Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- References
- Copyright
Analysis on Performance Matrices of Routing protocols of Mobile Ad-Hoc Networks
Authors: Seema Gaba
DOI Link: https://doi.org/10.22214/ijraset.2022.44092
Certificate: View Certificate
Abstract
An ad-hoc network is a local area network which has been constructed to connect the one or more devices accordingly. It is a cluster of cellular mobile nodes that are collected with one-another, which form a transitory network, which means to form a temporary structure and there is no need of any permanent support. However, it will attach all nodes with the use of cellular network structure. At compile time, if there is any problem occur that will harm the network, than it can modify the channel from one node to another node. Therefore, because of greatly effective conditions to make networks in very difficult. To avoid these conditions that will harm the network, some protocols are introduced which includes the reactive routing protocols, pro-active routing protocols, cluster- based routing protocol, a hybrid-based routing protocol, Ad- hoc on demand distance routing protocol, optimized link state routing. This review paper gives the performance analysis of routing protocols based on their properties, characteristics, functions, and their shortcomings.
Introduction
I. INTRODUCTION
In the era of wireless technology the MANETs are one of the most efficient technology used for transmission of data. For example:- Wifi-direct, Bluetooth. It helps to connect the devices from the source to the destination without he need of stable infrastructure and any fixed establishment of accessible resources[1]. Several times, when the mobile users need to connect with the wireless structure at that point this help to communicate from one user to the another users with the help of this wireless technology and this can reduce the infrastructure requirement that can also easy to maintain and less security issues and there is no need to create space environment because it is movable connection that can easily handle within several temporal conditions[2].To demonstrate this concept, take an example if the group of users want to communicate with one- another for some organization purpose, if the one of the user is travelling at a point and the other users are at other places then there is no need to create a permanent network[3], at these type of conditions users can dynamically create an temporary connection that will help to communicate with one-another[4].
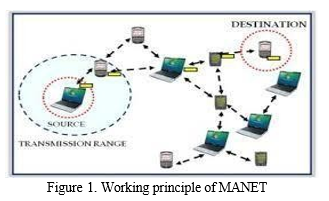
In the above figure 1:- The data packets are sending from the source to the destination with the help of connecting nodes from one device to the another device. Mobile ad-hoc network is used in many government operations also, like military operations, Secret- missions, civil-operations, in remote environment. The main purpose of the establish this type of mobile network in environment is to reduce the bandwidth, energy , and the time constraints [5]. It can also reduce the physical environment structure and limited the security issues that are loss during the sending data from one node to the another node. The mobile adhoc-network uses the multi hop technique rather than static technique that can provide the connectivity between the networks.
II. CLASSIFICATION OF ROUTING PROTOCOLS
A. Pro-active Protocol:-
These protocols can control the routing data of every node present in the network. Every node in the cellular network can protect the routing data of every other node. In the tables all the information is maintained regarding the all nodes that are present in the network[6]. The data is updated according to the topology changes randomly. The main Functionality of pro-active Routing protocol is that they are always feasible without any route analysis.
B. Reactive Protocols:-
These protocols cannot control the routing data of every node present in the network. Every node in the cellular network cannot protect the routing data of every other node[7]. It can do so if there exits the communication between them. These protocols can find the best based on-demand protocol than it can only send the information one node to the another node. However, this protocol can maintain the inter- connection to send and receive the data packets. The packets can transfer the information from source to the destination by making the request to the routes by analysis the best route between them.
C. Hybrid Routing-Protocol:-
The Hybrid Routing Protocols is the combination of both the Pro-active Routing Protocols and the Reactive Routing Protocols. As they contain the functionalities of both the Routing Protocols. The Hybrid Routing Protocol is uniformly send the information and it has the property of Scalability and the data is send is based on the size of the network[8]. However, it can seen that the information is send totally based on the network size.
III. CLUSTERS BASED ROUTING PROTOCOLS
In the Cluster based Routing Protocol, the nodes of the cellular network are connected with few of disassociate and lapped clusters. There is a cluster head that is selected by the every node of the network. For the Routing procedure the cluster head is reason for it. Every node which is used to communicate with one node to the another node is because of the gateway links. The gateway nodes are the connection of the one cluster to the another cluster[9].
A. Routing Process
These protocol are communicate with each other with the help of the cluster adjacency table i.e. (CAT) . The Cluster adjacency table routing process can support their neighbouring clusters to send and receive the data and after that it can store the information in their databases[10]. The Routing process in this type of protocol is based on the two types:-
- One-way Linked Process: This process is also known as bi-directional linked process in which it is bi-directional if atleast there is only linknode is present.
- Two-way linked Process: This process is also known as Uni- directional linked process in which it is unidirectional if more than one linked nodes are present. The Routing process is done with the two forms where the Source send the data and at the destination the Receiver can receives the data.
B. Discovery of the Routes:-
The Discovery of the routes that are best for the routing process is done with the help of the cluster head. The cluster head is send the request to the gateway, and the this gateway node further sends the received information to the another link[10]. This process is further continue in this way until the whole procedure will not finish. This process also can decrease the network congestion between the source address to the destination address.
- Advantages of CBRP: The Cluster based Routing protocols are hugely helpful in reduces the network congestion between the source to the destination and it can also improves the Routing connection between the two networks[11].
- Shortcomings of CBRP: Mostly all the routing protocols have some limitations and disadvantage based on their process. IN CBRP if the cellular network and the clusters are becoming huge then it cannot support the network communication. Moreover, it cannot make the inter- connection between the uni- directional linked process because this type of protocol cannot support the two-way linked process.
IV. ADHOC ON DEMAND DISTANCE VECTOR ROUTINGPROTOCOLS
The AODV network is also known as the Reactive Routing Protocols, as it is always available when the node is needed[12]. The following Figure 3. shows the exchange of the messages from the source node to the destination node.
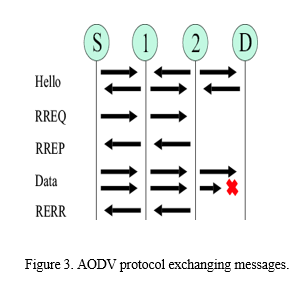
In the above figure 3. The hello message create the link to detect the link between the nodes. If the node has the source data to transmit to the any unauthorized node then it first send request to that node, after that by receiving acknowledgement it will further send the source data[13].
When the receiver does not receives the request than the sender again broadcast the message to the (RERR) after that (RREQ) follows the message Hello than it may follows the request that is given to the receiver to gain the information. If there are more than one RREPs, then the data is chosen only based upon the priority that which request come first. It has been seen that it also works as first-come first- serve technique[14]. The data move from source to the destination is all shown and recorded in the Routing Tables. In this table, if any node is does not work for some time, then that route node is discarded from this routing table and any information regarding for the movement from the Source to the Destination is not shown in the whole procedure[15].
A. Functions of AODV
- The AODV protocol is used for the One-way and the two-way transmission of data.
- The AODV protocol is very powerful and scalable in nature.
B. Shortcomings of AODV
- The AODV protocol is work according to the on-demand route node that iswhy work with it become difficult sometime.
- The AODV protocol needs some mechanisms to broadcasts the messages from the sourceto the destination.
- The maintenance is very low in this protocol.
- The AODV protocol is used for huge complex cellular networks.
- It has less security ascompared to the other protocols.
V. DESTINATION SEQUENCEDISTANCE VECTOR ROUTINGPROTOCOL
As the name suggests, This DSDV routing protocol is used in the ad-hoc number and contains a sequence number. The destination node is only responsible to generate the sequence number[16]. However, this protocol is used for the improvement of the routing loops. In this the information is send from source to the destination by the regular modification in the nodes. The routing information is created by make use of the broadcasting and the two-way linked protocols[17].
The DSDV is contain all the information about the energy consumption and the how much bandwidth is required , Moreover it can even notice a very little modification in the bandwidth and can update all the modified information in the Routing table .This Routing protocol is not used for the large complex networks[18]. As it does not support the huge information that contains the multiple nodes.
A. Characteristics of DSDV:-
- The DSDV reduces the network congestion because the updation is done at every step in this routing protocol[19].
- In the DSDV the path is selected upon the basis of best path among all the other paths.
- The routing protocol is reduced the space problem also.
B. Shortcomings of DSDV
- The DSDV only supports the one- way linked process routing.
- It cannot supports the large complex routings nodes.
- The DSDV can consume huge amount of bandwidth for the complex networks.
VI. DSR PROTOCOL
This type of protocol has consumes less resources for moving the nodes from source to the destination. However, there is no demand for fixed resources and special materials for the transmission of data[20].
A. Advantages of DSR
- In the Dynamic Source Routing Protocol Infrastructure cost is less.
- More than one routes are used in DSR.
B. Disadvantages of DSR:-
- The Dynamic Source Routing Protocol is not scalable in nature.
- The execution process low in this routing protocol.
VII. SUMMARY
In this review paper, the discussion of various protocols has been taken into account and these protocols are compared together on the basis of the performance matrices. In the Pro- active Routing Protocol, the nodes arestriving to connect with all the available networks always. In the Reactive Routing Protocol, based on the congestion and the connection of the network flows it will work. In AODV and DSR protocols, they both is not suitable for larger networks and DSDV routing protocol is give better results to work with larger network. At last, this is summarized that AODV protocol can give comparatively better results in routing environments as it works on demand basis.
References
[1] F. Lee, \"Routing in Mobile Ad hoc Networks\", Mobile Ad- Hoc Networks: Protocol Design, 2011. [2] R. Ahuja, A. B. Ahuja and P. Ahuja, \"Performance evaluation and comparison of AODV and DSR routing protocols in MANETs under wormhole attack\", IEEE Second International Conference on Image Information Processing (ICIIP-2013), 2013. [3] S. Ali and P. Nand, \"Comparative performance analysis of AODV and DSR routing protocols under wormhole attack in mobile ad hoc network on different nodes speeds\", International Conference on Computing Communication and Automation (ICCCA), 2016. [4] T. Abdel-Halim, H. M. A. Fahmy and A. M. Bahaa-Eldin, \"Agent-based trusted on-demand routing protocol for mobile ad- hoc networks\", Wireless Networks, vol. 21, no. 2, pp. 467-483, Mar. 2014. [5] Woungang, S. K. Dhurandher, M. S. Obaidat, H.-C. Chao and C. Liu, \"Trust-enhanced message security protocol for mobile ad hoc networks\", IEEE International Conference on Communications (ICC), 2012. [6] H. Xia, Z. Jia, X. Li, L. Ju and E. H.-M. Sha, \"Trust prediction and trust-based source routing in mobile ad hoc networks\", Ad Hoc Networks, vol. 11, no. 7, pp. 2096-2114, 2013. [7] Kelvin Fall, \"The ns manual (formerly ns Notes & Documentation)\", US Berkerley LBL USC/ISI and Xerox PARC, 2010. [8] A.D. Robins, GAWK:an effective AWK programming, April 2010. [9] A Tuteja, A Gujral and A Thalia, \"Comparative Performance Analysis of DSDV AODV and DSR Routing Protocols in MANET using NS2\", IEEE Comp. Society, pp. 330-333, 2010. [10] R. Agrawal, R. Tripathi and S. Tiwari, \"Performance Evaluation and Comparison of AODV and DSR Under Adversarial Environment\", International Conference on Computational Intelligence and Communication Networks, 2011. [11] M. Arora, R. K. Challa and D. Bansal, \"Performance Evaluation of Routing Protocols Based on Wormhole Attack in Wireless Mesh Networks\", Second International Conference on Computer and Network Technology, 2010. [12] P. Gera, K. Garg and M. Misra, \"Trust Based Multi Path DSR Protocol\", International Conference on Availability Reliability and Security, 2010. [13] X. Yang, C. Hui and L. Haizhon Frank, Handbook On Sensor Networks, World Scientific, 2010. [14] M. A. Azer, S. M. El-Kassas and M. S. El-Soudani, \"Immuning Routing Protocols from the Wormhole Attack in Wireless Ad Hoc Networks\", Fourth International Conference on Systems and Networks Communications, 2009. [15] K. Wang, M. Wu and S. Shen, \"A Trust Evaluation Method for Node Cooperation in Mobile Ad Hoc Networks\", Fifth International Conference on Information Technology: New Generations, 2008. [16] S Sarkar, T.G. Basavaraju and C. Puttamadappa, Ad Hoc Mobile Wireless Networks: Principles protocols and applications, Auerbach Publications, 2008. [17] Tonguz and G. Ferrari, Adhoc Wireless Networks-A Communication -Theoritic Perspective, Wiley and Sons, 2009. [18] A Boukhalkhal, M.B. Yagoubi, D Djoudi, Y Ouinten and M Benmohammed, \"Simulation of Mobile Adhoc Routing Strategies\", IEEE, pp. 128-132, 2008. [19] K. Wang, M. Wu and S. Shen, \"A Trust Evaluation Method for Node Cooperation in Mobile Ad Hoc Networks\", Fifth International Conference on Information Technology: New Generations, 2008. [20] [20]A. Pirzada, A. Datta and C. Mcdonald, \"Propagating trust in ad-hoc networks for reliable routing\", International Workshop on Wireless Ad-Hoc Networks, 2004.
Copyright
Copyright © 2022 Seema Gaba. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET44092
Publish Date : 2022-06-11
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

