danger scene, as traffic perceivability becomes restricted inside 5G organizations because of encryption and web benefits further scramble their traffic. Scrambled traffic has expanded by over 90% step by step, with an anticipated measure of 80% of all web traffic to be encoded in 2019 . The encryption of organization traffic permits a lot more noteworthy degrees of protection and security, but this equivalent encryption impedes network administrators' perceivability of traffic and accordingly the capacity to decide whether this traffic is malignant or harmless. Versatile, cloud and web applications rely upon all around executed encryption systems, using keys and testaments to confirm trust. The upsides of encryption are additionally its hindrances as vindictive clients can utilize encryption to dodge recognition and secure their malignant exercises.
The issue then as far as security is that most of associations don't have the instruments or answers for oversee conceivably malevolent encoded traffic and frameworks are not set up that can viably identify vindictive scrambled traffic without execution effects on the organization . Customary methods, for example, profound bundle examination become more hard to proceed as traffic would should be unscrambled sooner or later in the organization, investigated and afterward re-scrambled, this would be an asset and time serious cycle. Rather both encoded and decoded traffic can be investigated with stream related measurements. An organization stream can be characterized as a surge of traffic with a typical arrangement of identifiers . Breaking down stream measurements with AI will permit the identification of malware in encoded and decoded traffic, without the need to unscramble and yet again scramble each stream.
C. 5G SDS Implementation Architecture
5G organizations and their significant components like the CRAN (Cloud Radio Access Network) and center organization are virtualized, consequently totally characterized through programming. A comparative methodology can be taken for executing a computerized security framework through SDS. Figure 3. beneath shows a potential execution of a SDS framework in a 5G organization. A duplicate of an adequate measure of traffic from both the backhaul interface and from the center organization connection can be investigated to give start to finish network inconsistency identification. A duplicate of information is taken for investigation and to fabricate profiles of characterizing harmless and irregular traffic for the model, likewise by replicating information there will be no effects on network execution while the model breaks down the information. The information is then pre-prepared to be in a structure proper for the machine 4 learning model and examined for abnormalities, any distinguished inconsistencies are then put away in the approach supervisor data set with the relating traffic highlights. These arrangements are then shipped off a VNF (Virtual Network Function) administrator which would then be able to refresh the proper IDS (Intrusion Detection System) module in the center organization. In view of the time it takes for the model to deal with the information, set timetables can be characterized for running the model to guarantee strategies in the IDS Module are stayed up with the latest and to additional upgrade learning of the AI model. The key advantages are the capacity to mechanize the location, information base updates and suitable activity of any malignant streams.
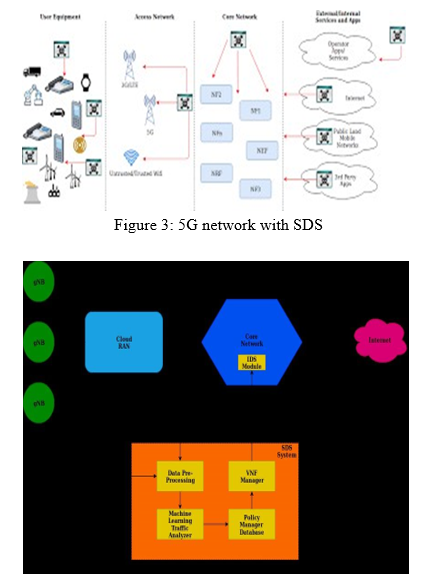
Figue 4. shows how this SDS framework can likewise be sent on explicit organization cuts to screen traffic streams and fabricate harmless and irregular traffic profiles dependent on the necessary particulars for that cut. The design of the chart centers around the partition of CP (Control Plane) and UP (User Plane), with UP's living either in the organization center or in the C-RAN, UP's can dwell in the C-RAN in case being nearer to the edge is needed for inertness reasons, CP's live in the organization center to unify control of the organization. C-RAN components are circulated including the vBBU's (virtualized Baseband Units), MEC (Mobile Edge Computing) applications and Up's. The shaded lines show the sensible associations between the SDS framework and different organization parts, cut information is gotten to both from the principal DC (Data Center) to screen backhaul traffic from the C-RAN and furthermore from the dissemination of organization cuts inside the center organization. The critical advantage of a SDS framework is that it tends to be conveyed in various pieces of the organization productively and with minimal expense. By creating programming characterized 5G security instruments in a cut based methodology, abnormality examples can be characterized per cut. One illustration of this is preparing the model to distinguish invasion assaults for little IoT gadgets working on one organization cut that could be conceivably utilized in botnets for DDoS assaults. Contingent upon administrator prerequisites each SDS framework is customisable to their requirements.
III. CONVOLUTION NEURAL NETWORK ANOMALY DETECTION
Deep learning is a space of AI which includes the plan of multifaceted neural organizations, which are basically numerically based neuron-like designs that utilization numerous factors to settle a mind boggling condition. To foster a neural organization for order of text or pictures requires a lot of design designing to acquire an organization that is most appropriate to the given informational index and has an adequate degree of precision. This part will hence investigate current advances in the space of AI based abnormality identification and afterward explore how strategies, for example, autoML and NAS can upgrade model plan to permit the plan of CNN structures that are both adaptable and exceptionally improved for the kind of information they are preparing on.
A. Current Advances
Organization interruption identification identifies with the issue of observing and separating ordinary organization streams from unusual streams which can think twice about security of a framework. The two governments and associations contribute intensely to track down a solid answer for shield their data resources and assets from noxious access, this has brought interruption identification frameworks to the bleeding edge of the network protection scene . As proposed by Denning creating interruption location frameworks that utilize AI strategies is to distinguish strange utilization designs and unusual traffic which might flag an endeavored interruption of the organization. This idea prompted the formation of another kind of IDS dependent on learning calculations instead of physically refreshing marks from recently recognized interruptions. In the course of the most recent thirty years different AI strategies have been applied in a customary methodology for creating network oddity recognition models. These methodologies utilized regulated, unaided and semi-managed learning calculations to propose an answer for oddity recognition. Hence inconsistency recognition is definitely not another space of study in AI applications and flow research has investigated an assortment of AI based applications. Anyway some normal issues emerge, for example, low precision 5 levels due to problematic model plan, ridiculously high exactness levels because of an absence of model speculation and over fitting, and furthermore the utilization of obsolete and oversimplified informational indexes. As displayed in exactness more than close to 100% is accomplished utilizing a diverse neural organization, but the informational collection utilized is the KDD99 dataset, an informational index which is 20 years of age and doesn't address current powerful organization conditions. Irregularity identification itself can be most effortlessly demonstrated as a characterization issue in regulated learning . Managed learning implies that named information is utilized to prepare the abnormality recognition model. The objective of this sort of preparing is to arrange the test information as irregular or typical based on a particular arrangement of provisions. In this paper the irregularity identification issue will be drawn nearer from a managed learning viewpoint and utilize a CNN engineering planned utilizing NAS to endeavor to upgrade the most elevated conceivable precision levels.
Successful model plan requires a critical level of structural designing [9], for example, exhibiting that the plan of fundamental CNN's the place where additional layers are simply added for testing purposes doesn't further develop precision, giving problematic outcomes at under 80% identification rate. show the adequacy of here and there examining on information to balance volumes of abnormality and harmless information, accomplishing a discovery pace of 99.99% utilizing arbitrary woodland and 99.30% utilizing three layered profound neural organizations, these exceptionally high outcomes are probably not going to address genuine identification levels and give the impression of an over fitted model and an absence of speculation. Compelling order of both harmless and bizarre traffic is likewise an issue, by and large models can distinguish named harmless traffic with extremely high (99-100%) exactness, but deciding peculiar traffic can be more troublesome, as displayed in where the arbitrary woodland calculation is applied to the UNSW-NB15 dataset, harmless traffic was arranged at almost 100% precision, but strange traffic was characterized at 82%, this implies that 18% of atypical traffic was basically undetected. The methodology of this paper endeavors to amend and address a portion of these normal issues. This is done in two primary ways by choosing the most modern IDS informational index, the CICIDS2018 which reproduces a genuine climate and is clarified exhaustively further on. Also, besides by utilizing a CNN model dependent on NAS, which has accomplished probably the most elevated exactness levels in the ImageNet informational collection and utilizations a regulator to independently improve boundaries for the model. By adopting this strategy the most ideal model can be created for a particular informational collection..
B. AutoML & NAS
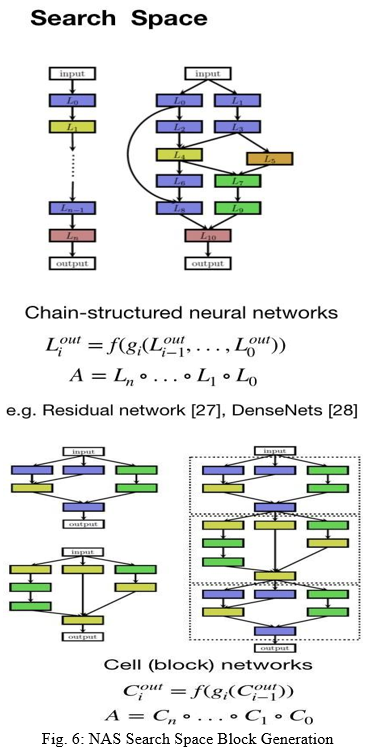
Execution Neural engineering search carries mechanization to the plan of neural organization models, this permits the most advanced model plans to be figured without the drawn-out course of actually planning, testing and changing models. This state of the art method in neural organization configuration has prompted the ascent of various robotized AI stages. In this paper Google's autoML Vision and Vision Edge stages will be used for model plan, preparing, approval and testing. The fundamental engineering which empowers these stages is NASNet (Neural Architecture Search Network) and MNasNet (Mobile Neural Architecture Search Network). Neural engineering search can be characterized as an angle based technique for finding advanced models. The construction and availability of a neural organization can be indicated by a variable length string. Accordingly it becomes conceivable to utilize a RNN (Recurrent Neural Network) as displayed in Figure 5. to create this string . The organization determined by the string is known as the kid organization and preparing the genuine informational index with the youngster organization will bring about reformist exactness increments on the test informational index. This exactness can be utilized as the prize sign to register the arrangement angle to refresh the regulator. Along these lines in the following emphasis the regulator will give a higher likelihood to designs that get a higher exactness .
Set forth plainly this implies the regulator can figure out how to work on its pursuit over the long haul and advance position of layers and squares of the neural organization [17].
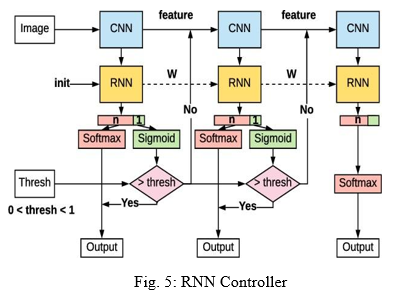
As far as execution neural engineering search utilizes the regulator to create a bunch of design hyperparameters of the organization. On account of a CNN it can foresee channel stature, channel width, step tallness, step width and various channels per layer . This interaction is then rehashed until the quantity of layers surpasses a specific worth. This issue with NAS is applying it to an exceptionally enormous informational collection is amazingly computationally serious. Consequently this procedure is applied to an example of the informational collection . The NAS search space is characterized so the intricacy of the engineering is free of the profundity of the organization and the size of info pictures. It accomplishes this by separating all CNN's in the inquiry space into cells with indistinguishable design yet various loads as displayed in Figure 6 Therefore looking for the most ideal engineering can be diminished to looking for the best cell engineering. Via looking for every particular cell design, speed is significantly expanded and the cell is bound to have better speculation. In view of this singular cell preparing approach, organizations can be upgraded for speed or exactness relying upon the hunt space size. This permits the neural organization to accomplish an extremely undeniable degree of exactness on the ImageNet approval informational collection at 82.7% top 1 exactness .ImageNet is the biggest information base for marked pictures containing more than 14 million pictures and has boundless use in giving a benchmark to deciding the presentation of various CNN models.
MnasNet expands the NAS search space idea by carrying out factorized progressive pursuit space . The factorized various leveled search space supports extra layer variety all through the organization and balances the size of the all out search space. This methodology brings greater adaptability into NAS as models can be intended to adjust speed versus precision. So far this methodology enjoys the greatest benefit of speed. On the ImageNet dataset the MNasNet engineering accomplished 75.2% top 1 exactness which in contrast with conventional versatile neural organization structures is 1.8 occasions quicker than MobileNetV2 and 0.5% higher precision. In contrast with NASNet results were 7.5% lower precision, but 2.3 occasions quicker in preparing pictures inside the design . In the outcomes area NASNet and MNasNET will be contrasted and tests led for 24 hours and 3 hours separately to evaluate the distinctions in outcomes. Inactivity and computational force is likewise an essential worry for execution purposes for this situation. By improving a neural organization that can in any case accomplish an undeniable degree of exactness, low inertness when preparing and furthermore can be run on gadgets, for example, a present day cell phone, this will permit substantially more adaptability for sending in a 5G organization.
IV. ANOMALY DETECTION DATASET
A. Data Set Environment Overview
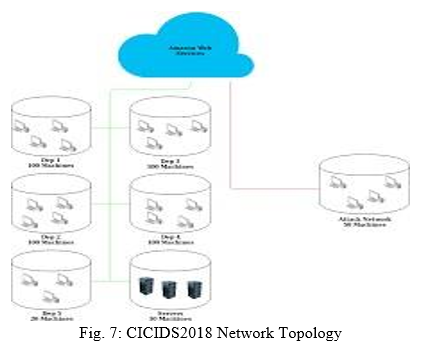
Peculiarity discovery is one of the most encouraging spaces of exploration in identifying novel assaults. Anyway its reception to genuine applications is obstructed because of framework intricacy requiring a lot of testing, tuning and assessment. Along these lines for research purposes a recreated framework can be planned with a thorough arrangement of interruptions and unusual conduct blended in with typical traffic for peculiarity identification investigation. As organization practices and malware are transforming it becomes important to have a climate that all the more precisely mimics a true situation. The information that would then be able to be caught from the framework is dynamic and gives more significant and reasonable understanding into harmless and bizarre organization traffic conduct. Lamentably customary IDS informational collections were not planned thusly, for instance the KDD CUP99 informational index or the ADFA-IDS informational collection were established in a testing climate that was just included single LAN connections and one assaulting and one safeguarding framework, this methodology addresses a static climate and gives problematic and less sensible outcomes . The IDS-2018 informational collection from the Canadian Institute of Cybersecurity is an informational index gotten from a recreated climate that endeavors to address these inadequacies. The principle objective of this informational index is to utilize a methodical way to deal with produce an assorted and exhaustive benchmark informational collection for interruption identification dependent on the production of harmless traffic and malevolent traffic profiles. The actual climate comprises of 50 assaulting machines on a casualty association with 5 divisions which incorporates 420 machines and 30 workers. The informational collection takes parcel catches of organization traffic and framework logs of each machine, just as the extraction of 80 organization highlights coordinated as streams. Figure 7. Beneath shows the general organization geography which is a typical LAN network on an AWS (Amazon Web Services) cloud stage. 6 subnets are introduced named as Dep1 to Dep5 and Servers. Dep1 to Dep4 machines have Windows 8/10 Os', Dep5 has all Linux machines running Ubuntu, Servers has distinctive MS Windows workers like App workers, dynamic registry and email. The aggressor network has Windows 8/10 machines and Ubuntu machines.
B. Network Profiles & Features
Conventions recreated in the climate are: HTTPS (HyperText Transfer Protocol Secure), HTTP (HyperText Transfer Protocol), SMTP (Simple Mail Transfer Protocol), POP3 (Post Office Protocol 3), IMAP (Internet Message Access Protocol), SSH (Secure Shell), FTP (File Transfer Protocol). Traffic types are broken into two profiles, either a B-profile (harmless traffic) or M-profile (pernicious traffic). The kinds of traffic inside these profiles is clarified in additional detail underneath. B-Profile: Describes typical traffic types mimicked through various AI calculations with various organization conventions:
- Emulates the conduct of clients by using different AI measurable investigation methods like K-Means, Random Forest, SVM and J48.
- Network highlights gathered incorporate parcel size of convention, number of bundles per stream, different examples in payload, size of payload and solicitation time dispersion of a convention. 7 The particular assaults utilized in the M-Profile are normal assaults utilized by malevolent entertainers just as infiltration analyzer.
They cover a wide assortment of situations from network based assaults, various types of HTTP DoS and DDoS, animal power assaults, online assaults and broad weaknesses. They likewise cover parts of the OWASP top 10 2019 including infusion based assaults from SQL, broken validation because of helpless secret phrase the board permitting simpler beast power assaults and security misconfigurations which permit weaknesses, for example, heartbleed due to unpatched frameworks. M-Profile depicts the assault situation for atypical traffic, six distinctive assault situations are reenacted:
a. Internal network penetration - takes advantage of utilization weakness by sending pernicious documents through email. Metasploit structure is used for abuse permitting a secondary passage to be executed on the casualty's PC.
b. HTTP DoS - Slowloris, LOIC and HOIC which cause disavowal of administration are utilized, these devices can make web workers distant. Slowloris can do this with only one machine and is best against Apache workers . Apache workers are the second most normal web workers on the web representing 26.73% of web workers.
c. Web application attacks - Web application based attacks had a go at using the Damn Vulnerable Web App (DVWA) for SQL imbuement, request implantation and limitless record move.
d. Brute power attacks - Use a word reference monster power attack containing 90 million words contrary to guideline laborers to try to acquire SSH and MySQL account information.
e. Last revived attacks - Well known shortcomings that can impact huge number of contraptions under explicit conditions and on the off chance that they are running more prepared, outdated variations of programming.
Heartleech will be utilized in this climate, it is utilized to check frameworks powerless against the Heartbleed bug, whenever frameworks are discovered they would then be able to be taken advantage of and information can be exfiltrated.
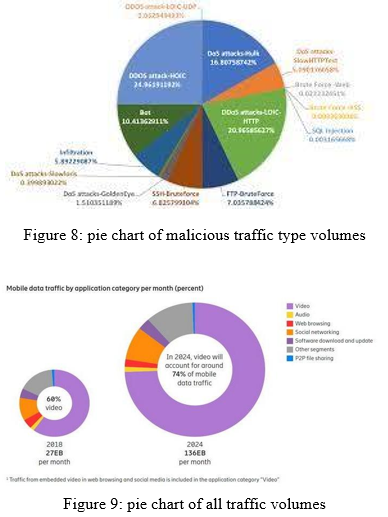
To characterize the components from these profiles, introductory crude parcel catches are changed over to organize streams for simpler examination. Utilizing CICFlowMeter bidirectional streams are created where the main parcel decides the forward (source to objective) and in reverse (objective to source) bearings. Subsequently from the 83 measurable provisions assembled from the streams like span, number of parcels, number of bytes, length of bundles, these are determined independently for both forward and turn around bearings. For TCP streams they are ended upon association teardown (when a FIN bundle is gotten) and UDP streams are ended by a stream break. Fig 8. Pie Chart of Malicious Traffic Type Volumes Fig 9. Pie Chart of all Traffic Volumes This paper will separate all named network streams into two streams for examination, irregular and harmless. Harmless comprises of all traffic portrayed in the B-Profile and abnormal is all traffic depicted in the M-Profile. Various assaults happen at various outings of a sum of 10 days or 240 hours, these assaults are scattered haphazardly inside harmless traffic. Altogether there are 2748235 abnormality streams and 6584535 harmless streams giving an aggregate of 9332770 streams in the informational collection. This is a parted of 70.55% harmless traffic and 29.45% abnormality traffic. The two pie graphs underneath in Figure 8. what's more, Figure 9. show the breakdown of traffic volumes in the informational index.
V. INTER-ARRIVAL TIME & FEATURE SELECTION
IAT (Inter-Arrival Time) can be characterized as the normal edges, parcels or streams that show up at a host throughout a specific time span ]. By looking at this element and other factual types of IAT, for example, the mean, least, most extreme and standard deviation of IAT of an organization stream, harmless traffic can be displayed to adjust to the Weibull conveyance. By demonstrating harmless traffic to the Weibull circulation, atypical traffic can accordingly be distinguished as it will cause abnormalities and deviations in the dispersion . This relationship is recognizable across bundles, streams and meetings for both TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) transport conventions in web traffic. Accordingly these IAT network stream provisions can be demonstrative of the distinction in harmless and strange streams. Flow studies show the Weibull dissemination displayed to web traffic by utilizing traffic follows caught from the WAND Research Group [31]. 24 hours of traffic 8 checking from an ISP has caught information from remote areas of interest, DSL and ethernet availability in a metropolitan climate . The information caught shows the conformance for bundles, streams and meetings as they decline from solidarity (worth of 1) to the Weibull dispersion.
Stretching out this idea to zero in on network streams, has exhibited that regardless of the assortment of organizations in size, number of clients, applications and burdens, the IAT's of harmless TCP streams likewise adjust to the Weibull circulation and explicit inconsistencies in these streams will cause deviations in rush hour gridlock. Numerous informational indexes were gathered with contrasting data transfer capacity, size and applications to check this conformance. Informational indexes that were tried in were:
MAWI3 (Measurement and Analysis on the WIDE Internet): June 2012, 1.4 million exchanges, gotten from a 150Mbps abroad spine interface among Japan and USA.
- SUT (Sharif University of Technology): June 2012, 2.4 million streams, got from web passage of SUT grounds.
- MCO: February 2011, 2.3 million streams, got from a web passage of a medium business affiliation.
- NUST1 (National University of Sciences and Technology): March 2009, 2.2 million streams, Captured from an endpoint switch masterminded in NUST, Pakistan.
- ISP NUST: got from an edge switch of a medium evaluated ISP and converged with assault streams conveyed in NUST.
While investigating the traffic streams from the above informational indexes, shows that the deviation in the Weibull dispersion is apparent when contrasting all streams with harmless streams. Explicit assault infusions into the ISP NUST informational index have additionally been examined as far as recognition rate. The assault infusion was for a SYN flood assault, a sort of DoS assault that comprises of a high volume of SYN bundles with a tiny between appearance times . This exceptional change in between appearance time causes anomalies in the Weibull circulation and permitted location of assaults. shows that a 98.8% exactness rate was accomplished with a 4.8% bogus caution rate. This exhibits the high measure of difference that some normal sorts of pernicious assaults can have on stream between appearance time. This idea shapes the reason for the component determination choice from the CICIDS2018 informational index and these suppositions will be checked in the outcomes segment. By considering these previous investigations in between appearance traffic stream conduct these ideas can be reached out to current day AI models to give obviously characterized marked information on ordering among atypical and harmless traffic streams. Component choice subsequently elaborate a two section determination measure. The initial segment is the determination of standard elements that give essential data on the stream. The subsequent part includes choosing a predetermined number of elements that show clear contrasts in qualities between a harmless and odd stream. As shown beforehand, IAT stream information can be proposed as a solid up-and-comer and all the more explicitly measurable varieties of IAT stream information can be utilized to additionally dissect these relationships. This choice to restrict include choice is to furnish the AI model with clean information and to eliminate overabundance commotion in the information that isn't significant in corresponding the connection among abnormal and harmless streams. By doing this a more effective model can be planned, with higher precision and quicker speed. 20 elements alongside an extra name section to order each stream type have hence been chosen and these are:
a. Basic Flow Features: Destination Port, Protocol, Flow Duration, Total Forward Packets, Total Backward Packets, Flow Pkts/s.
b. IAT Statistical Metadata: Flow IAT Mean, Flow IAT Standard Deviation, Flow IAT Maximum, Flow IAT Minimum, Flow IAT Total, Forward IAT Mean, Forward IAT Standard Deviation, Forward IAT Max, Forward IAT Min, Backward IAT Total, Backward IAT Mean, Backward IAT Standard Deviation, Backward IAT Max, Backward IAT Min
A. Pre-Processing Data Set
Educational file pre-taking care of incorporates changing the data into the right construction sensible for the CNN, which for the present circumstance is a 100x100x3 picture. The portrayed 20 arrangements from the instructive assortment are isolated in CSV archive plan. SV inputs are reshaped into RGB pictures of 100 x 100 x 3 size, any additional left over data under this size is discarded as all photos for the CNN are should have been of a comparable data size. This image size was picked because of giving a respectable volume of test pictures for the proportion of data open (in excess of 1000 model pictures). Generally the trade offs between using a higher diverged from a lower objective picture is that a more significant standard picture will contain better nuances when ready by the neural association, however this will set aside more effort for both planning and testing stages.
A lower objective picture will give less nuances, but more overall component depictions and the neural association will really need to plan and test the data at a speedier rate. For this paper autoML tests and builds all photos to 224 x 224 x 3 information picture size, thusly there are only two considerations, first thing the volume of pictures is more than 1000 and that sufficient component nuances are gotten. Two models are shown underneath in Figure 10 and Figure 11 of what an irregularity picture looks like conversely, with an innocuous picture. Graphically, irregularity pictures are unpredictable and tumultuous, while innocuous pictures are more common and contain some unmistakable model.
VI. ANOMALY DETECTION RESULTS
A. Methodology
Machine Intelligence Library Google TensorFlow was utilized to execute the neural organization models in this review – both the proposed and its comparator. The Dataset 2013 Kyoto University honeypot frameworks' organization traffic information was utilized in this review. It has 24 measurable provisions, 14 components from the KDD Cup 1999 dataset, and 10 extra elements, which as indicated by Song, Takakura, and Okabe (2006)might be vital in a more viable examination on interruption discovery. Just 22 dataset highlights were utilized in the review.
B. Data Preprocessing
For the examination, just 25% of the entire 16.2 GB network traffic dataset was utilized, for example ≈4.1 GB of information (from January 1, 2013 to June 1, 2013). Prior to utilizing the dataset for the examination, it was standardized first – normalization (for nonstop information, see Eq. 1) and ordering (for straight out information), then, at that point, it was binned (discretized).
z = X − µ σ (1)
where X is the component worth to be normalized, µ is the mean worth of the given element, and σ is its standard deviation.But for proficiency, the StandardScaler(). fit_transform() capacity of Scikit-learn[19] was utilized for the information normalization in this review. For ordering, the classifications were planned to [0,n − 1] utilizing the LabelEncoder().fit_transform() capacity of Scikit-learn[19]. After dataset standardization, the persistent elements were binned (decile binning, a discretization/quantization strategy). This was finished by getting the tenth , twentieth , ..., 90th, and 100th quantile of the elements, and their records filled in as their receptacle number. This cycle was finished utilizing the qcut() capacity of pandas. Binning decreases the necessary computational expense, and further develops the grouping execution on the dataset. Finally, the components were one-hot encoded, preparing it for use by the model. The GRU-SVM Neural Network Architecture the current paper proposes to utilize SVM as the classifier in a neural organization engineering. In particular, a Gated Recurrent Unit (GRU) RNN. For this review, there were 21 provisions utilized as the model info. Then, at that point, the boundaries are learned through the gating component of GRU (Equations (2) to (5)).
z = σ(Wz · [ht−1, xt ]) (2)
r = σ(Wr · [ht−1, xt ]) (3)
ht = tanh(W · [rt ∗ ht−1, xt ]) (4)
ht = (1 − zt ) ∗ ht−1 + zt ∗ ˜ht (5)
z = σ(Wz · [ht−1, xt ]) (2)
r = σ(Wr · [ht−1, xt ]) (3)
ht = tanh(W · [rt ∗ ht−1, xt ]) (4)
ht = (1 − zt ) ∗ ht−1 + zt ∗ ˜ht (5)
But with the introduction of SVM as its final layer, the parameters are also learned by optimizing the objective function of SVM (see Eq. 6). Then, instead of measuring the network loss using cross entropy function, the GRU- SVM model will use the loss function of SVM (Eq. 6).
min 1 2 ?w? 2 1 + C Õn i=1 max(0, 1 − y ′ i (w T xi + bi)) ….. (6)
Eq. 6 is known as the unconstrained improvement issue of L1-SVM. In any case, it isn't differentiable. In reality, its assortment, known as the L2-SVM is differentiable and is more consistent than the L1-SVM:
min 1 2 ?w? 2 2 + C Õn i=1 max(0, 1 − y ′i(w T xi + bi))2 ….. (7)
The L2-SVM was utilized for the proposed GRU-SVM design. With respect to the expectation, the choice capacity f (x) = si?n(wx + b) delivers a score vector for each class. Thus, to get the anticipated class name y of an information x, the ar?max work is utilized:
predicted_class = ar?max(si?n(wx + b))
The ar?max capacity will return the record of the greatest score across the vector of the anticipated classes. The proposed GRU-SVM model might be summed up as follows:
- Input the dataset highlights {xi | xi ∈ R m } to the GRU iend lmodel.
- Initialize the learning boundaries loads and inclinations with subjective qualities (they will be changed through preparing).
- The cell territories of GRU are registered dependent on the info highlights xi , and its learning boundaries esteems.
- At the last time step, the forecast of the model is processed utilizing the choice capacity of SVM: f (x) = si?n(wx + b).
- The loss of the neural organization is processed utilizing Eq. 7.
- An advancement calculation is utilized for misfortune minimization (for this review, the Adam enhancer was utilized). Advancement changes the loads and predispositions dependent on the processed misfortune.
- This measure is rehashed until the neural organization arrives at the ideal precision or the most elevated exactness conceivable.
A short time later, the prepared model can be utilized for paired order on a given information.
Information Analysis: The adequacy of the proposed GRU-SVM model was estimated through the two periods of the trial:
a. training stage
b. test stage
Alongside the proposed model, the traditional GRU-Softmax was additionally prepared and tried on the equivalent dataset. The primary period of the analysis used 80% of complete information focuses (≈3.2 GB, or 14, 856, 316 lines of organization traffic log) from the 25% of the dataset. After standardization and binning, it was uncovered through an undeniable level examination that a duplication happened. Utilizing the DataFrame.drop_duplicates() of pandas[16], the 14, 856, 316-line information dropped down to 1, 898, 322 lines (≈40MB). The second period of the investigation was the assessment of the two prepared models utilizing 20% of absolute information focuses from the 25% of the dataset. The testing dataset additionally encountered an exceptional shrinkage in size – from 3, 714, 078 lines to 420, 759 lines (≈9 MB). The boundaries for the trials are the accompanying:
- Accuracy
- Epochs
- Loss
- Run time
- Number of information focuses
- Number of bogus up-sides
- Number of bogus negatives
These boundaries depend on the ones considered by Mukkamala, Janoski, and Sung (2002)[17] in their review where they analyzed SVM and a feed-forward neural organization for interruption discovery. Finally, the factual measures for twofold arrangement were estimated (genuine positive rate, genuine negative rate, bogus positive rate, and bogus negative rate).
The observational proof introduced in this paper recommends that SVM beats Softmax work as far as expectation precision, when utilized as the last yield layer in a neural organization. This finding substantiates the cases by Alalshekmubarak and Smith (2013) and Tang (2013), and upholds the case that SVM is a more reasonable methodology than Softmax for parallel grouping. Not exclusively did the GRU-SVM model outflank the GRU-Softmax as far as forecast exactness, however it likewise beat the ordinary model as far as preparing time and testing time. Accordingly, supporting the hypothetical ramifications according to the individual calculation intricacies of every classifier. The detailed preparing precision of ≈81.54% and testing exactness of ≈84.15% sets that the GRU-SVM model has a generally more grounded prescient exhibition than the GRU-Softmax model (with preparing precision of ≈63.07% and testing precision of ≈70.75%). Thus, we propose a hypothesis to clarify the moderately lower execution of Softmax contrasted with SVM in this specific situation. To begin with, SVM was planned essentially for parallel classification[5], while Softmax is best-fit for multinomial grouping. Expanding on the reason, SVM couldn't care less with regards to the singular scores of the classes it predicts, it just requires its edges to be fulfilled. Actually, the Softmax capacity will consistently figure out how to further develop its anticipated likelihood conveyance by guaranteeing that the right class has the higher/most elevated likelihood, and the inaccurate classes.
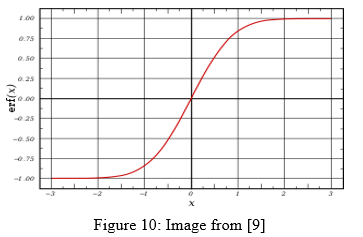
Graph of a sigmoid σ function. have the lower probability. This behavior of the Softmax function is exemplary, but excessive for a problem like binary classification. Given that the sigmoid σ function is a special case of Softmax (see Eq. 8-9), we can refer to its graph as to how it classifies a network output.
σ(y) = 1 1 + e −y
= 1 1 + 1 e y
= 1 e y + 1 e y
= e y 1 + e y
= e y e 0 + e y (8)
so
f tmax(y) = e yi Ín=1 i=0 e yi = e yi e y0 + e y1 ………. (9)
It can be inferred from the graph of sigmoid σ function (see Figure 4) that y values tend to respond less to changes in x. In other words, the gradients would be small, which gives rise to the “vanishing gradients” problem. Indeed, one of the problems being solved by LSTM, and consequently, by its variants such as GRU[3, 8]. This behavior defeats the purpose of GRU and LSTM solving the problems of atraditional RNN. We posit that this is the cause of misclassifications by the GRU-Softmax model. The said erroneous manner of the GRU-Softmax model reflects as a favor for the GRU-SVM model. But the comparison of the exhibited predictive accuracies of both models is not the only reason for the practicality in choosing SVM over Softmax in this case. The amount of training time and testing time were also considered.

As their computational intricacies propose, SVM has the advantage over Softmax. This is on the grounds that the calculation intricacy of the indicator work in SVM is just O(1). Then again, the indicator capacity of Softmax has a calculation intricacy of O(n). As results have shown, the GRU-SVM model likewise outflanked the GRU-Softmax model in both preparing time and testing time. In this way, it authenticates the particular calculation intricacies of the classifiers.
VII. DISCUSSION & FUTURE DIRECTIONS
There are numerous regions that should be viewed as when endeavoring to get 5G organizations, as the organization is so different, security turns out to be more hard to execute viably. The methodology of this paper is then to foster a start to finish observing framework for traffic that moves through the organization, this isn't in itself a conclusive security arrangement, only one piece of the general security design that is needed to get the organization. The model planned with the chose essential and IAT include set in this paper utilizing autoML has figured out how to arrange all harmless traffic streams accurately which is a generally excellent outcome, but for abnormality traffic streams 96.4% of traffic was characterized effectively, so accordingly there is still opportunity to get better. There was insignificant contrast in both the MNasNet (3 hour running time) engineering and the NASNet (24 hour running time) design, this could be because of the informational collection size. For additional model approval, testing can be directed with a bigger informational collection, testing can likewise be led with various informational collections to guarantee a healthy level of speculation in the model and to check for overfitting issues. At last recognizing any outwardly comparative harmless and irregularity pictures and testing with various elements to endeavor to isolate the contrast among harmless and atypical pictures much more could be researched. The better that an inconsistency picture and a harmless picture can be recognized, the simpler it will become to prepare the model and decrease exception information and mistakes. NAS has permitted the formation of a high level model for a particular informational index to be constructed independently and to stay away from the dreary course of manual engineering plan, the planned NAS model would now be able to be sent out into a custom application for additional testing and refinement. Generally speaking the outcomes feature the adequacy of AI based picture discovery procedures for network stream examination. This exploration could be stretched out in various ways, for example:
- Implementing unaided learning strategies to make a semi-regulated learning model, as truly most of organization traffic is unlabelled information and pre-preparing unlabelled information into spotless and coordinated marked information is a tedious interaction. Broadening this idea a harmless traffic profile could be intended for a particular organization cut utilizing unaided learning procedures for general arrangement and afterward regulated strategies for extra adjusting to check the profile.
- Building an information base that stores traffic logs, a particular volume of the logs would be taken routinely for preparing the organization, further review could be directed in how frequently to re-train the organization, with what new approaching information, how long should it require to prepare and would it be feasible to convey different cases of the neural organization, so one example can prepare on new information while one more case can be tried on existing information.
- Implement a continuous traffic checking framework with an AI constructed profile, this could be planned as a wise firewall.
- Design an upgraded trust based framework to verify trust dependent on prescient stream investigation.
Conclusion
This paper proposed an original arrangement of applying programming characterized security with AI to give start to finish insurance to 5G organizations. The underlying task scope has been satisfied and the methodology of changing over network streams into pictures for examination by a CNN has exhibited profoundly precise outcomes for the information accessible, particularly thinking about that CNN\'s are customarily streamlined for genuine picture/photo recognition. The use of a machine 11 learning based SDS framework is promising for true execution and a portion of the focuses illustrated above investigate this further. Anyway challenges still should be survived, as far as overseeing assorted and complex 5G organizations and furthermore dealing with the huge volumes and varieties of traffic that will course through them. By and large this is just the start for AI based security applications. The development in 5G organization rollouts, worldwide web use, IoT gadget availability and enormous information investigation will proceed to enlarge and make new assault surfaces. To oversee and alleviate these assault surfaces viably, dynamic and keen AI security frameworks that can react quickly to dangers will be basic.
References
[1] Martín Abadi, Ashish Agarwal, Paul Barham, Eugene Brevdo, Zhifeng Chen, Craig Citro, Greg S. Corrado, Andy Davis, Jeffrey Dean, Matthieu Devin, Sanjay Ghemawat, Ian Goodfellow, Andrew Harp, Geoffrey Irving, Michael Isard, Yangqing Jia, Rafal Jozefowicz, Lukasz Kaiser, Manjunath Kudlur, Josh Levenberg, Dan Mané, Rajat Monga, Sherry Moore, Derek Murray, Chris Olah, Mike Schuster, Jonathon Shlens, Benoit Steiner, Ilya Sutskever, Kunal Talwar, Paul Tucker, Vincent Vanhoucke, Vijay Vasudevan, Fernanda Viégas, Oriol Vinyals, Pete Warden, Martin Wattenberg, Martin Wicke, Yuan Yu, and Xiaoqiang Zheng. 2015. TensorFlow: Large-Scale Machine Learning on Heterogeneous Systems. (2015). http://tensorflow.org/ Software available from tensorflow.org. [2] A. Alalshekmubarak and L.S. Smith. 2013. A Novel Approach Combining Recurrent Neural Network and Support Vector Machines for Time Series Classification. In Innovations in Information Technology (IIT), 2013 9th International Conference on. IEEE, 42–47. [3] Kyunghyun Cho, Bart Van Merriënboer, Caglar Gulcehre, Dzmitry Bahdanau, Fethi Bougares, Holger Schwenk, and Yoshua Bengio. 2014. Learning phrase representations using RNN encoder-decoder for statistical machine translation. arXiv preprint arXiv:1406.1078 (2014). [4] Jan K Chorowski, Dzmitry Bahdanau, Dmitriy Serdyuk, Kyunghyun Cho, and Yoshua Bengio. 2015. Attention-based models for speech recognition. In Advances in Neural Information Processing Systems. 577–585. [4] C. Cortes and V. Vapnik. 1995. Support-vector Networks. Machine Learning. 20.3 (1995), 273–297. https://doi.org/10.1007/BF00994018 [5] Jeremy Frank. 1994. Artificial intelligence and intrusion detection: Current and future directions. In Proceedings of the 17th national computer security conference, Vol. 10. Baltimore, USA, 1–12. [6] Anup K Ghosh, Aaron Schwartzbard, and Michael Schatz. 1999. Learning Program Behavior Profiles for Intrusion Detection.. In Workshop on Intrusion Detection and Network Monitoring, Vol. 51462. 1–13. [7] Yohan Grember (https://stackoverflow.com/users/7672928/yohan grember). [n. d.]. Binary classification with Softmax. Stack Overflow. ([n.d.]). arXiv:https://stackoverflow.com/questions/45793856 https://stackoverflow.com/ questions/45793856 URL:https://stackoverflow.com/questions/45793856 (version: 2017-08-21) [8] Naseer and Y. Saleem, Enhanced Network Anomaly Detection Based on Deep Neural Networks, SPECIAL SECTION ON CYBERTHREATS AND COUNTERMEASURES IN THE HEALTHCARE SECTOR, Jun. 2018. [9] D. E. Denning, An intrusion-detection model, IEEE Trans. Softw. Eng., vol. SE-13, no. 2, pp. 222232, Feb. 1987. [Online].Available:http://ieeexplore.ieee.org/abstract/document/ 1702202/ [Accessed: 07-Apr-2019]. [10] A. Dawoud and S. Shahristani, Deep Learning for Network Anomalies Detection, 2018 International Conference on Machine Learning and Data Engineering (iCMLDE), 2018. [11] D. Kwon and K. Natarajan, An Empirical Study on Network Anomaly Detection using Convolutional Neural Networks, 2018 IEEE 38th International Conference on Distributed Computing Systems, 2018. [12] R. Abdulhammed and M. Faezipour, Deep and Machine Learning Approaches for Anomaly-Based IntrusionDetection of Imbalanced Network Traffic, IEEE Sensors Letters, Jan. 2019. [13] I. Alrashdi and A. Alqazzaz, AD-IoT: Anomaly Detection of IoT Cyberattacks Smart City Using Machine Leaming, IEEE, 2019. [14] B. Zoph and Q. V. Le, Neural Architecture Search with Reinforcement Learning, arxiv, Feb. 2017. [15] G. Seif, Everything you need to know about AutoML and Neural Architecture Search, Towards Data Science, 21-Aug2018. [Online]. Available: https://towardsdatascience.com/ everything-you-need-to-know-about-automl-and-neural-arch-/n/itecture-search- 8db1863682bf2. [Accessed: 06-Apr-2019]. [16] State-of-the-art table for Image Classification on ImageNet, Papers With Code : the latest in machine learning[Online]. Available:https://paperswithcode.com/sota/image-classification-on-imagenet. [Accessed:11-Apr-2019
Copyright
Copyright © 2022 Thota Guna Durga Prashanth, Pendli Rishith Reddy. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET38691
Publish Date : 2021-10-29
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

