Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- References
- Copyright
Smart Entry System
Authors: Ch. Amulya, K Yashwanth, P. Manishanker, Dr. S. Krishna, Dr. Syed Jahangir Badashah
DOI Link: https://doi.org/10.22214/ijraset.2023.48740
Certificate: View Certificate
Abstract
Security and safety are growing in popularity as time goes on, and they are being enhanced and utilised to make our lives easier. Technology has now permeated every aspect of human life, so protecting the security of one\'s home, place of business, or organisation cannot be overlooked. Developing a smart receptionist with a smart lock system was mostly done for security reasons. When the front entrance of the house, business, or organisation is closed, this clever security system is employed to detect a visitor. The Raspberry Pi and Telegram bot are used in this setup to issue commands that operate the door lock. In this system, anytime a person approaches the door, the PIR sensor detects their presence, activates the camera, records a 5-second video of the individual, and sends a notification to the user via Telegram. The system will open the door if the owner permits entry, and the door will remain locked if the owner forbids entry using commands sent through the Telegram bot.
Introduction
I. INTRODUCTION
The "Smart Entry System" is a system that was created to raise the security level. The Raspberry Pi 3 can open the door thanks to the system's design. And only allow authorised people access. Access control for the door and a security system based on a face recognition pattern are provided by this efficient system. The main goal of the paper is to identify the visitor at the front entrance and let them into the office if the known person is in front of the door and the worried person is in the middle of a meeting. The entire operation of the front door is managed by a Raspberry Pi 3. Quad-core, 1.2GHz Raspberry Pi3 model B processor with 4GB of RAM. It is a scaled-down variation of the active computer. There are numerous interacting units. Using a Raspberry Pi 3 and the internet, a video and photo of the visitor are taken with the Pi Cam and delivered to the registered Telegram account.Normal locks were replaced with password-based door locks, which are widely used nowadays, in order to ensure superior security. The guest must input the password in the password-based door lock system in order to unlock the door. It offers better protection than conventional locks since there is a greater danger of losing the keys to conventional locks, which can be prevented by employing password-based door locks. Anyone who knows the password can enter the house without having to wait for the person carrying the keys with him.
When someone approaches the door, the PIR sensor in this system detects their presence, notifies the user by Telegram, turns on the camera, records a 5-second video of the person, and then turns on the smart lock. By giving commands to a telegram bot.door via a mobile device, the system will unlock the door if the owner approves admission and keep it locked if the owner refuses entry. This system consists of a Raspberry Pi model B3, a PIR sensor, a camera module, and an Android software called Telegram for receiving notifications. Any approaching people are detected by the technology at the entrance.
The user can use a mobile phone to unlock the door as soon as they receive a notice. The user will open the door and offer authentication to enter the house if the person is recognised. In the modern world, security is crucial since, as the adage goes, "the more technology, the higher the security." In order to protect the Raspberry Pi from hackers, this document offers security. Asymmetric cryptography and SSH keys are used in this project to secure the network. Users can secure their Raspberry Pi by using the FAIL2BAN technique. Electronic door lock systems are now among the most frequently installed security systems for homes and businesses in recent years. Such systems' defining characteristic is the dependability with which authorised individuals can gain access to the doors via a secure system with a user-friendly interface. The Near Field Communication (NFC) door lock system is a new mechanism that has emerged. Based on pattern recognition technology, this method examines a person's face to ascertain their personality . For instance, such analysis can be performed on facial image or video streams. The study also considers the size and posture of the face's physical features. This study's objective is to demonstrate a state-of-the-art Bluetooth-based home security system. The main goal is to build a prototype that can mimic wireless operations like controlling and monitoring a digital door lock.
Our daily lives' safety is of the utmost importance. Everybody requires a sense of security. As part of our security strategy, we have a door access control system.
The security of conventional locks has declined, making it feasible for anyone to get entry by picking them. It is necessary to have a system that is accessible twenty-four hours a day, seven days a week. Only authorised individuals are permitted entry into restricted areas thanks to a password-based door lock system. Arduino is in charge of the entire system. A keypad can be used to enter the password. The door will open if the password matches the one entered into Arduino. This password-based bolt system gives customers access to a more convenient and safe locking-opening method. Electronic door locks will soon replace mechanical door locks thanks to the security door lock automation system. There have been presented a number of remote systems for business and academia. These systems were created to offer remote monitoring and control capabilities. For instance, a Zigbee-based system has been suggested. One of the many components that make up this system, the human detection module (HDM), tries to recognise the user at the entrance. This can be done using the camera module that is handling the video or photo feed.
II. OBJECTIVE
The primary goal of the paper is to identify the visitor at the front entrance and let them enter the office if the person in question is in the middle of a meeting and if the familiar person is in front of the door.
III. LITERATURE REVIEW
In 2020, Deepthi Murthy put up a study on the Raspberry Pi, which indicated that a thorough examination of the little PC-sized Raspberry Pi was nearing completion.
Being a small form factor device, the Raspberry Pi offers endless prospective consequences for undertaking improvement in the area of implanted frameworks and daily undertaking unconventional initiatives. Software engineering students can utilise the Raspberry Pi to practise programming, learn Linux administration, and perform server administration tasks on email, cloud, and other web servers. Different devices, like as sensors, LEDs, and so on, can be interfaced with installed frameworks using GPIO. This paper will astound everyone, inspiring them to use this technology and look into endless possibilities. A small, surprisingly affordable, low-structure factor PC, the Raspberry Pi is considered as being highly effective. The Raspberry Pi can be used by different SMEs to do small and medium-sized jobs, such as acting as a web server, database server, and video server. Thus, it is possible to save a lot of money by not recruiting more staff. A single platform for gaining considerable programming experience is the Raspberry Pi. Numerous programming languages are supported by Pi, and users can choose a specific compiler to guarantee that their code is run correctly. Python, Pi's primary programming language, is less complex and simpler to comprehend. Benefits include less lines, improved code, better board work. As a result, the Raspberry Pi may be easily removed to access a huge variety of apps in that Linux operating framework. The Raspberry Pi is compatible with extra hardware, including a camera, component moduler kit, gertboard, and hatboard, which can be connected to a wide range of external devices, including buttons, LEDs, and clients that can run a variety of software on the Pi. Compared to independent enterprises, the product offers a more morally sound choice while also saving energy.
This tiny charge card, which is reusable, provides a discount on cooling goods. It cannot function as an undeniable PC because the Ethernet Port and Processing CPU aren't as swift to measure doing many operations and recording cycles. With a fully functional Windows operating system, this is impossible. The product offers a wide range of possibilities for office space, is only accessible to SME's, and is not particularly valuable[3]. Dr. Asif Ali and Salman Shaikh proposed a study on automatic face recognition in 2020. This paper defines visual deficiency as the inability to comprehend visual information due to physiological or neurological reasons. A clear, understandable, and tightly focused guidance framework has been developed and put into action in this endeavour to promote the mobility of visually impaired and outwardly inhibited people. The project shows wearable technology with headphones. In order to enable physically disabled persons to move about independently, it has been coupled with raspberry-pitto to demonstrate features including obstacle finding, facial recognition, picture to discourse transformation, and money locating. A graphic with a Haarand ANN computation has been utilised to illustrate the capabilities in this task. This methodology thoroughly describes a face acknowledgment-based automatic involvement system. The offered solution provides a way to distinguish between people based on their info picture, which was acquired from a picture of an envelope. With this method, we can comprehend the essentials of an understudy and speed up their participation naturally and without the help of a human. The model's usability can be boosted if subtleties are stored on the cloud. The registers that comprise the customary participation framework differ from each other by The structure for consumer engagement includes registers that are set aside by teachers, which invites human error and requires a lot of upkeep. In this paradigm, time usage is a key area of concern. We have thought about changing it using modern digital tools like FACE RECOGNITION that are readily available. Greater accuracy will be achieved through our efforts, with minimum physical labour. The assignment has been changed to address the issues with the existing framework.
The assignment has been changed to address the issues with the existing framework. It is our responsibility to acknowledge faces before indicating engagement. When a particular student's essence matches one of the countenances contained in a photograph, participation is checked; if not, the face is ignored and participation is not stamped. The database of the class's relatively high number of students is kept in an envelope. Our task makes use of face acknowledgment (Machine Learning) technologies. This use a Histogram of Oriented Gradient for face recognition and an SVM Classifier for name recognition.
A. Existing Technology
Normal locks were replaced with password-based door locks, which are widely used nowadays, in order to ensure superior security. The guest must input the password in the password-based door lock system in order to unlock the door. When compared to conventional locks, it offers superior security because there is a greater risk of key loss with conventional locks, which may be reduced by employing password-based door locks. Anyone with the password can enter the house without having to wait for the holder of the keys. However, the main drawback of password-based door lock systems is that if you forget your password, you have no chance of unlocking the door, which could lead you into problems.
B. Proposed Technology
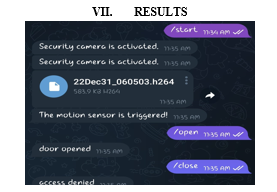
In comparison to conventional locks and door locks that rely on passwords, the proposed system, called a "smart door receptionist with smart lock system," offers great security. The "Smart Receptionist with Smart Lock System" is a system that was created to raise the security level. The Raspberry Pi 3 can open the door thanks to the system's design. And only allow authorised people access. This efficient system uses a face recognition pattern to manage access to the door and the security system. The Raspberry Pi and the user are connected using Telegram. The door opens or closes in accordance with orders you send to the Telegram bot, such as "/open," "/closedoor," and "/close."
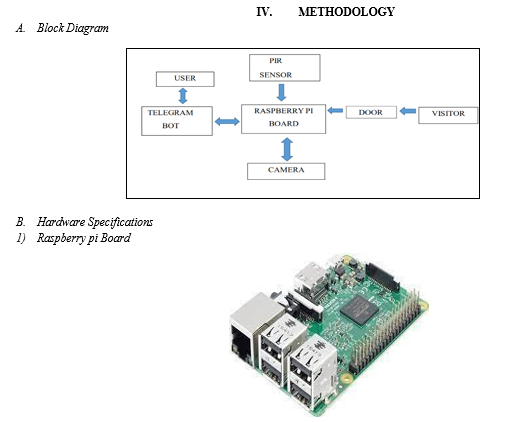
V. WORKING
- Step 1: The PIR sensor detects motion and turns on the camera module whenever someone approaches the entrance.
- Step 2: The visitor's video is recorded by the Pi Cam and sent to the owner's telegraph.
- Step 3: Depending on the owner's choice, the raspberry pi is given the appropriate command in a telegram (such as "/open," "/close," or "/access refused").
- Step 4: The door opens or closes in response to the command that the raspberry pi receives.
- Step 5: If we need to let the guest into our office, we must issue the command "/open" to unlock the servo-driven door lock. To open the door, the servo motor revolves anticlockwise. After the visitor enters the house or workplace, the door automatically closes after 10 seconds by rotating the servo motor anticlockwise.
- Step 6: The door stays closed if the command "/access denied" is provided.
VI. CONNECTIONS
- The raspberry pi's GPIO pins are connected to the PIR sensor's outgoing pin.
- The raspberry pi's GPIO2 pin is connected to the signal pin of the servo motor.
- The Raspberry Pi's power pins are linked to the servo and PIR's VCC and GND pins.
References
[1] https://gpiozero.readthedocs.io/en/stable/api_output.html [2] https://projects.raspberrypi.org/en/projects/parent-detector/1 [3] https://www.engineersgarage.com/raspberry-pi-based-smart-home- security-system [4] https://docs.microsoft.com/en-us/azure/bot-service/bot-service-channel-connect-telegram?view=azure-bot-service-4.0 [5] https://roboticsbackend.com/raspberry-pi-camera-picamera-python- library
Copyright
Copyright © 2023 Ch. Amulya, K Yashwanth, P. Manishanker, Dr. S. Krishna, Dr. Syed Jahangir Badashah. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET48740
Publish Date : 2023-01-19
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

