Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Smart Voting System Using Facial Recognition
Authors: Abbas Behrainwala, Amar Saxena, Ishika Navlani, Sakshi Sahay, Noshir Tarapore
DOI Link: https://doi.org/10.22214/ijraset.2022.39810
Certificate: View Certificate
Abstract
In this paper a new authentication technique is discussed i-e; facial recognition verification for online voting system. It aims to develop a computerized voting system to make the election process more secure and user friendly. The electorate want to visit distinct locations like polling cubicles and stand in an extended queue to cast their vote, because of such reasons most of the people skip their chance of voting. The voter who isn\'t eligible also can forged its vote via way of means of faux way which can also additionally cause many problems. That\'s why in this project we have proposed a system or way for voting which is very effective or useful in voting. This system can also save money of the government which is spent in the election process. Overall this project is being developed to help staff of election commission of India and also reduce the human efforts.
Introduction
I. PROBLEM STATEMENT
The basic methodology as applied to online voting systems would involve giving voters realistic voting tasks to accomplish using a variety of ballot design. Voting task performance is measured using variables such as accuracy, time and workload. The voting server collects the vote and filters out duplicate or invalid votes. Each voter can then check his vote online to ensure that his vote has been counted.
II. INTRODUCTION
Election plays an important role in such a huge democratic country like India where the leader is elected by residents.Elections preserve a truthful state functioning, as they provide people the choice to select their personal government. So the election ought to be an unfastened and truthful process. Every citizen of a democratic country has a right of voting with his/her own choice. One of the fundamental issues in the conventional democratic framework is that it expends bunches of labor and resources.Also some humans can be worried about illegal publications of movement at some point of this manner of election or its preparation. There are some disadvantages of the conventional election voting process which is being used in our country such as machine stops working, chances of brutality, time consuming, resource consuming, spot arranged etc. Many people couldn't vote because the voter has to reach the poll booths to vote or some people like those who are living far away from their original birth place where they are allowed to vote. So to get rid of their drawbacks, a new System is introduced i.e. Online Voting System, which provides accuracy, security, flexibility, mobility etc. An online voting System in a web based application to use in the election process. Initially ballot paper technique was used in the election process. Then the Electronic Voting Machine comes, these are easy to store the data and easily manageable. These are more secure than the ballot paper and less time consuming.Now, we proposed a system with biometric authentication to make the voting process more secure and reduce the time taken in the voting process. By the use of this, the electorate can solidify their vote for his or her preferred candidate through the use of their system. We use Face detection and Recognition Technology for authentication of citizens that he/she is the proper consumer or not. We provide many modules in which admin can login withinside the tool and show the numerous operations.Also users can login in the system and use their right to vote. When the Voter uses the system, the system will capture his/her image using a web camera & try to match with the image stored in the database. If both images are the same then the voter can cast his/her vote. Most higher learning establishments in Kenya conduct elections routinely to elect an understudy leadership to choose them. They proposed the process of an online system, which includes systems like enlistment of voters, vote casting, vote checking, and pronouncing results which would establish a decent answer for a substitute of framework that is in the institutes in Kenya.
III. MOTIVATION
This project revolves around the development of an online voting system that employs facial recognition registration as well as the use of a one-time password generated for each voter per election, which will allow voters to participate in the elections regardless of their physical location. Following Academic Staff Elections in the University of Ibadan as the case study for the system to be developed.
IV. AIMS AND SCOPE OBJECTIVES
The aim is to develop an application that seeks to use various stages of security authentication to enhance the election process for political party elections using the real case study, i.e.The University of Ibadan, in the end imparting an internet platform which permits all eligible electorate to workout their franchise from any region for the duration of the election period. The targets are:
- To create a secured online voting platform where authenticity of votes and voters are ensured with the use of mechanisms such as facial recognition and one – time password
- To enhance Voter’s identity due to the fact that biometric functions can not be shared.
- To ease the trouble of queuing in the course of balloting duration in elections.
V. EXISTING SYSTEMS
The existing system is not too effective. At present there are two types of voting methods, they are:
- Ballot Voting
- EVM Voting
A. Ballot Voting
A ballot is a device used to cast votes in an election, and may be a piece of paper used in secret voting. In this the voter is given a paper which consists of all the party symbols along with representative names in it. Here, people come to the polling booth, take the ballot paper and vote by putting a stamp on the desired party symbol. Finally, the ballot paper is folded and dropped into the ballot box. At last, the votes are counted by the Election commission officers.
B. EVM (Electronic Voting Machine) Voting
An EVM is a device which is used for voting. This machine consists of party symbols along with the representative’s name and a button at the end for each and every party name. The voters come near the EVM machine after completion of their verification at the early level before voting. After verification the voter goes near the EVM and casts their vote by pressing the button. The above procedures are not so accurate as there may be possibility for the false/fake voting. The ballot papers may be lost at the time of counting which may affect results of the particular area or people may miscount the number of votes which leads authority into wrong hands. EVM machines sometimes get corrupted and polling gets stopped temporarily and a lot of time is wasted or EVM may be tampered and the casted votes may be polled to a particular party only, even the vote is casted to different candidates or parties. This may lead authority into the wrong hands.They also lack security as one’s vote can be casted by another voter or even a miscellaneous person. This factor is known as fake voting. Without proper authentication there is a possibility of fake voting. So, the existing system is not efficient for voting. Even though there is very little false/fake voting, this minor setback can turn the results in the opposite direction.
VI. RELATED WORK
Several authors have put in efforts in the field of face recognition, significant contributions are briefed in the literature review. Vigorous technique [3] for naturally coordinating highlights in pictures compared to the equivalent physical point on an item observed from two discretionary perspectives. Unlike conventional stereo matching approaches coordinating methodologies, the presumption like no earlier information about the relative camera positions and directions. Actually in this application this is the data wish to decide from the picture feature matches. Highlights are distinguished in two or more pictures and portrayed utilizing affine texture invariants. The fundamental test is the way to improve the recognition performance when influenced by the fluctuation of non-linear effects that incorporate illumination variances, poses, facial expressions, occlusions and so on. A robust 4-layer Convolutional Neural Network (CNN) [4], engineering is proposed for the face acknowledgment issue, with an answer that is equipped for dealing with facial pictures that contain occlusions, poses, facial expressions. There are many face recognition algorithms, just a bunch of them meet the continuous limitations of a software based arrangement without utilizing any committed hardware engine. This paper presents a real-time and robust solution for mobile platforms [5], which in general have limited computation and memory resources as compared to PC platforms. This solution includes joining two previous real-time implementations for mobile platforms to address the shortcoming of each implementation. The main execution gives an on the web or on-the-fly light source adjustment for the second usage which is seen as robust to various face postures or orientations. Pattern classification approach by considering every pixel in an image as a coordinate in a high-dimensional space is discussed in [6].
Along with the upside of the perception that the images of a specific face, under fluctuating illumination but fixed pose, lie in a 3D linear subspace of the high dimensional image space—if the face is a Lambertian surface without shadowing. In any case, since faces are not genuinely Lambertian surfaces and in fact produce self-shadowing; images will deviate from this linear subspace. As opposed to explicitly projecting this deviation, linearly project the image into a subspace in a way which limits those regions of the face with huge deviation. Design and execution of the component extraction strategy for Speeded-Up Robust Features (SURF) and Support Vector Machine (SVM) grouping technique into the traffic signs recognition application is deliberated in [7]. The yield of this application is the importance of the traffic sign with two languages, Indonesia and English. In the SURF strategy, the littlest huge number of key focuses will influence the accuracy level to perceive a picture. Face detection is the premise of all the face processing systems, while in video the face detection issue has more special importance. By examining the face detection dependent on Adaboost algorithm, this paper presents a quick and good robust face detection method. Firstly, the motion region which contains faces is obtained based on motion detection, excluding the background interference. Secondly, the Adaboost algorithm is used to detect the face in the motion region and locate the face. The experiments show that this method can rapidly and accurately detect human faces [8]. The face recognition and tracking and the advancement of the customer side of the system uses Android cell phones. For the face recognition stage, Viola-Jones algorithm is used that isn't influenced by illuminations. The face tracking stage depends on the Optical Flow algorithm. Optical Flow is implemented in the framework with two component extraction strategies, Fast Corner Features and Regular Features [9]. Real-time robust technique is created to distinguish irises on faces with coronal axis rotation within the normal range. The technique permits head movement without any limitations to the background. The technique depends on anthropometric templates applied to recognize the face and eyes. The template uses key features of the face, for example, elliptical shape, and location of the eyebrows, nose, and lips [10].
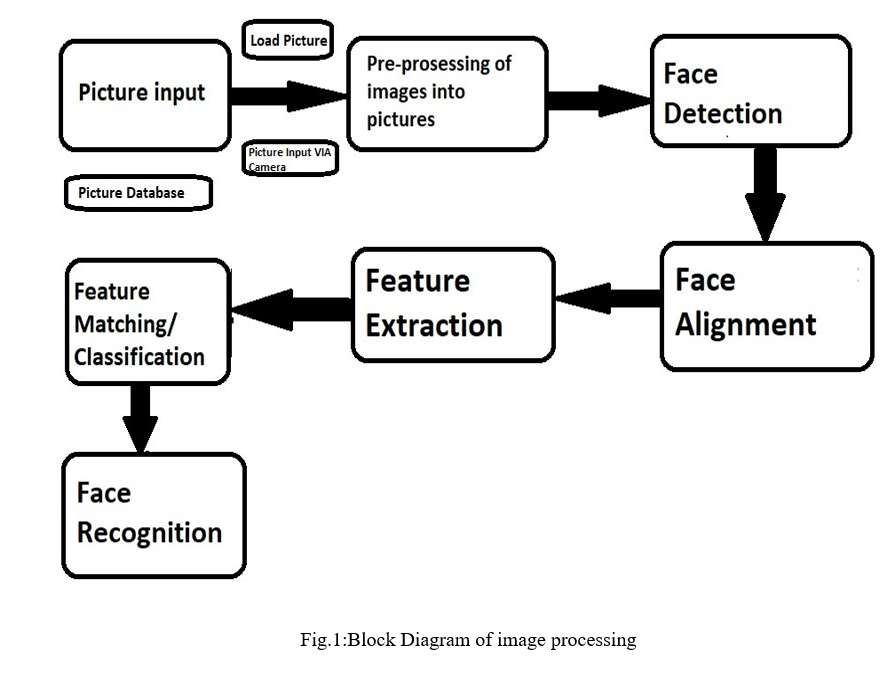
A. Block Diagram of Image Processing
The Block diagram below (Fig.1) shows the steps for processing the image and then storing it into the database. The image is taken as input and then it is pre-processed into pictures and then the next step is face detection and face alignment. After these steps the features of an image are extracted and are matched with the original image after that only the image is stored into the database
B. Architecture
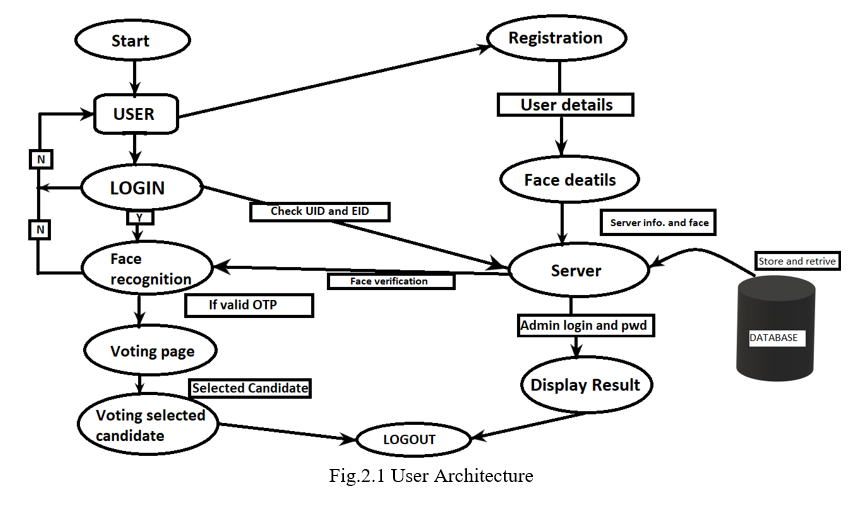
The Image above (Fig.2.1) shows the User Architecture. The user must be a registered voter to vote for the elections, if he/she is a new user then he/she has to first register himself/herself for voting.
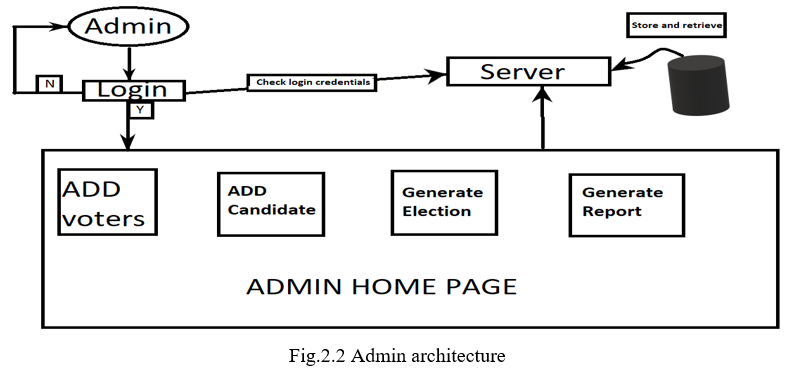
Fig.2.2 shows the architecture of the admin.Admins can control polling booths, they can also declare results when the elections are held.
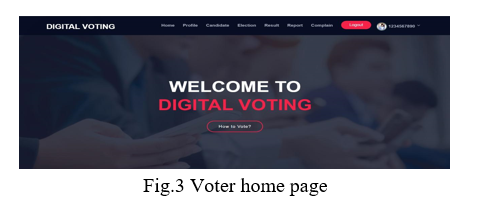
The above figure (Fig.3) is the home page of the user/voter for the Digital voting system. Here a voter can either check the results or vote for his/her favourite candidate. The user can also file a complaint if any.
The figure above(Fig.4) is the login page for the user/admin where he/she has to enter his/her login credentials first to verify himself/herself by entering a correct password.
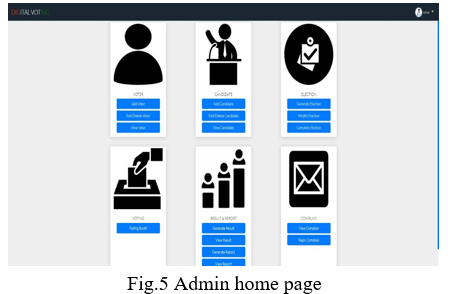
The above figure(Fig.5) is the admin home page which is controlled only by the admin where the admin can add election details and also register new voters, the admin can as well check the results and declare them.
C. Analysis
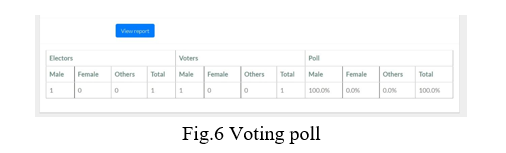
The figure above(fig.6) shows the voting poll from our web page that we have built. It shows the number of electors and voters.
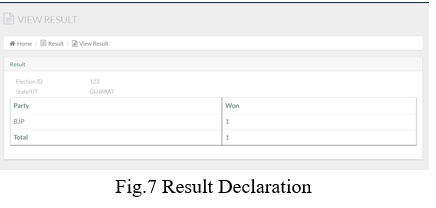
This image(fig.7) shows results that were declared by the admin.
As we can see in the picture above, political party is BJP.
Along with that it is also showing us the unique Election Id of each voter which is 123 and state name i.e Gujarat
In our system, voters can cast their vote anytime, anywhere by selecting their political party symbol at a time. When elections are over, their vote will get noted and after giving vote their voting data will be deleted. After that, Admin can show the result in the form of a dashboard.
Conclusion
We proposed the process of an online system, which includes systems like enlistment of voters, vote casting, vote checking, and pronouncing results which would establish a decent answer to substitute for the framework that is in the institutes in Kenya. The aim is to develop an application that seeks to use various stages of security authentication to enhance the election process for political party elections using the real case study, i.e. the University of Ibadan, ultimately providing an online platform which enables all eligible voters to exercise their franchise from any location during the election period.
References
[1] Shrivastava, Vishesh, and Girish Tere. \"An analysis of electronic voting machines for their effectiveness.\"International Journal of Computing Experiments (IJCE) Vol 1 (2016): 8-12. [2] Abdulhamid, S. M., Adebayo, O. S., Ugiomoh, D. O., & AbdulMalik, M. D. (2013). The Design and Development of Real-Time E-Voting System in Nigeria with Emphasis on Security and Result Veracity. International Journal of Computer Network and Information Security,5(5),9–18. https://doi.org/10.5815/ijcnis.2013.05.02 [3] Hazzaa, F. I., Kadry, S., & Zein, O. K. (2012). Web- Based Voting System Using Fingerprint: Design and Implementation. II [4] 404–409. [4] Nautiyal, J. (2013). An Automated Technique for Criminal Face Identification Using Biometric Approach. 2013(Cac2s), 608–611. [5] Patel, C. I., & Patel, R. (2013). Robust Face Recognition Using Distance Matrix. International Journal of Computer and Electrical Engineering,5(4),401–404. https://doi.org/10.7763/ijcee.2013.v5.740 [6] Yamini, K., Kumar, S. M., Sonia, S., Yugandhar, P. V, & Bharath, T. (2019). Class Attendance Using Face Detection and Recognition with OPENCV. 3822–3826. [7] Soomro, Z. A., & Ali, A. (2020). FPGA based real- time face authorization system for electronic voting system. [8] Kavitha, S. N. (n.d.). Biometrics Secured Voting System with Fingerprint , Face and Iris Verification. 743–746. [9] Wagner, P. (2012). Face Recognition with Python. 1– 16. [10] P, J. I. P., Kishorit, K. R., Ganesh, B., Gokulprashanth, P., & Udhayakumar, G. (2018). Electronic Voting Machine with Facial Recognition and Fingerprint Sensors. 3, Hazzaa, F. I., Kadry, S., & Zein, O. K. (2012). WebBased Voting System Using Fingerprint: Design and Implementation. II(Iv), 404–409.
Copyright
Copyright © 2022 Abbas Behrainwala, Amar Saxena, Ishika Navlani, Sakshi Sahay, Noshir Tarapore. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET39810
Publish Date : 2022-01-05
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

