Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
A Study of Cryptographic Algorithms
Authors: Dr. Manjot Kaur Bhatia, Rajshekhar Singh Rajpurohit, Gulafshan , Benjamin Joseph
DOI Link: https://doi.org/10.22214/ijraset.2022.47848
Certificate: View Certificate
Abstract
This paper explores many important Symmetric and Asymmetric Cryptography algorithms and their essence in network security. As the use of the internet has grown, so have attacks on the communication channels. These attacks can be used by third parties to obtain sensitive data about your organization and its activities. This data can be used to compromise an organization’s operations or blackmail the organisation to pay for the data. To avoid these situations, such algorithms are adapted to protect communications. These algorithms encrypt data that is nearly impossible for unauthorized persons to read, making it unusable for attackers. These algorithms therefore play an important role in the security of communications. This paper states a study of symmetric and asymmetric algorithms in terms of optimal resource allocation, potential attacks which can be used to exploit these algorithms, time consumption, power consumption, overall structure and some other basis Along with explanation of some of the security attacks.
Introduction
I. INTRODUCTION TO CRYPTOGRAPHY
In today's world, the most precious element is data. Data can tell us a lot about an organization’s strengths and weaknesses. The one who can possess and process this data with statistical and/or logical techniques can ultimately affect activities of organization actively or passively. Hence arises the question, shouldn’t there be some security features for this vital element?
This is where cryptography comes into play. Cryptography consists of securing information and communication with techniques derived from mathematical concepts and rule- based calculations called algorithms. The ideal cryptography technique would let decipher the data by only those for whom the information is intended.[1][2][3][4]
A. Cryptography Goals
The ultimate goal of cryptography is to secure information that can't be deciphered by third party personnel who are not supposed to receive the message. This goal may be softened into several sub-goals.[2] These are listed below
- Confidentiality
This term covers 2 connected concepts:
a. Data Confidentiality: This concept assures that personal data is made available only to the authorized personnel.
b. Privacy: This concept makes sure that the information collected is available only to the intended receivers and not shared further.
2. Integrity
This term covers 2 connected concepts:
a. Information Integrity: The information is modified solely in a specified and approved way.
b. System Integrity: Ensures that a device/software performs its operations in a robust way, free from forced or accidental unauthorized manipulation of the system.
3. Availability: Ensures that systems work whenever available and repair is made available to the authorized users. The above listed objectives are known as the CIA triad. The 3 ideas embody the fundamental security objectives for informational and computational services. As an example, the NIST standard FIPS 199 (Federal Information Processing Standard Publication 199, Standards for Security Categorization of Federal Information and Information Systems) lists confidentiality, integrity, and availability because of the 3 security objectives for information and for information systems. FIPS 199 provides a helpful characterization of those 3 objectives in terms of needs and also the definition of a loss of security in every category: [3][1]
a. Confidentiality: Protective approved restrictions on information access and revelation, as well as suggests that for shielding personal privacy and proprietary information.
b. Integrity: Guarding against improper information, modification or destruction, as well as making certain information non-repudiational and believable. Unauthorized manipulation of information is loss of integrity.
c. Availability: This is about ensuring the timely and reliable access to and use of data. A loss of availability is the disruption of access to use of data or associated systems.
Though the utilization of the central intelligence agency triad to outline security objectives is well established, some within the security field feels that extra unit required to give a whole image. Two of the foremost unremarkably mentioned area units are as follows: [1][3][4]
4. Authenticity: the property of being real and having the ability to be verified and trusted; confidence within the validity of a transmission, a message, or message conceiver. This implies that users are who they say they are and the information arrived at the system came from a trusted source.
5. Accountability: The principle of accountability refers to an entity being answerable to authority for any loss or misuse of that information. Since ideal secure systems are not yet an achievable goal, we must be able to trace a security breach to a responsible party. Systems must keep records of their activities to help forensic analysts trace back in case of security breach or transaction disputes.
B. How does Cryptography Work?
Let’s say there are two people, Alice and Bob who want to communicate and share information about the future ambitions of their company. They are using some regular insecure channel to communicate. Because this information is crucial to the company’s future operations, it must be protected. If Oscar, who is not supposed to receive this vital information, obtains it through eavesdropping tactics and wishes to thwart their objectives, he can easily do so by distorting the data by stealing their intellectual property and selling it to someone else.[2][4]
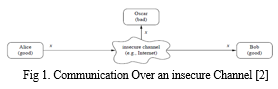
Cryptography can help to mitigate such hazards. The symmetric cipher (which has been modernized on a massive scale) is a rudimentary type of encryption approach in which one secret key is shared by a secured channel between Alice and Bob before communication begins. This secure route could be a face-to-face meeting or another way. This key will be used by the sender to encrypt the message and by the recipient to decrypt the data. Plain text refers to unencrypted data, while cypher text refers to encrypted data. Even if Oscar listens in on their chat, he won't be able to decipher the message because it will be encrypted using a secure key that only Alice and Bob have. As a result, all critical data will be protected, and even if someone gains access to critical messages, they will be unable to decrypt them without the private key, which will be held only by those who are supposed to receive them.[2][3]
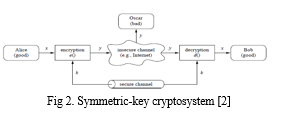
- x is called plain text
- y is called ciphertext
- k is called private/secret key
- the set of all possible keys are called key space
The vital thing to remember is that the private key must be kept secret, but the algorithm can be made public. It makes sense to keep the method confidential in order to prevent third parties from decrypting the communication, but keeping the algorithm private also indicates that it has not been tested. Making an encryption method's algorithm public and allowing other cryptographers to study it is the best way to determine whether it is strong enough or can be decoded by determined attacker. The private key is the only thing that must be kept hidden.
C. Remark
Here, the only thing under consideration is confidentiality, that is hiding the contextual meaning of the message from people with unauthorized access. Cryptography can also be used to avoid third party from making unnoticed changes in the data (message integrity) or assure the data is really coming from an authenticated user. (message authenticity)
II. TYPES OF CRYPTOGRAPHY
There are mainly two types of cryptography:-
- Symmetric cipher : DES, AES
- Asymmetric cipher : RSA, ECC
A. Symmetric Cipher
The symmetric cipher makes use of only one private key to encrypt the data and this same key is used to decrypt the data. If Alice wants to send a message to Bob, she can use the K1 private key and this K1 private key will be used on Bob’s side as well to decrypt that message. [2][3]
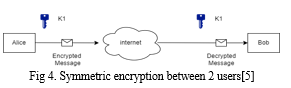
Now, if a third party, say Charlie, wants to send a message to Alice, she should use a different key than K1 because K1 is already in use to establish secure communication between Alice and Bob, and both of them have this key, so even if the message is only intended for Alice, Bob can decrypt it using his key. To circumvent this, every two people on the network must communicate using a unique key.
Same thing goes for establishing a connection between Charlie and bob.
Drawbacks
- The primary drawback of symmetric encryption is the increasing amount of unique keys required to interact with various users. If one person needs to communicate with 100 others, they must manage and keep 100 keys safe, which would make encryption a lot more hectic than it needs to be.
- Another critical disadvantage of using symmetric encryption is that the private key must be shared with both parties in order to have secured communication. Since there can’t be any electronic communication which can guarantee 100% security.
B. Asymmetric Cipher
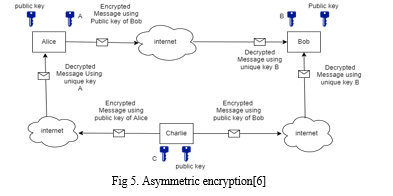
To overcome the drawback of symmetric cipher, asymmetric cipher was introduced by Whitfield Diffie and Martin Hellman in 1977. Also known as public-key cryptography.
Instead of having only one unique key, this has two. As in symmetric cypher, one is the private key. The other is the public key, which is held by all members in a network. If the data is encrypted with a public key, the data will be decrypted with a relative private key. When a private key is used to encrypt data, the associated public key is used to decrypt it. Thus, the sender is always verified.
The catch here is that the public key would encrypt the message on the basis of the recipient’s private key and vice versa. If Alice wants to send a message to Bob using asymmetric encryption, she must encrypt the message using Bob's public key; however, this message can only be decoded using Bob's private key, which is only in Bob's possession. As a result, each connection does not require a unique key, but rather a single unique key for anyone on the network and a public key held by everyone. Same would happen in case of Charlie sending message to Alice or Bob.[2][3]
- Advantages over Symmetric Encryption
- Key distribution problem is solved.
- Since there’s no need to transmit secret keys, it’s more secure than symmetric encryption.
- The use of digital signatures is allowed, therefore the recipient can verify the source of the message. That is, message authenticity is achieved.
- It allows non-repudiation so that the sender can’t deny sending a message.
2. Disadvantages
- It is a comparatively slow process, that’s why it is not appropriate to use it for decrypting bulk messages.
- If a person lost their private key, they cannot decrypt their messages.
- If an unauthorized actor identifies someone’s private key, they can interpret their messages.
III. WORKING OF ALGORITHMS
A. Data Encryption Standard (DES)
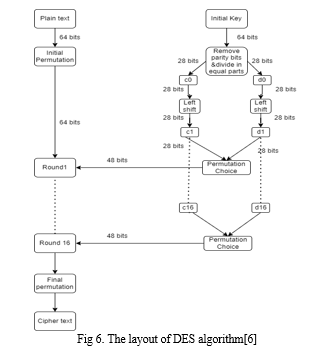
DES stands for Data Encryption Standard. It is an algorithm of symmetric cryptography. DES is a block cipher and encrypts data in blocks of size 64 bit. There are a few steps to understand how DES works. [5][6]
- Operations on Message
a. Initial permutation: In this the 64 bit block data is handed over to an initial permutation function.
b. In the second step, 64 bit data is again permuted into two blocks of 32 bit data. These blocks are called left plain text (LPT) and right plain text (RPT).
c. These both blocks are operated in a total of 16 rounds with a private key.
d. Final permutation is performed. This permutation is also called inverse initial permutation.
2. Operations on Key
a. Initially the key size is 64 bit.
b. 8 Parity bits (8, 16, 24, 32, 40, 48, 56, 64) are removed and the key size becomes 56 bits.
c. These 56 bits will be divided into two equal sized blocks of 28 bits each.
d. Left circular shift will be performed on the basis of the round number.
- If the round number is one of these (1, 2, 9, 16) there will be one bit circular shift.
- Else there will be a two bit circular shift.
e. A copy of both blocks of sub-keys will be used in the next round. For the current round the both sub-keys will be combined. This will give 56 bits sized sub-key for the round.
f. Now a permutation function will choose 48 bits from 56 bits and arrange them. It is called “Compression-Permutation operation”.
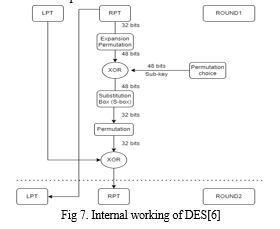
3. Core operations in Each Round
a. Left plain text (LPT) block and one copy of right plain text (RPT) will be passed at the end..
b. Right plain text block will have bits expanded by expansion permutation. (from 32 bits to 48 bits)
c. This 48 bit block will perform XOR operation with the sub-key.
d. This 48 bit resultant block will be passed with substitution blocks (s-block) and ultimately turned into 32 bits block.
e. This 32 bit block will be again permuted.
f. This processed RPT will perform XOR with LPT.
g. The copy of initial RPT will work as LPT and processed RPT will be RPT for the next round.
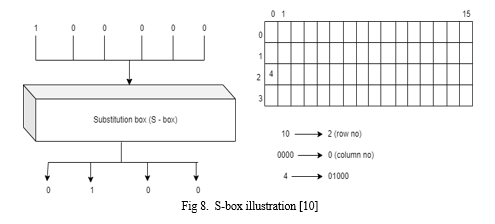
4. Substitution box Operations: [10] [11]
a. 8 s-boxes work simultaneously to process 48 bits data blocks.
b. 6 bits are passed to each s-box.
c. First and last bit are combined. The decimal value of the obtained binary code will represent the number of rows. And the rest of the bits are combined whose decimal value will represent the number of columns.
d. Whatever data on that specific position in the initial 64 bit data table will be converted to 4 bits binary form.
e. Bits of this binary number will be output of s-box.
f. Every s-box will convert 6 bits into 4 bits. Hence 48 bits into 32 bits.
DES Limitations
- Key Size: The sub-key is only of size 56 which results in 256 combinations, so even the brute-force attack is very efficient against DES encryption. Since modern computers have more computational power and they have the ASIC (application specific integrated circuit), it makes such computations much faster. [1][2] [8]
- Weak Keys: 4 out of 256 combinations only contain 0’s or 1’s or half 0’s and half 1’s. The disadvantage of using weak keys is that, if we use weak keys in 2 continuous rounds, we get the same plain text we were processing. [9]
- Semi-weak Keys: 6 out of these sub-key combinations will generate only 2 types of semi keys in 16 rounds. So each of them is repeated 8 times. So it will be easier for a cryptanalyst to decrypt the data. [2] [8]
- Possible Weak Keys: 48 key combinations are possible weak keys, which only generate 4 types of keys in 16 rounds. So each of them is repeated 4 times instead of having 16 distinct sub-keys.[2]
- Key Clustering: If one sub-key k1 encrypts a message and some random key, k2 encrypts that message but it is the same as the initial message. This is called key clustering, which makes it weak algorithm to encrypt.[2]
C. Advanced Encryption Standards (AES)
AES stands for advanced encryption standards.
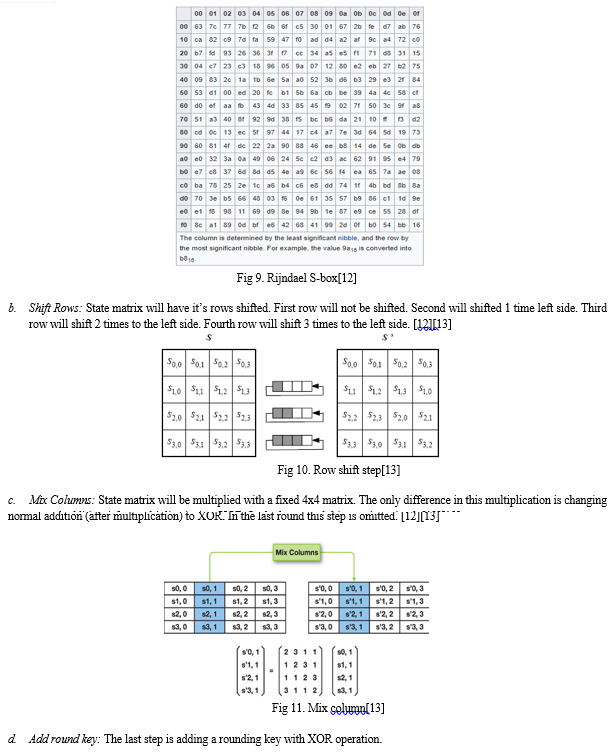
- Operation on Message: [9][11][12]
a. Whole message is divided into blocks of 128 bits.
b. This 128 bits block would be in the form of a 4x4 matrix whose one cell would have size of 1byte (8bits).
c. The block would be performing XOR operation with k0 sub-key and generate a state matrix. (intermediate form)
2. AES Transformation Function
a. Sub-Bytes: State matrix will pass through the substitution box (Rijndael S-box). This s-box has a 16x16 matrix of distinct hexadecimal values. Every cell of the data block will be replaced by these values. Every cell of data will have a hexadecimal value whose left digit will be denoting row no. and right digit will denote column number. Now the hexadecimal value at this specific position in s-box will replace value inside that state matrix.[12][13]
Conclusion
Symmetric encryption utilizes a unique key that requires it to be shared to the people who need to obtain the data, whereas asymmetric encryption uses a pair of public key and a private key to encrypt and decrypt messages when exchanging information. Some popular algorithms for symmetric encryption are RC4, AES, DES, 3DES, and QUAD. RSA, Diffie-Hellman, ECC are some of the Asymmetric Encryption. Implementation of ECC is toughest among others because of the complicated mathematical aspect of the algorithm. Some attacks against these algorithms are Brute-force attacks, Cipher-only attacks, Known-plaintext attack, Man in the middle, side channel etc. Key-size of an algorithm affects memory usage and power consumption along with the speed of encryption and decryption. AES is the most robust symmetric encryption algorithm, whereas ECC turns out to be a better Asymmetric algorithm than RSA. The longer key length of RSA causes RSA to be the least secure algorithm because of potential side channel attacks. DES is the only algorithm among those discussed, to be vulnerable to brute force attack. Other algorithms’ longer key sizes makes it impossible to be cracked with a brute force attack.
References
[1] Delfs, H., Knebl, H., & Knebl, H. (2002). Introduction to cryptography (Vol. 2). Heidelberg: Springer. [2] Stallings, W. (2006). Cryptography and network security, 4/E. Pearson Education India. [3] Mollin, R. A. (2006). An introduction to cryptography. Chapman and Hall/CRC. [4] Bellare, M., & Rogaway, P. (2005). Introduction to modern cryptography. Ucsd Cse, 207, 207 [5] Mahajan, P., & Sachdeva, A. (2013). A exploring of AES, DES and RSA encryption algorithms for security. Global Journal of Computer Science and Technology. [6] Singh, G. (2013). A study of encryption algorithms (RSA, DES, 3DES and AES) for information security. International Journal of Computer Applications, 67(19) [7] Patil, P., Narayankar, P., Narayan, D. G., & Meena, S. M. (2016). A comprehensive evaluation of cryptographic algorithms: DES, 3DES, AES, RSA and Blowfish. Procedia Computer Science, 78, 617-624 [8] Smid, M. E., & Branstad, D. K. (1988). Data encryption standard: past and future. Proceedings of the IEEE, 76(5), 550-559. [9] Penchalaiah, N., & Seshadri, R. (2010). Effective Comparison and evaluation of DES and Rijndael Algorithm (AES). International journal of computer science and engineering, 2(05), 1641-1645. [10] Courtois, N. (2005). The best differential characteristics and subtleties of the Biham-Shamir attacks on DES. Cryptology ePrint Archive. [11] Akkar, M. L., & Giraud, C. (2001, May). An implementation of DES and AES, secure against some attacks. In International Workshop on Cryptographic Hardware and Embedded Systems (pp. 309-318). Springer, Berlin, Heidelberg. [12] Bonneau, J., & Mironov, I. (2006, October). Cache-collision timing attacks against AES. In International Workshop on Cryptographic Hardware and Embedded Systems (pp. 201-215). Springer, Berlin, Heidelberg. [13] Selmane, N., Guilley, S., & Danger, J. L. (2008, May). Practical setup time violation attacks on AES. In 2008 Seventh European Dependable Computing Conference (pp. 91-96). IEEE. [14] Zhou, X., & Tang, X. (2011, August). Research and implementation of RSA algorithms for encryption and decryption. In Proceedings of 2011 6th international forum on strategic technology (Vol. 2, pp. 1118-1121). IEEE. [15] Rahman, M. M., Saha, T. K., & Bhuiyan, M. A. A. (2012). Implementation of RSA algorithm for speech data encryption and decryption. IJCSNS International Journal of Computer Science and Network Security, 12(3), 74-82. [16] Boneh, D. (1999). A 20-years attack on the RSA cryptosystem. Notices of the AMS, 46(2), 203-213. [17] Nara, R., Satoh, K., Yanagisawa, M., Ohtsuki, T., & Togawa, N. (2010). Scan-based side-channel attack on his RSA cryptosystem using scan signatures. IEICE transactions on fundamentals of electronics, communications and computer sciences, 93(12), 2481-2489. [18] Nitaj, A., Ariffin, M. R. K., Nassr, D. I., & Bahig, H. M. (2014, May). New attacks on the RSA cryptosystem. In International conference on cryptology in Africa (pp. 178-198). Springer, Cham [19] Singh, L. D., & Singh, K. M. (2015). An implementation of text encryption using elliptic curve cryptography. Procedia Computer Science, 54, 73-82 [20] Alam, M., Jahan, I., Rosario, L. J., & Jerin, I. (2016). A Comparative Study of RSA and ECC and Implementation of ECC on Embedded Systems. algorithms, 1, 2. [21] Amounas, F., & El Kinani, E. H. (2012). ECC encryption and decryption by data sequence. Applied Mathematical Sciences, 6(101), 5039-5047. [22] Padmavathi, B., & Kumari, S. R. (2013). A survey on performance analysis of DES, AES and RSA algorithms along with LSB substitution. IJSR, India, 2, 2319-7064. [23] Farah, S., Javed, Y., Shamim, A., & Nawaz, T. (2012, December). An experimental study on performance evaluation of asymmetric encryption algorithms. In Recent Advances in Information Science, Proceeding of the 3rd European Conf. of Computer Science,(EECS-12) (pp. 121-124).
Copyright
Copyright © 2022 Dr. Manjot Kaur Bhatia, Rajshekhar Singh Rajpurohit, Gulafshan , Benjamin Joseph. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET47848
Publish Date : 2022-12-03
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

