Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
The Various Types of Network Topologies Systems and their Efficiency Reliabilities
Authors: Muhammad Arif Bin Jalil
DOI Link: https://doi.org/10.22214/ijraset.2023.55654
Certificate: View Certificate
Abstract
Topology describes the procedure of putting items in a particular order, arrangement, or connection. So, the process of organising, organising, or connecting various devices in a network is referred to as network topology. Network topology refers to the various ways that devices can be connected to one another. Depending on how devices are connected to one another and how data moves between them, these network topologies have been categorised into several categories. Some of the topologies used in different industries for system layout include star, ring, hybrid, mesh, tree, and bus. This study has examined the advantages and disadvantages of different topologies based on connections and data flow. In this article, the significance of network topology will be discussed. In this article, the significance of network topology is covered. The increasing need for these topologies in several start-ups and major enterprises is covered in this article.It demonstrates how topologies have a bright future because every organisation must establish a network that must be carefully organised, leading to an increase in the use of network topologies.
Introduction
I. INTRODUCTION
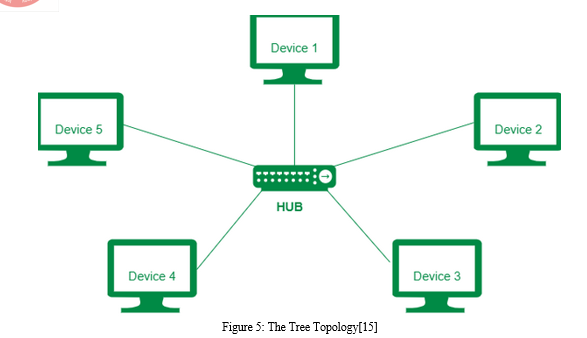
The process of setting up different components (such links and nodes) of a network is known as networking topology. It can be thought of as a geometric illustration of the interconnection and communication between many systems[1]. There are several reasons why the network layout is important. It is crucial for the performance and operation of any network, above all. Choosing the right topology for a organisations operating model can improve performance while also making it easier to spot issues, fix them, and allocate resources more wisely throughout the network to ensure the optimal network health[2]. A network topology diagram produced by software is frequently used to show and change the design and structure of a network. The primary benefit of using these diagrams is that they can provide users with visual representations of both logical and physical layouts, assisting them in understanding how the links between devices work during troubleshooting[3].An effective and well managed topology can increase data energy and efficiency, helping to save operating and maintenance costs. The way a network is set up may make or break how well it connects, functions, and is protected from downtime. Efficient network administration and monitoring require a full understanding of both the logical and physical topology in order to ensure that any network is reliable and effective[4]. The topologies that are used to organise systems come in a variety of forms.
II. TYPES OF NETWORK TOPOLOGIES
A. Physical Topology
It deals with the cables, wires, and other physical connections between various nodes. It involves placing devices and installing code as well as setting up various network components, such as links and nodes. It can be described more simply as the physical configuration of the network's nodes, workstations, and cables[5]. Physical topology describes how a network's various components are arranged. It depicts the actual configuration of the connections and equipment that make up a network. It neglects minor variables like data transfer and device type in favour of the network's core concerns. Depending on how simple it is to build and set up the network, nodes and network cables will be arranged in a particular configuration. The cost and bandwidth capacity depends on the device solution. It considers the positions of the nodes and their separation from one another. Devices may be connected in a bus topology or organised to form a Ring Topology.
B. Logical Topology
The arrangement of devices and their communication are reflected in logical topology. Data transmission through physical topology does not depend on node configurations or physical topology.
It is concerned with minute characteristics of the network, such as the type and calibre of equipment such as switches, routers, which influence the rate and speed of data packet transmission. The network's logical topology guarantees optimal flow control that is controllable. The flow of the data can either take the form of a circular logical ring or a linear pattern known as a logical bus.
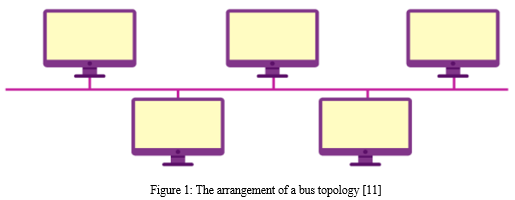
C. Bus Topology
In a network with bus topology, every system and device present is connected to a single wire. It transmits data from one end to the other in a single direction. There are line terminators on both ends of the shared channel. Any node that is to be send a signal through the network must first send a message to the network in order to do so. No matter who is the receiver the message is addressed to, all reachable stations in the network will get it. There are not any bi-directional properties in this. Given that the topology crashes if the backbone is compromised, it is a multi-point connection with a non-robust topology[6]. Line topology and backbone topology are some names for it. Data travels along the cable in the same direction. There may be problems if numerous hosts attempt to transfer data at the same time. Because of this, it uses CSMA/CD (Carrier Sense Multiple Access / Collision Avoidance) technology to solve the problem or designates one host as bus master. It is a fundamental form of networking where the failure of one device has no bearing on the functioning of the others. However, all other devices will stop functioning if the shared communication channel breaks down. It is frequently utilised in established networks, including 802.3 (Ethernet) and 802.4 networks[7]. The bus topology shown in Figure 2 illustrates how devices can be connected to one another via a network and how data travels from one end to the other.
- CSMA (Carrier Sense Multiple Access)
It is a sort of media access control that is used to control data flow in order to protect data integrity or to prevent packet loss. The issues that arise when any two nodes deliver messages at the same time are often handled using two alternative strategies.
2. Carrier Sense Multiple Access with Collision Detection (CSMA CD)
It is an access method that is employed to find data collisions. In the event that a collision is discovered, the transmitter will stop sending data. As a result, it concentrates on data collision recovery. This technique was created to lessen the likelihood of collisions occurring when two or more stations begin transmitting their signals over the data connection layer. Each station must first check the status of the medium while using carrier sense multiple access.
3. Carrier-sense multiple access with collision avoidance (CSMA/CA)
It is a method for preventing collisions that works by figuring out whether the gearbox medium is congested or not. The sender of the data will wait till the media is available if he is preoccupied. This effectively lowers the possibilities of a collision. After the collision, recovery is not supported. The fundamental TENET (Target Characterization using Network Topology) of CSMA/CA is that a station must be capable of receiving while broadcasting in order to identify a collision between two stations. In wired networks, if a collision has taken place, the received signal's energy nearly doubles, allowing the station to detect the potential for collision. In wireless networks, the majority of the energy is required for transmission, and if a collision happens, the energy of the received signal only increases by 5–10%. The stati on is unable to sense collisions using it. As a result, CSMA/CA was created specifically for wireless networks.
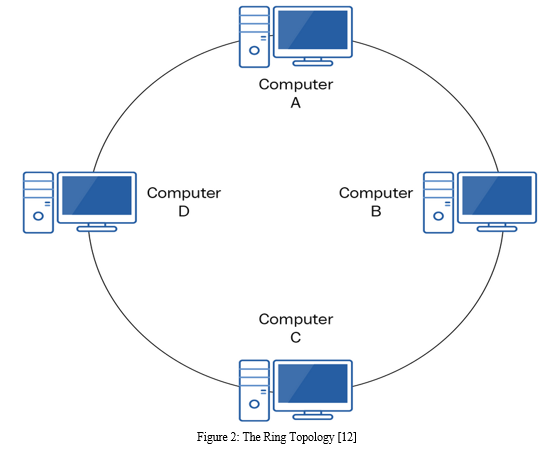
D. Ring Topology
In this type of architecture, each host machine is connected to exactly two more hosts, resulting in a circular network structure. Data is routed through all intermediary hosts if any host wishes to communicate with or send a message to another host that is not immediately adjacent to it. The system that receives the message from the one before it sends it to the one after it[8]. To add another host to the current configuration, the administrator might only need to use one more wire. The only distinction from bus topology is that it has connected endpoints. The data flow in this case is also restricted to one direction and occurs within a loop that never ends. Dual ring topology, on the other hand, is a bidirectional topology that can be achieved by providing two connections between each network node. There is no termination point because the two ends are linked . Data flows through it in a clockwise direction. When a ring topology with a large number of nodes is used, a lot of repeaters are required because in a ring topology with 90 nodes, data must travel via 89 nodes before reaching the 90th node[9]. Repeaters are used in the network as a result to prevent data loss. Figure 3 shows how the devices are arranged in a Ring topology and how the data travels in a loop.
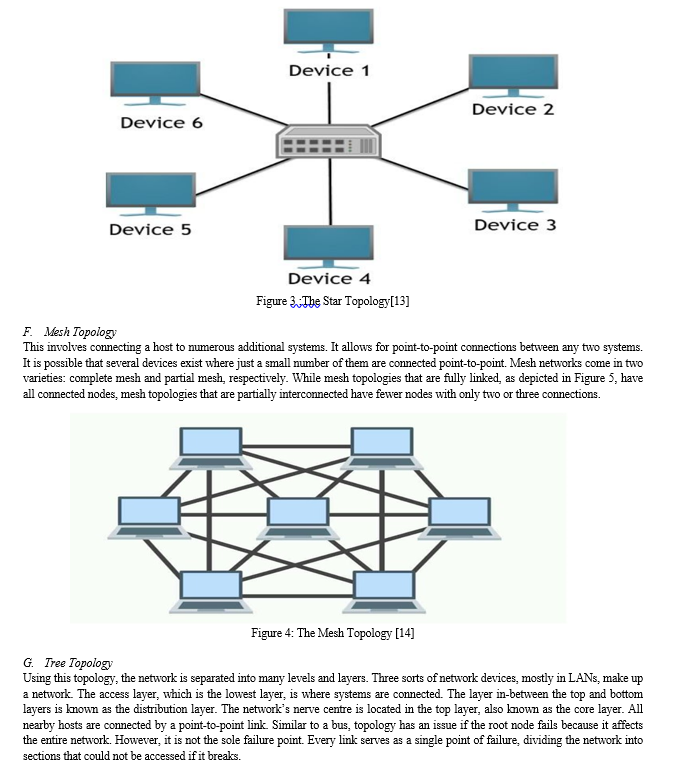
E. Star Topology
It is the most widely applied topology. In this design, a wire connects each system to a separate hub.The other nodes are connected to this hub, which serves as the central node. This hub could be intelligent, i.e., active hubs, or passive, i.e., not intelligent, like broadcasting devices. Hubs that are in operation contain repeaters. The devices linked to the primary computer are referred to as clients and the main computer as a server. Coaxial cable or RJ-45 connections are used to link the devices together[10]. Hubs or switches are generally used as connecting devices in a physical star design. There is no direct device connection in this scenario; all systems must first communicate with the hub. Information transmitted from any network node must pass via the main system, which serves as a repeater and prevents data loss, in order to reach its destination. Figure 4 shows the Star topology of linked devices and the data flow between them.
H. Hybrid Topology:
We may describe it as a combination of different topologies. These are frequently utilised in large, multinational corporations where each department has a unique organisational structure. These give the network system a tonne of flexibility. Depending on the user's needs and requirements, several topologies can be selected and put into use.
III. NETWORKING AND NETWORK TOPOLOGIES
Computer science is an important and wide branch of engineering. There are various subjects, which are included in the course, which are important for students to have knowledge of such as Analysis of Algorithms, Data structure, Database management, and Networking. These are the subjects, which are important while preparing for several competitive exam, interviews and technical examinations. These subjects comprises of algorithms, laws and concepts, which are basis for development of various software programs. One such subject is networking, which includes ideas like network terminologies, network topologies like the star, bus, mesh, tree, and ring topologies, various kinds of computer networks, protocols like the Hyper Text Transfer Protocol (HTTP), Transmission Control Protocol (TCP), and many others that guarantee the safe and efficient transfer of data.
Conclusion
The term network topology refers to a variety of topologies that describe the connections between various devices for the purpose of exchanging data. Different topologies can be categorised according to several factors. In this study, these topologies have been covered. This work has examined the significance of various topologies. It is described how device layouts are performed in different topologies. This study discusses ring topology, including its diagrammatic representation, benefits, and drawbacks. Similar to this, this work has discussed a number of alternative topologies, including mesh, star, bus, tree, and hybrid topology. All of these, from tiny businesses to large corporations, have their own unique networks that connect various equipment. These connections are made while considering the advantages of various topologies, and they are then made in accordance with those considerations. As new businesses open up every day, these topologies are increasingly needed, expanding their potential application in the future.
References
[1] E. Ozkan-Canbolat and A. Beraha, “Configuration and innovation related network topology,” J. Innov. Knowl., 2016, doi:10.1016/j.jik.2016.01.013. [2] E. Ozkan-Canbolat and A. Beraha, “A configurational approach to network topology design for product innovation,” J. Bus. Res., 2016,doi: 10.1016/j.jbusres.2016.04.115. [3] D. L. Harrington et al., “Network topology and functional connectivity disturbances precede the onset of Huntington’s disease,” Brain,2015, doi: 10.1093/brain/awv145. [4] G. Engels et al., “Clinical pain and functional network topology in Parkinson’s disease: a resting-state fMRI study,” J. Neural Transm.,2018, doi: 10.1007/s00702-018-1916-y. [5] X. Diego, L. Marcon, P. Müller, and J. Sharpe, “Key Features of Turing Systems are Determined Purely by Network Topology,” Phys.Rev. X, 2018, doi: 10.1103/PhysRevX.8.021071. [6] E. Heasley, N. Clifford, and J. Millington, “Integrating network topology metrics into studies of catchment-level effects on habitatdiversity,” Hydrol. Earth Syst. Sci. Discuss., 2018, doi: 10.5194/hess-2018-89. [7] V. Deshpande, H. Badis, and L. George, “BTCmap: Mapping bitcoin peer-to-peer network topology,” in 2018 IFIP/IEEE InternationalConference on Performance Evaluation and Modeling in Wired and Wireless Networks, PEMWN 2018, 2018, doi:10.23919/PEMWN.2018.8548904. [8] B. Bangerter, S. Talwar, R. Arefi, and K. Stewart, “Networks and devices for the 5G era,” IEEE Commun. Mag., 2014, doi:10.1109/MCOM.2014.6736748. [9] G. Rosell-Tarragó, E. Cozzo, and A. Díaz-Guilera, “A complex network framework to model cognition: Unveiling correlation structuresfrom connectivity,” Complexity, 2018, doi: 10.1155/2018/1918753. [10] L. M. Wierenga et al., “A multisample study of longitudinal changes in brain network architecture in 4–13-year-old children,” Hum.Brain Mapp., 2018, doi: 10.1002/hbm.23833 [11] https://byjus.com/gate/bus-topology-notes/ [12] https://subscription.packtpub.com/book/cloud-and networking/9781838643508/6/ch06lvl1sec44/ring-topology [13] https://circuitglobe.com/difference-between-star-and-ring-topology.html [14] https://www.edrawsoft.com/article/mesh-topology.html [15] https://www.geeksforgeeks.org/difference-between-star-topology-and-tree-topology/
Copyright
Copyright © 2023 Muhammad Arif Bin Jalil. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET55654
Publish Date : 2023-09-07
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

