Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Review Paper on Door Lock Security Systems
Authors: Vibhor Sharma, Tushar Todia, Utkarsha Vishwakarma
DOI Link: https://doi.org/10.22214/ijraset.2022.43028
Certificate: View Certificate
Abstract
Security is a major issue everywhere today. Everyone wants a home, a factory, a bank, and so on. Housing security is becoming more and more important as access to services increases day by day. Here in this paper, we try to present the research done on various methods of locking doors that have been used in homes, offices, shops, factories etc. This study will also shed light on the pros and cons of various door lock systems. and technologies used in various systems.The study will include the traditional door lock system, RFID-based system, touch-based systems, Bluetooth and GSM based technology and various other technologies used in secure door lock systems. Technological advancement in each passing day can help us to meet various technologies that can be applied to a door lock system. Since safety is a major concern for most people right now, we feel that research conducted on a variety of topics related to the topic can help people choose the best technology for their upcoming projects or make changes to past projects and use a successful department. locking systems for their needs.
Introduction
I. INTRODUCTION
With the growing security-related problems that people face in their workplaces, homes and elsewhere, it has become a major problem for people to use the best door lock system that can provide greater security, pocket-friendly and casual wear and teari.e. door locking depends on the area of ??use as an organization it is best to use RFID technology while at home, key and biometric door lock systems can almost be used by people. Each of these programs has a feature of authentication and authentication that will only provide access to the concerned person. Several revised papers related to the topic and read about the various door lock systems, their features, the technology used, the functionality of the potential systems. help people make the best choice of door lock systems for their utility in their respective area of implementation or project and make possible changes in their existing systems. All the reviewed door lock systems will be categorized based on the technologies that are made use of.
II. TRADITIONAL DOORLOCKSYSTEMS
Traditional door lock systems include a lock and lock system where the door lock automatically opens with the help of a key. The keys can be easily repeated and the doors can be opened by entrants. This approach was as unsafe as modern door locks designed and built that rarely come with access detection, alarming features and photographic features. Door lock systems play a key role in securing workplaces with confidential data or files, stores with large amounts of money or internal storage or even homes with many expensive and necessary items stored indoors.
III. LITERATURERE VIEW
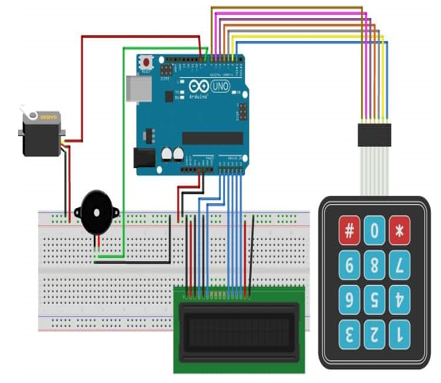
S. Umbarkar et al. [1] use electronic door lock system using Arduino Platform using three different modes namely keypad, Bluetooth and GSM modules. These three modules work with a 4-character password with a keypad matrix. A Bluetooth module was used to establish a connection between a smart phone and a door lock Bluetooth kit and password to unlock the door. The GSM module was used to enter passwords on his cell phone via text message to unlock or unlock the door. It also sent a text message about this module in the event of three failed attempts to enter the password and used the buzzer as an unauthorized login warning. Servo Motor was used to represent the actions of locking and opening the door. The 16X2 LCD display was used to display / interact with the person trying to lock / unlock the door such as “Enter Password”, “Incorrect Password”, in other words, reflects the current state of model usage. Mei-Chuan Tseng et al. [2] suggested how to monitor the door opening function using a single wrist-worn sensor. It can monitor the movement of the upper limb of a person while performing the activities of daily life. It had three subtitles from the complete movement of the door opening which includes holding, rotating and opening the door. the proposed system can detect and identify these signals. The data collection phase includes a 3-axis accelerometer collection and a gyroscope data sensor worn on the wrist.. Sriharsha B S et al. [3] designed and implemented a security system using Arduino, 16x2 LCD, 4x4 keypad matrix and Piezo buzzer that can be used for various applications such as bank locks, BIOS locks on computers, security departments, etc. This program contains a pre-defined password entered by the user (s) each time they want to open a door. The user is instructed to enter a password to unlock the door read by Arduino. The door will open for a period of time allowing user access if the entered password matches the previously defined password. If the entered password is incorrect, a beep sound is generated to alert you to login. The proposed system was developed in an Arduino kit that included ATMega.
Adnan Ibrahin et al. [4] developed a GSM-based door locking system using a PIC field and using a gear engine to display door operations. In the event that a criminal fails to enter the correct password for the third time, the GSM module lock system sends a warning message to the owner to detect interference.. The LCD displays the Lock screen message. To open the door, the user has to press the unlock button where the LCD will display ENTER PASSWORD. To enter a password, the user must press 5 switches (i.e. 5-digit password) S1, S2, S3, S4, S5. Each switch should be pressed sequentially as a digit digit. For example, if the password says “23342” S1 should be pressed 2 times, S2 should be pressed 3 times, S3 should be pressed 3 times, S4 should be pressed 4 times followed by S5 pressed 2 times. Then the UNLOCK button is pressed for confirmation. It is the PIC that signs to open the door if the password entered is correct and the corresponding NATURAL message is displayed on the LCD. The user can only change their login name after opening the door the correct existing password. Initially, when a criminal tries to open a door, the door is locked. If the user enters the wrong password, the LCD displays the PASSWORD ERROR message. In three consecutive failed attempts, the buzzer starts and the GSM module sends a warning message to the owner and neighbors' cell phones. The system is also temporarily blocked.
Steeven Zeiss et al. [5] proposed a door-locking security system with sensory sensors to detect human presence at a distance and no physical contact between the door and the person required to lock / unlock the door. This helps to prevent sewage issues such as infectious diseases from spreading due to fewer people touching the door lizard with their hands as in public toilets. Their project may be used in hospitals instead of foot shifts and in people with physical disabilities. When swiping is performed, only direct and horizontal touch sensors are activated. The four touch sensors are numbered in a way that contrasts with the movement of the clock. Active touch can be detected using a set of digital numbers from 1 to 4 (as there are 4 touch sensors). If the pattern is 12341, it shows a circular touch and the pattern 111444 represents a straight swipe touch. There are various touches to lock, open, open and close the door which can be made in a variety of circular, horizontal or vertical ways.
IlkyuHa [6] has developed a digital door locking system with a number of features such as impact detection and alarm functions to detect when a criminal uses visible force to open a door. It also has a photo transfer function to get pictures of a person if he or she has mistyped the password more than a certain amount and transmits it to the owner's cell phone, incoming log / exit function, a real guest photo recognition system who do not do that. know the password and function to find a valid user when holding a mobile device while opening and closing the door. Visitors can also access the door by entering the code and their photo will be sent to the user. The user when seeing a remote visitor with his device can grant access. The controller can also identify the authorized user and automatically open the door when the user is holding his mobile device. Inbound and outbound logs are stored on the administrator website that can be questioned by the user's mobile device. The door can be opened without the use of physical force and can be accessed even if the user forgets the password. The program included components such as Microcontroller to control the door lock and Bluetooth module used to communicate with mobile devices. To check the presence of a nearby user, an ultrasonic sensor is used. The camera sensor is used for the purpose of taking photographs and the sensor detection sensor to determine the force used by the attacker to open the door to user alert.
Muhammad Sabirin Hadis et al. [7] has developed a secure door lock system that can be unlocked by entering a password on a remote device to control the same.
The app also uses low-power Bluetooth technology found in all gadgets. The program also indirectly promotes the United Nations Convention on the Right of Persons with Disabilities.. This Bluetooth technology acts as a communication agreement between the user and the door lock system.
The system has low power as it consumes less power than Wi-Fi. The program consists of four components: Door Lock, Lock Control System, Server and Device with Bluetooth technology. There is a Bluetooth headset set to ensure security by unlocking the door only if an authorized person has a Bluetooth-enabled device right next to the door. Bluetooth range is approximately 10 m when the Verification range is set to 1 m.
The system also has special features that can be unlocked under certain conditions to increase security and enhance comfort such as the Fingerprint feature, the Get Back feature in case the mobile device is lost...
Yuan-Chih Yu [8] suggested in his paper that the traditional door lock system involves carrying a pile of keys to unlock the door and a keypad-based system cannot be used for long with a virtual keypad such as a printer on a keypad. fades after prolonged use or blurred fingerprints on a touch screen that helps the attacker make a mistake to guess the secret and open the door. Door lock systems also operate on electrical devices which makes them dependent on power and ineffective during power outages. The author came up with a digital door lock system that included a smart card reader and a touch panel. In cases such as power failure, the system was connected to a USB port where the power bank could be connected to power the system.
The keyhole is closed and can only be used if the system is not working during a power outage. A finger touch is made to function as a visible key in the keyhole. The rotation angle and depth of the visible key in the keyhole (key tooth level) are adjusted. Above the keyhole is a codec number showing the rotation angle and the key level of the tooth. Rotation angle and depth can be shared between authorized personnel or family members and in case the connection is forgotten, other members may remind him of the same. The codec number is a combination of the rotation angle and the depth of the key tooth e.g. 180-1 represents 180 ° rotation and 1 key tooth depth.
Meera Mathew and Divya R S [9] developed a door lock system with RFID technology. It also provides authentication from the password.
The system provided better performance and better reliability. They have used many encryption schemes using Java. The two most important features of the program are: the matching key and the Java encryption program. An android app used to store a secure encryption key called Secure Wallet.
The user can change the keys according to their agreement. The user had a login and password to log in to the app and update the private key based on what the OTP would receive by the user and installed while opening the door. to open the door, the user must place his RFID tag next to the reader. The reader retrieves the information associated with the tag and encrypts the information using the private key and encrypted the data to match the stored information. If the information matches the database, OTP is sent to the user via his smart phone.
This OTP is generated by the central server. This OTP is installed by the user on the keypad and is verified. The control signal is made by a system that instructs the corresponding holes to open or lock the door. Date and time of entry and exit are recorded along with user information. The LCD is used to communicate with the controller. ZigBee technology is used for sending and receiving data (OTP). The Block Encryption method is used to encrypt the RFID code with the help of a secret key. Each of the 10 blocks is encrypted in any of the following ways: Blowfish, AES, DES, RC5 respectively. The Symmetric Block cipher method uses the same encryption key.
Somjit Nath et al. [10] designed and developed a door-opening system that can be used in a Laboratory or Library. The system is built using a central server to collect and store all useful information and access to authorized personnel was provided via RFID technology. Wireless Transmitter and receiver were also used in the system. The program is based on Arduino Uno. All users are given a serial number. burned on their RFID tag that the reader can read when the user needs to open the door. All important information about the user is stored on a central server. Once the door is open, it stays in place for a while and the door closes. Manual opening and closing buttons are available on the server terminal that can be used during an emergency or outbreak. An online monitoring system is used to monitor every activity activity. The transmitter and receiver are used for communication between the door and the server.
Conclusion
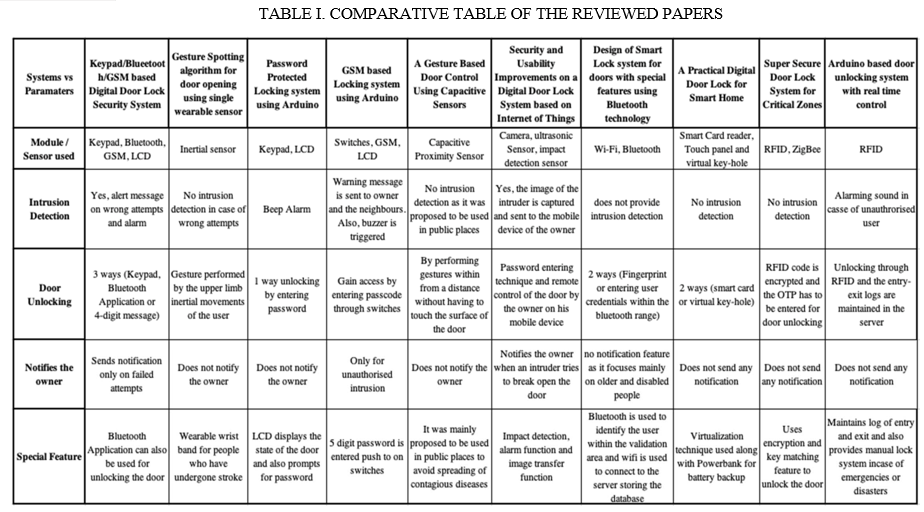
A review paper for door lock systems is presented with a quote from all relevant authors and ideas for their project, research and theory. Comparative analysis made in all papers and presented in review paper. While it is not possible to guarantee complete protection but to identify threats, risks are a few important steps taken to provide as much protection as possible.
References
[1] S. Umbarkar, G. Rajput, S. Halder, P. Harname and S. Mendgudle, “Keypad/ Bluetooth/GSM Based Digital Door Lock Security System,” in ICCASP/ ICMMD-2016, Vol. 137, Pp.749-757. [2] M. Tseng, K. Liu, C. Hsieh, S. J. Hsu and C. Chan, \"Gesture spotting algorithm for door opening using single wearable sensor,\" 2018 IEEE International Conference on Applied System Invention (ICASI), Chiba, 2018, pp.854-856. [3] Sriharsha B S, Zabiullah, Vishnu S B and Sanju V, “Password Protected Locking System Using Arduino,” in BIJIT –2016, January - June, 2016, Vol. 8 No. 1, ISSN 0973–5658. [4] Ibrahim, A. Paravath, P. K. Aswin, S. M. Iqbal and S. U. Abdulla, \"GSM based digital door lock security system,\" 2015 International Conference on Power, Instrumentation, Control and Computing (PICC), Thrissur, 2015, pp. 1-6. [5] Zeiß S., Marinc A., Braun A., Große-Puppendahl T., Beck S. (2014) A Gesture-Based Door Control Using Capacitive Sensors. In: StreitzN.,Markopoulos P. (eds) Distributed, Ambient, and Pervasive Interactions. DAPI 2014. Lecture Notes in Computer Science, vol 8530.Springer,Cham. [6] Ilkyu Ha, “Security and Usability Improvement on a Digital Door Lock System based on Internet of Things,” in Advanced Science and Technology Letters Vol.109 (Security, Reliability and Safety 2015),pp.33-38. [7] M. S. Hadis, E. Palantei, A. A. Ilham and A. Hendra, \"Design of smart lock system for doors with special features using bluetooth technology,\" 2018 International Conference on Information and Communications Technology, (ICOIACT), Yogyakarta, 2018, pp.396-400. [8] Y. Yu, \"A practical digital door lock for smart home,\" 2018 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, 2018, pp.1-2. [9] A. M. Mathew and R. S. Divya, \"Super secure door lock system for critical zones,\" 2017 International Conference on Networks & Advances in Computational Technologies (NetACT), Thiruvanthapuram, 2017, pp. 242-245. [10] S. Nath, P. Banerjee, R. N. Biswas, S. K. Mitra and M. K. Naskar, \"Arduino based door unlocking system with real time control,\" 2016 2nd International Conference on Contemporary Computing and Informatics (IC3I), Noida, 2016, pp.358-362.
Copyright
Copyright © 2022 Vibhor Sharma, Tushar Todia, Utkarsha Vishwakarma. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET43028
Publish Date : 2022-05-21
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

