Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Tracking and Management of Deforestation and Related Activates using Blockchain and IoT
Authors: Aditya P. Khandelwal, Karishma Nair
DOI Link: https://doi.org/10.22214/ijraset.2022.46521
Certificate: View Certificate
Abstract
Objective- To conceptualize a system using a fusion of Blockchain and IoT to keep track of deforestation and related activities and maintain a distributed public ledger of the same. Methods-IoT network detects deforestation or related activities using extrapolation of data generated, and thus updating the Blockchain with the same. It will create a public ledger with all the information related to the region wherein the system is deployed. Concerned authorities would be apprised, and commensurate action would be taken in case some illicit activity is detected by the central node of the IoT module. Novelty-Novelty lies within the program, which would use the data generated by the IoT module, use it to infer the activities, initiate response actions and update the data on the Blockchain.
Introduction
I. INTRODUCTION
The majority of the earth's terrestrial biodiversity is covered with forests. The way we interact with and use the world's forests has become crucial for conserving the world's biodiversity. 80% of amphibian species, 75% of bird species, and 68% of mammals consider forests home. Tropical woods are home to over 60% of all vascular plants. Forests cover 31% of all surface area on the planet, but they are not evenly distributed. These statements are sufficient to emphasize the significance of forests. Almost half of the forest is substantially intact, with primary forest accounting for more than a third [2]. Even though afforestation has been rising in recent decades, the net area of forest has abated. Since 2010, the world's net forest cover has decreased by 4.7 million hectares per year on average. Deforestation rates, on the other hand, are much significantly higher. According to the United Nations food and agriculture organization (FAO), 10 million hectares of forest are cut down every year [3]. The persistently high net forest loss and even higher deforestation rates are strong indicators that present anti-deforestation movements, and the legislation is ineffectual or rife with loopholes.
According to the report (CBD, 2016), illegally obtained round wood and sawn wood account for 42% of global round and sawn wood commerce, worth an estimated Rs. Four hundred twenty-seven billion per year [4]. Not only do illegal markets for various forest-derived products sourced from deforestation, but so do the establishment of organized crime syndicates indulging in forest-related sup, soil erosion, species loss, economic losses due to forest fires, and annual carbon emissions due to deforestation. Furthermore, deforestation and the conversion of wooded lands to grow other commodities or raise animals emit almost 1.5 gigatons of carbon per year, roughly the same as Russia's yearly emissions [5]. We aim to propose a tamper-proof digital ledger based on blockchain technology to enable a way of tracking forests. IoT will be used to verify the status of trees; Blockchain will be integrated with digital protocols to create the ledger. Hence the ledger will be tamper-proof and publicly available, thus maintaining transparency and will also keep track of the deforestation rate.
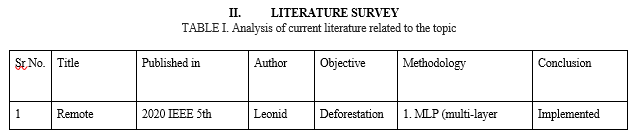
III. METHODOLOGY
A. kchain Technology
Satoshi Nakamoto first envisioned and conceived the Blockchain in 2008 as the technology behind Bitcoin, but since then, it has been delineated in various ways. The most widely accepted definition is that it is an open, shared, decentralized, and distributed digital ledger in which transactions and data pertaining to the parties involved in the transaction are recorded and added in chronological order to permanent and tamper-proof records [6]. Distributed ledger (DLT) technologies include Blockchain, which is a system based on a distributed ledger—that is, a system in which all network nodes have a duplicate copy of a database that can be read and edited independently by the individual nodes. The four principal qualities that distinguish blockchain technology from other information system initiatives are (a) decentralization, (b) security, (c) authenticity, and (d) smart execution [7]. Because Blockchain employs high-level hashing, it is tamper-proof and resistant to any attempt to alteration or modification.
A smart contract is a computer protocol for digitally facilitating, verifying, or enforcing a contractual obligation under predetermined terms. Smart contracts, which are incorporated in blockchain networks, enable and facilitate the execution of credible, trackable, and irreversible transactions without the involvement of third parties. These transactions can be in the form of data transfer or updating and execution of some task after the prerequisite conditions are met, monetary transactions or any other manner in which they are programmed.
B. Defining The Stumbling Block
An implied fact is that the methods currently employed to keep track of deforestation and related activities are opaque and based on behemoth changes in the forest landscape. There is no way we can keep track of every single tree or a small group of trees, for that matter, over a long period of time. As it is said, "Petals make a flower garden" every single tree matters. Thus, one possible solution for revolutionizing the forest management techniques forever could be by creating and maintaining a public distributed ledger which accounts for all of them along with the added jewel of diaphony, which is the most sought-after characteristic by the general population these days.
- An Immutable Public Ledger Of All The Trees: As we can conclude from the current reports and records of the still prevailing deforestation and the inaccuracies in the same., we are proposing a system through which record of every single tree would be kept on a public blockchain wherein every physical tree present in the area would have its unique identity on the chain along, its current status, whether it is standing or has been taken down if it was permissioned or illegal, could also be found out using the Blockchain. The proposed system can be broken down into two autonomous methods that working together would give us information about the tree, its unique identity on the Blockchain, whether it is erect or not, and if it fell, was it permissioned and for what reason. It would also alert the concerned officials as soon as a tree has fallen or a forest fire ignited, along with a method to trace its location, its legality and take the necessary actions.
C. Proposed Approach
The proposed approach can be understood as a synchronized working of two different models, structured as follows
- Representing And Maintaining A Public Ledger Of All The Trees And Their Location
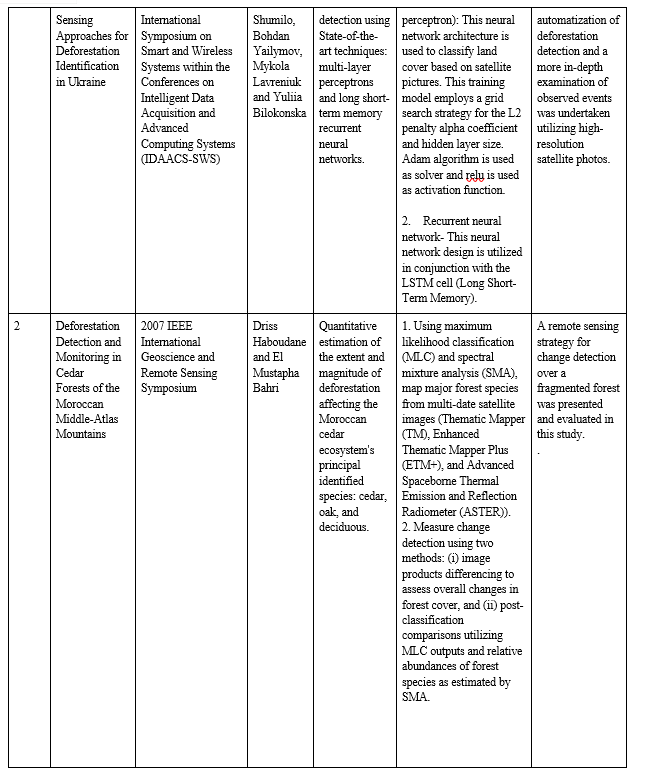
The proposed system can be visualized in the following manner:
a. Tags: These are basic solar-powered wireless sensors which can give two states, i.e., on or off. A network administrator issues the tags for each router and registers it on the router with a unique id which would later become the physical identity of the tree it is linked to (physically attached). These tags in the "On" state represent that the tree associated with it is erect, not authorized to be taken down, no matter whatsoever. The state of all these tags would be given to a router which would, in turn, pass on the state of all the associated tags to the CIS. The tags should be randomly placed on every tree such that there is no possible algorithm through which they can be traced and removed from trees covering a large area, thus failing or tricking the system.
b. Routers: These are intelligent devices used to link many tags to the CIS. Each router's Ip address would help trace the region's geographic location where the associated tags of the trees are present. The tags would be registered to the router by their Ip address/ or the location's coordinates where the tree is present. This system would help to perusal trees over a large area, or if pushed to its limits, the scalability could cover the globe. Every router would be connected with CIS, which would take the state of tags (on or off) and update the Blockchain after a predetermined time interval. Customized routers for this specific purpose can also be designed such that they support a large number of tags with a good range of communication and in which registration of each tag would be using its unique name (assigned by the network operator), which would help identify the physical tree linked to it on the Blockchain and trace its location.
c. Network Administrator: The network administrator's responsibility is to overlook the working of the entire model and, in some unusual scenarios, to override the network. The regular tasks of a network manager would include issuing tags linked with unique identities to trees, attaching the tag to the tree physically, requesting the turning off of tags in case of an authorized tree falling, randomly inspecting the entire routing network and whether the digital and physical identity of the tree is aligned and handling of cases wherein the illicit falling of trees is done, and flags have been raised. They are basically people who will take care of the smooth running of the entire network and check the accuracy of data uploaded by the CIS on any given day and take necessary steps according to their observations.
d. Central Intelligence Server (Uses A Heuristic Approach): The CIS is the heart of the network whose work will be based entirely on a smart contract which is to be designed such that it sustains and automates the whole procedure of having the digital identities of trees on a public blockchain, updating the Blockchain about the tress erect and the ones which were fallen along with the justification in case of authorized deforestation or the legal action taken against the preparators in case of illicit activity. CIS will take the records of all the tags linked with different routers and the routers then linked to CIS, check their state, and create the primary database of all the region's trees. Then, it will upload these databases on a public blockchain so that everyone can know the state of forest / preserved areas and will be able to keep an accurate distributed and immutable record of the same. If some deforestation is to be done or even if only a few trees of such a region are to be fallen, the network manager should first give the CIS all the required details and the permissions from the concerned authorities. If the reason is from a predefined set of conditions due to which removal of the tree is allowed, which would be programmed during the generation of the smart contract, the CIS will turn off the tag associated with the given trees if it approves permission. If the tags of a specific tree/ region are On and the tree falling detection model detects the falling of trees whose tags were on, it will immediately notify the concerned authorities and update the Blockchain with an illicit activity state related to the tags. The authorities need to check into the region and submit a report to the network manager as soon as they arrive on-site about the issue, later moving that information to the CIS to upload on the Blockchain. In this way, a near real-time investigation log would be maintained, and the public could actually verify the facts provided by the authorities by conducting individual investigations of that region. If in case the authorities have misreported any scene which is later found, and the proofs of such malpractice are submitted on the network, strict legal/criminal action would be taken against the officials involved. This would retain a sense of responsibility in them as their reports could be verified by anyone anywhere, and they would be held accountable for their actions. The nodes, as stated above, will form the network identity of trees belonging to a region. This topology could be scaled and made available across the whole globe, which would thus create an immutable record of all the trees present, would present a clear report of the current situation and encourage populations to increase afforestation rapidly as the results would be available and visible, people will have more general enthusiasm for the same.
2. Autonomous Forest Deforestation Alert System
For the execution of this module, we have selected two distinct methods, which are: -
a. Constructing an IoT module using sensors
b. Using the temporal density of forests as observed by satellites.
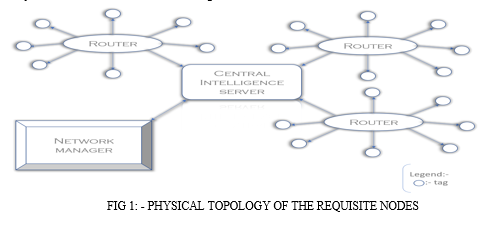
D. IOT Module Using Sensors
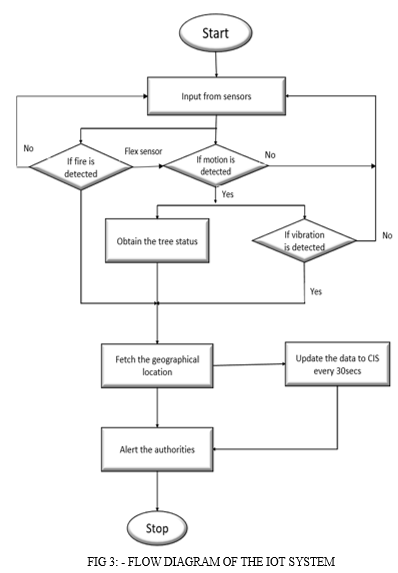
Using a system consisting of a flex sensor, relay, GPS, GSM, flame sensor, accelerometer, real-time deforestation and forest activity monitoring can be done [9]. The proposed system will work as follows: -
- Flex Sensor: The bending strip principle is used in this sensor, which implies that as the strip is twisted, the resistance changes. With the use of any controller, this can be determined. Because the resistance changes when the sensor twists, it works similar to a variable resistance. Because the resistance will be dissimilar when the surface is level, the resistance change can be influenced by the surface's linearity. The flex sensor will be fixed to the tree trunk to detect the bending of a tree.
- Accelerometer Sensor: The accelerometer is installed directly on the vibrating object, transforming the vibration energy into an electrical signal proportionate to the object's momentary acceleration. In case of sudden falling, instantaneous acceleration can be detected, which along with the data of the flex sensor, can be used to extrapolate that a tree has fallen.
- Flame Sensor: A flame sensor is a detector primarily used to detect and respond to the occurrence of a fire or flame. A flame detection reaction can trigger an alarm system. Because of the mechanism used to detect the flame, the reaction of these sensors is faster and more precise than that of a heat/smoke detector. This sensor/detector can be made with an electronic circuit and an electromagnetic radiation receiver. The infrared flame flash method is used in this sensor, which allows it to work through a layer of oil, dust, water vapour, or ice.
- PIR Sensor: An electrical sensor that measures infrared light emitted by objects is known as a passive infrared sensor. Infrared radiation is emitted by all objects and living beings with a temperature higher than absolute zero. The more infrared radiations are emitted, the warmer the thing; hence the PIR sensor is a thermal infrared sensor that detects item motion by measuring fluctuations in infrared radiation in its immediate environment, which is emitted by all living organisms. The sensor interprets these changes in pulses as motion in its detecting zone. A gird of such PIR sensors on the forest ground would help in detecting the falling or sudden random moments of trees. The same will be triggered by animals, but the program is to be designed such that these situations are not considered flags.
- GPS: The Global Positioning System (GPS) is an acronym for Global Positioning System. Satellites and ground-based control stations are part of the system. The GPS sensor comprises a surface mount chip that processes signals from GPS satellites using a small rectangular antenna that is usually installed on top of the GPS chip. GPS will be used to pin the locations of routers, which would give access to the region or its linked trees.
- GSM: GSM (Global System for Mobile Communication) is a technology that allows mobile data and voice services to be transmitted. It was established to explain the protocols for mobile phones' second-generation (2G) digital cellular networks, and it is now the global standard for mobile communications. This will be used for intra-network communications.
- Raspberry Pi: The Raspberry pi is a single computer board with a credit card size that can be used for many tasks that your computer does. The Raspberry Pi runs Linux (several versions), and its primary supported operating system, Pi OS, is open source and runs a suite of open-source software; this provides this system with dynamic development scope such that contributors across the globe can suggest improvisations in its operation. The central node, i.e. CIS, would consist of a Raspberry Pi, which would take the inputs from all the sensors and would create specific results based upon their inputs and transfer that to the CIS.
The following sensors would be used to make up an IoT based system which would function as: -
The PIR (passive infrared) sensor grid will be implanted near ground level. PIR working along with accelerometer and flex sensor would generate data, an amalgamation of which can be used to extrapolate tree falling motion as flex sensor would detect bends, accelerometer the sudden acceleration while falling of trees and the PIR grid will detect the sudden change in the vicinity of the sensors thus forming an IoT network which can be effectively used to detect deforestation. If such deforestation is detected by the network, the geolocation of the tags of the trees where it occurred is accessed by the router and updated on the CIS, which will take further actions.
The flame sensor would be used for fire detection; once it is detected, the sensor would give the input to the router, which along with the geolocation of the fire using the GPS, alert the officials and update the information on the Blockchain about the trees affected. The authorities would be compelled to put the reports on the Blockchain through the network manager after the completed situation is taken care of. All this data would be available to the public for analysis.
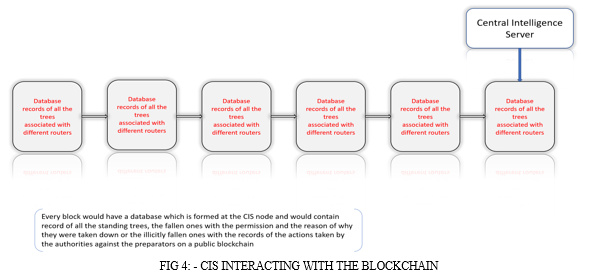
CIS will periodically update the Blockchain with all the databases it receives from the tags, routers and IoT system, which would be timestamped; thus, the data created would support 3dimensonal searching. The difference between traditional and the stated Blockchain is that in traditional Blockchain, the right to add the block is given to the node, which solves a complex computational problem to get the authority to add a block, unlike that in the proposed Blockchain, only the CIS nodes of different regions will have the authority to add blocks and update the data of Blockchain. End-user can only view an immutable record stored over time since the dawn of the system, which will keep the record of every tree and could be verified physically along with the access to the location where a particular tree is present using the combination of CIS address, Router Ip and the tag names or the GPS location fetched by the IoT system. It will be the central block of processing all the information and decision-making.
Another method which could be used instead of the IOT is: -
E. Using The Temporal Density Of Forests As Observed By Satellites
An alternate solution for deforestation detection is using Sentinel-1 time series with Landsat and ALOS-2 PALSAR-2. Independent of weather, season, or location, combining observations from several optical and synthetic aperture radar (SAR) satellites can offer temporally dense and regular information at a medium resolution scale. This has the potential to improve near-real-time deforestation monitoring in dry tropical locations, where standard optical-only monitoring methods are hindered by constant cloud cover, resulting in limited data availability. A combination of Sentinel-1 C-band SAR time series, ALSO-2 PALSAR-2 L-band SAR, and Landsat-7/ETM+ and 8/OLI can be used to demonstrate multi-sensor near-real-time deforestation identification in tropical dry forests [8]. Once deforestation is identified using the imagery, the tags of that region could be traced using the router and CIS location and then checked for their status. If already turned off would imply that deforestation was permitted. Else, the authorities would be notified of the illicit/ permissionless deforestation taking place along with its location.
IV. RESULTS AND DISCUSSION
A. Scope And Scalability
- Forest is an invaluable resource, which is exhausting at an unprecedented rate due to deforestation; the massive afforestation campaigns feel redundant because the net forest is reduced by millions of hectares per year on average. Deforestation also contributes 8-10% of our annual carbon emissions [9], rapid global warming, loss of topsoil and many other environmentally detrimental effects, thus raising the scope of implementation of the proposed model to manage the same.
- Development of pan globe network wherein sensors and devices used are designed and adapted to the regions and needs of where they are implemented intended to create a distributed public ledger of information of the situation of trees in the forests and other protected areas.
- The most significant feature of the proposed system lies within the fact that it takes the information about a public concern as forest resources and its management, which traditionally was inaccessible to the common people because it was present and handled by few central authorities, and gives the power to the periphery, i.e., the power to access, validate and take necessary action if needed in the management of an exhaustible resource.
- The model could be extended to monitor the trees in non-protected public areas like parks, metropolitans, villages etc.
- Targeted and statistical deforestation would lead to better forest regeneration & causing less detrimental impacts, all the while providing essential forest supplies.
- Implementation and management of legislation and related laws in the preserved territories will be more accessible and more transparent to the public.
- Accountability of the concerned officials and the general public spirit related to maintaining the forests and related resources would increase drastically.
B. The Possible Scalability Issues Which Could Arise In Its Application Are
- The development of sensor devices according to the exact requirement will be done over time, and the specifications of such devices will change from region to region.
- Natural calamities like earthquakes, tornadoes, thunderstorms, forest fires etc., would disrupt the network in the region where they occur.
- CIS would prove to be a single vantage point for attacks and therefore needs to be secured accordingly.
- The wide acceptance of the proposed method will need the approval of various governments and international organizations.
Conclusion
The rate of illegal deforestation and reforestation can be recorded and made public using this approach. Records of when, where, and how deforestation occurs, whether it is as a result of fire or tree cutting or as a result of high surrounding temperatures, may be recognized and saved in an immutable ledger. The system would also notify concerned officials as soon as a tree fell or a forest fire ignited and initiate a protocol to track its position, determine its legality, and take appropriate action. As a result, it will be possible to combat tree smuggling, raise public awareness of primary forest degradation, and improve enthusiasm in the general population about afforestation as they will be able to keep track of their plantation in an immutable form.
References
[1] The state of the world\'s forests, Food and Agriculture organization of the United Nation. Available at: https://www.fao.org/state-of-forests/en/ [2] Forests and deforestation, Our World in Data organization. Available at: https://ourworldindata.org/forests-and-deforestation [3] Sheikh Fahad Ahmad, Deepak Kumar Singh, Automatic Detection of Tree Cutting in Forests using Acoustic Properties, Journal of King Saud University, Computer and Information Sciences, Volume 32, Issue 10, December 2020, Pages 1208-1209. Available at: https://www.researchgate.net/publication/330826950_Automatic_Detection_of_Tree_Cutting_in_Forests_using_Acoustic_Properties [4] Illegal Logging and Deforestation, US Agency for International Development. Available at: https://www.usaid.gov/biodiversity/illegal-logging-and-deforestation [5] Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008. Available online: https://bitcoin.org/bitcoin.pdf [6] Saberi, S.; Kouhizadeh, M.; Sarkis, J.; Shen, L. Blockchain technology and its relationships to sustainable supply chain management. Int. J. Prod. Res. 2019, 57, 2117–2135. [7] Johannes Reiche, Eliakim Hamunyela, Jan Verbesselt, Dirk Hoekman, Martin Herold, Improving near-real time deforestation monitoring in tropical dry forests by combining dense Sentinel-1 time series with Landsat and ALOS-2 PALSAR-2, Volume 204, 2018, Pages 147-161, ISSN 0034-4257. Available online : https://www.sciencedirect.com/science/article/pii/S0034425717304959 [8] Raghavendra L R, Vivek B T, Suhas Gowda K R, Vijay Kumar M , Vineeth M S, IOT based illegal tree cutting prevention and monitoring with web application, International Journal of Scientific Research and Engineering Development-– Volume 2 Issue 3, May –June 2019. Available at: http://www.ijsred.com/volume2/issue3/IJSRED-V2I3P33.pdf [9] Deforestation and climate change, Climate Council newsletter. Available at: https://www.climatecouncil.org.au/deforestation/
Copyright
Copyright © 2022 Aditya P. Khandelwal, Karishma Nair. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET46521
Publish Date : 2022-08-29
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

