Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Advance Security by Using Face Recognition
Authors: Asmita Nagpure, Mayuri Sonule, Surja Chauhan, Shreya Bhowate, Kunal Meshram, Prof. H. V. Gorewar
DOI Link: https://doi.org/10.22214/ijraset.2022.40347
Certificate: View Certificate
Abstract
In this paper we have proposed face recognition door lock system using raspberry pi for enhancing security purpose. Implementation of the device is for monitoring whether any unknown person is entering from the door. In order to get accurate and clear picture of an victim we have proposed Haar Cascade method for detecting face. As soon as the person enters near the door, pi camera captures the image of that person and face detection process is done then if it matches with images available in database then the door is unlocked otherwise a message with the picture of a person will be sent to the registered mobile through LAN network. The main motto of this project is to utilization of sensor with the combination of embedded equipment for the door opening systems. The main purpose of this system is to provide best security for home and office by using face recognition technique.
Introduction
I. INTRODUCTION
Nowadays, as the technology is developing rapidly, facilities for human beings are developing. In day-to-day activities, life of people has become very easier with the implementation of many new technologies. On the other hand, it also produces the major security issues. In general, in order to secure their residence, people make use of CCTV cameras. Images will store in the cloud, so that the action can be taken when any suspicious incident takes place. This type of approach is a passive. But there is a need for an active approach which works on Realtime. This type of approach is nothing but where actions can be taken immediately as soon as a security threat occurs. Hence a smart IOT based face recognition device is the new idea to develop, which recognizes the face of the person near by the door and compares with the uploaded faces stored in the cloud. If image of person is matched with database image, then the door would open and welcomes them. If an unknown person trying to enter, the owner would be alerted automatically by message and mail with an intruder image. To develop this system, we have used Raspberry Pi, Pi camera which will be installed intruder, DC motor to open the door through relay, indicate whether the door is opened or not, the security sector is experiencing diversification. Further modification in the system can be to biometric security system to ensure better security. Biometric security system includes fingerprint-based device was the first biometric locking system. Using the fingerprints of a known person for unlocking the door is main parameter for this system. However, like any other devices, they also have drawbacks. Fingerprints of a person can be duplicated by the victims. This can lead to opening of the door for victims. Finally, research moved to image processing system. This system provides high security.
This module is used in order to send messages to the registered mobile number. When a person wants to access his locker, initially at the main door of locker and sensor will be placed. This sensor will sense the body temperature of a person who is standing near the door. And then, his/her image will be captured by the camera which is installed at the main gate. This image will be given to the PC where the MATLAB software will compare this image with the authentic images stored in the PC If the person is authentic, then only the door will open otherwise it will remain closed and the alarm will buzz for further action to near the door for recognition of face.
II. LITERATURE REVIEW
In this project we using one camera which is identify an owner of home and open the door in few second. If in home kids or older age's in home need more attention and care that time, we not able to go home that we need someone how take care our love one's but here's problem how go inside the home because face recognition system that time we use alternate option the system well send notification to owner told some stand out of door or the person call owner how to get inside the home by enter OTP.From decades, for science society using of smart home is not a new term. As there is an advance in technology there is a fast increase in the field of home security automation. The control of smart device for automatic door lock system is done using Bluetooth, internet etc. Most of the laptops, tablets, mobiles have built-in adapters which in turn reduce the cost of the system, but it controls within the Bluetooth range not beyond that. The system which is based on SMS technology have only one components i.e. micro controller. Here micro controller is working like bridge between the user, sensors and actuators. By using PCA, Eigen faces are generated by changing the faces available in the database. Distance of the person from door is calculated by Euclidean distance method. If the distance is less, then only it is a recognized face. After that by using module the system generates an alert message to the owner.
A. LBPH Algorithm
Humans’ beings perform face recognition every day and practically with zero effort. Although it seems like a very simple task for us, it has proven to be a more complex task for a computer, as it has many variables that can impair the accuracy of the system, for example: illumination variation, low resolution, occlusion, amongst other and more. In computer science, face recognition is basically method of recognizing a person based on their facial image. It has become very famous in last two decades, mainly because of the new methods developed and the high picture quality of the current videos/cameras.
Equations
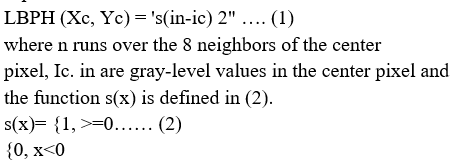
But there are few limitations to LBPH operator that its small 3x3 matrix method cannot capture the dominant features of large-scale structures. As a result of that, it fails to deal with the texture at different scales, the operator can be extended to use neighborhoods of different.
B. Haar-Cascade Classifier
Detection of object using Haar feature based cascade classifiers is an effective detection of object method proposed by Paul Viola and Michael Jones!". It is a based-on machine learning approach where a cascade function is developed from a lot of positive and negative images. It is then used for detecting objects in other images. Here, we are working with face detection. Initially, the algorithm requires a lot of positive images (images of faces) and negative images (images without faces) to train the classifier accordingly. Then we need to extract features from it. Features are nothing but numerical information extracted from the images that can be used to differentiate one image from another.
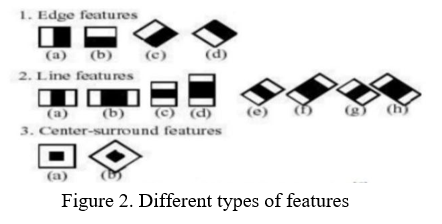
Figure 2 shows different Haar features. A simple rectangular Haar like feature can be defined as he differences between the sum of pixels of areas inside the rectangle, which can be at different position and Scale within the original image. A Haar-like feature takes neighboring rectangular regions at a specific location in a detection window, sums up the pixel intensities in each region and calculates the difference between their sums. First, the pixel values inside the black area of rectangular region are added together then the values in the white areas are added. This result is used to differentiate the image sub regions.
An example of this would be the detection of human faces in the images. The areas around the eyes are more darker than the areas on the cheeks!). One example of a Haar like feature for detection of face is therefore a set of two neighboring rectangular areas above the eye and cheek region.
C. Proposed System
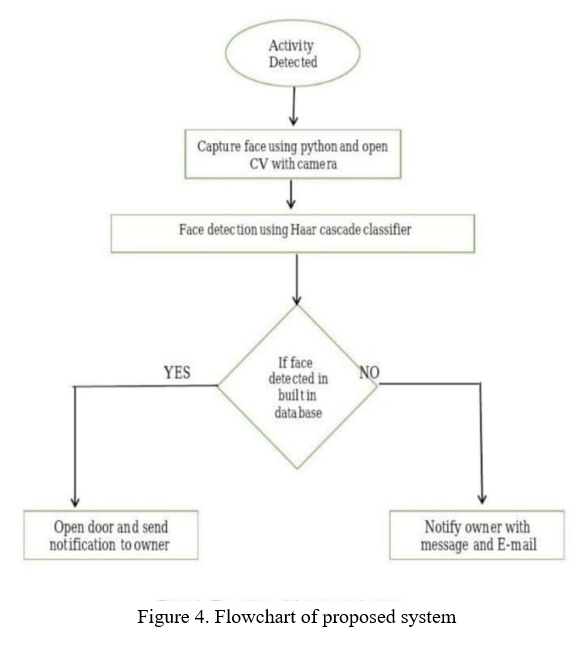
After preprocessing like resizing and cropping of images, Haar cascade classifier is used to detect if there is a single face detected or multiple. Figure 4 shows the flowchart for the proposed system of this project. Edge, line, and center surround are the features of Haar which are taken as inputs. By using these cascade features the test of the image is done. The features of Haar are then divided into various stages. Stage by stage the rectangular windows will be tested. The initial stages will having less Haar-like features. If the first stage window fails, then it is to be discarded from the process and the next stages will not be tested. If all the stages successfully completed then only it is considered to be face is detected and then it checks with the images already stored in database of raspberry Pi [9, 12, 13, and 14]. The main advantage of Haar cascade classifiers is to fast detection speed as compared to other classifiers.
D. Methodology
The first task is to collect the data for which we are going to train our classifier. We will write a python code that will take thirty faces of each individual person using OpenCV pre-trained classifier. When the person press the button, the implemented code now called using the camera, system capture the image sequence and compare this image with database. If the image is match , then in application module get the signal to the door. In this project , for face detection and identification we are using machine learning, deep learning and python. For recognise face we using camera and for controlling the locking system weare using nodemcu and all modules integrated through server.
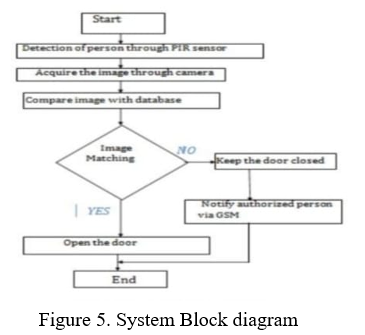
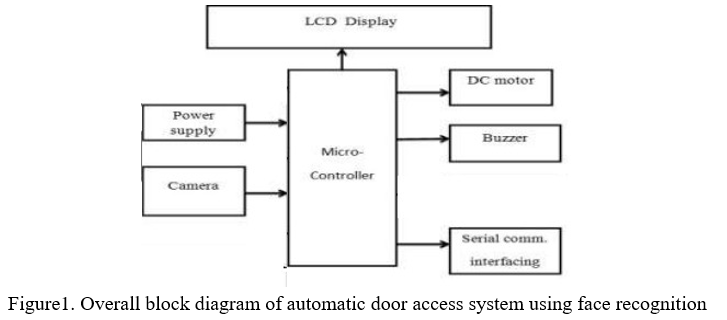
According to above block diagram shown above, first motion is detected by sensor then the image is captured by camera which is input to the microcontroller, Microcontroller checks whether given input is saved within the database. If yes then the door will open, which is mechanical function done by DC motor. If input image does not match with image in the database then door will remain closed and Buzzer will start beeping and the result will be displayed on the LCD. This project uses system to send notification of an unauthorized person and also to connect hardware with PC it uses serial communication interfacing.
E. Circuit Diagram
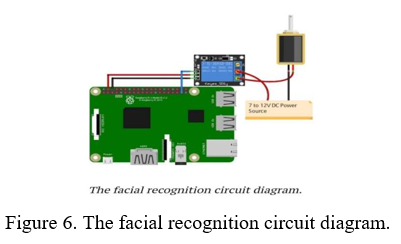
The circuit shows the design of automatic door lock system. The components used are nodemcu, solenoid, adapter . sensor works as a main function. a live body generally emits infrared energy which is sensed by the sensor from considerable distance. This sensing signal is feed to a microcontroller to check the operating range of the sensor, it sends a logical command to open the door. The door automatically closes with affixed time delay. If there is no further movement within the operating range. The interrupt signals are used through limit switches to avoid reverse rotor condition of the motor. The GPIO pins of the Raspberry Pi are use to give an output of 3.3V but the solenoid lock requires 7-12V to operate. Due to this, we will need to use an external power supply and relay to operate the lock. Connect the VCC and GND point of the relay module to 5V and GND of Raspberry Pi. Then connect the signal pin of the relay to the GPIO 26 of the Raspberry Pi. On the other side of the relay module, connect the negative wire form DC power source to the negative point of the solenoid door lock. Connect the positive point from the DC power source to the common of the relay module and then connect normally open from the relay module to positive point of the solenoid door lock. Machine learning algorithm is used to avoid the complexity of calculations, which is inbuilt in Open CV library . Raspberry Pi processes the captured image coordinates with the existing coordinates of the images in the database. If the images matches, then it sends the signals to relay switch through GPIO pins.
III. HARDWARE DESIGN
A. I3 Processor
This processor is Developed and manufactured by “Intel” and first introduced and released in 2010 . This core i3 is a dual-core computer processor, Available for use in both desktop and laptop computers . It is one of three types of processors in the “I” series (also called the Intel core family of processors)
B. OS Windows XP
Windows XP is a major release of the windows operating system developed by the Microsoft . Itis the direct successors to both windows 2000 for professional users and windows Me for home users, and was released to manufacturing on august 24,2001, and later to retail on October 25,2001.

IV. IOT COMPONENTS
A. NodeMCU
NodeMcu is a very low-cost open source IOT device. It initially included firmware which runs on the ESP826 wifi SoC from Espresso if systems , and hardware which was based on the ESP-12. Later, support for the ESP32 32- bit MCU has been added.
B. Solenoid
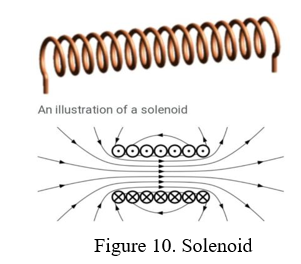
In electro-magnetic technology, a solenoid is an actuator assembly with a sliding ferro-magnetic Plunger inside the coil. without power, the plunger extends for part of its length outside the coil and applying power pulls the plunger into the coil.
C. Adapter
An adapter is the device or system that converts attributes of one electrical device to otherwise incompatible device or system. Some modify power or signal attributes, while others merely adapt the physical form of one connector to another connector.
V. IMPLEMENTAION
There are single parts in this implementation step. The implementation of face recognition system by using MATLAB.
A. Implementation of Face Detection And Recognition
Matlab2014a is used for coding. In the database folder, 50 different facial part of images for ten persons are used as the training images. While making the folder in the database, the captured images are applied and cropped by face detection module in order to obtain the only facial parts of all images with different directions For instance, five images of a person with different face directions are shown in figure 12.

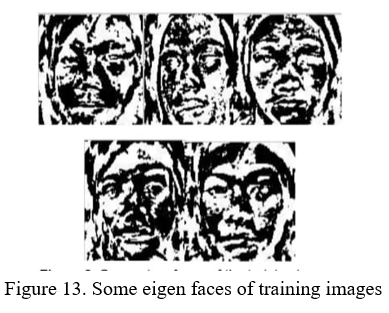
All training images are reshaped and converted into 125x125 gray scale images by using resize and rgb2graymatlab built-in function. Mean centered (or subtracted) images are evaluated by subtracting image from the original training image in the database. The eight vectors corresponding to the covariance matrix define the Eigen faces which looks like ghostly faces. Since 50 training images are used, 50 eigen faces are obtained. Some eigen faces of the training images are shown in figure 13.
The trained and test images are projected onto the facespace where the eigen faces are the coordinates or dimensions to find their respective euclidian distance. By comparing the euclidian distance of all projected trained images with the projected test image, minimum distance between them which shows similarity to test image is obtained. By using this way, the facial image recognition was done in system.
VI. SIMULATION TESTS AND RESULTS
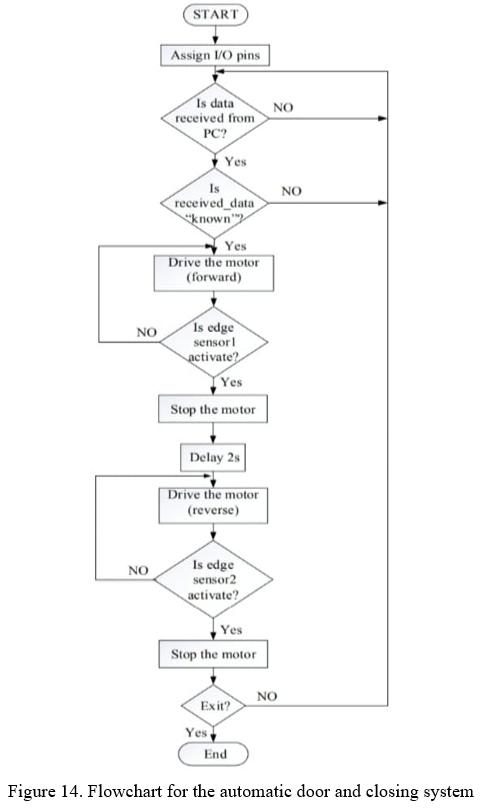
The overall automatic door access system using face recognition is simulated by using PROTEUS software and MATLAB. VSPE software are used to create a virtual serial port for the communication. A MATLAB GUI is created in order to perform an automatic face recognition and detection. There are two cases in this system. The first is automatic opening of door for the recognized person and the second is ringing the alarm for the unauthenticated person. In this system, input images are taken through the camera continuously until and unless the ‘stop camera’ button is pressed. Figure 15 shows the MATLAB GUI result when captured face is detected and recognized as authenticated person
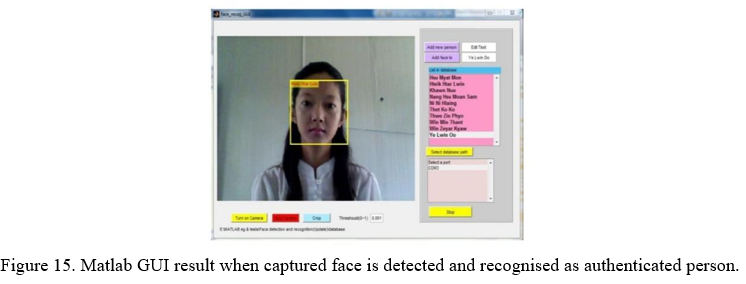
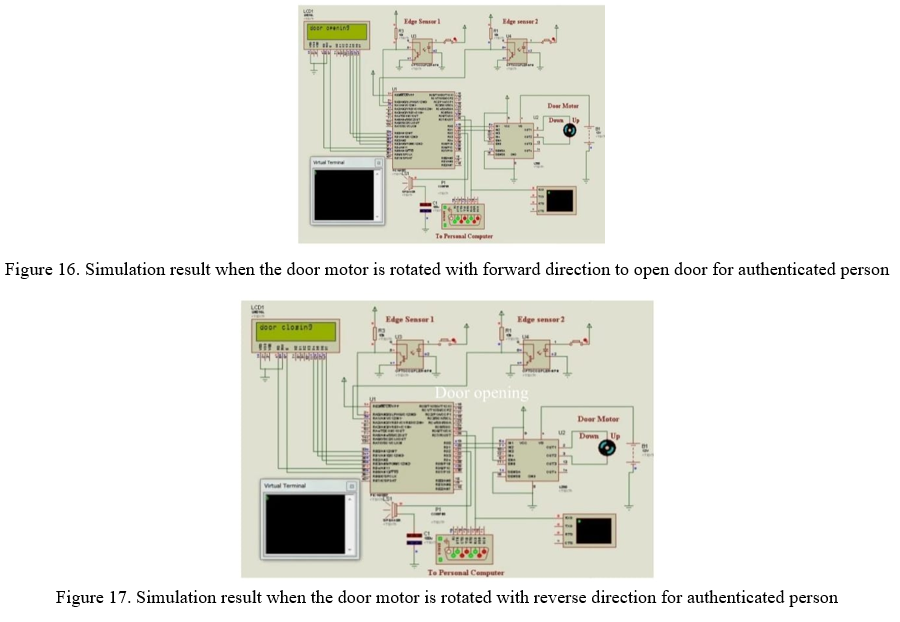
When the captured image is recognized as the authenticated person, door motor is rotated in the forward direction until the edge sensor 1 is activated after opening the door. When the sensor 1 is activated, the door motor is stopped. After 2 seconds, door motor is rotated with reverse direction until edge sensor 2 is activated.
Figure 16 and 17 show the simulation result for authenticated person.
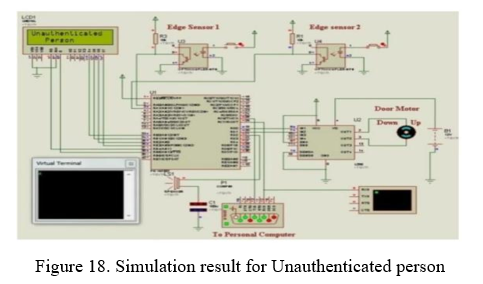
When the captured image is recognized as unauthenticatedperson, alarm is rung and door is still closed. This simulation result is shown in figure 18.
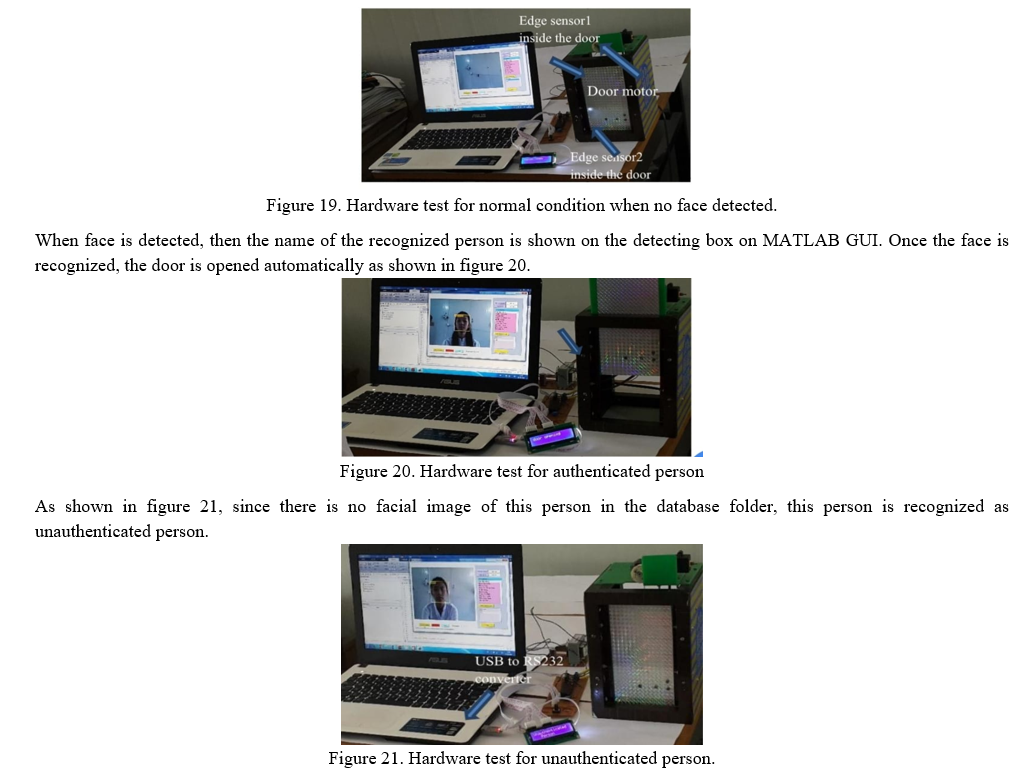
VII. HARDWARE RESULTS
To perform automatic door access system, personal computer (PC) is connected with the microcontroller via USB to RS232 converter. When no face is detected in front of the webcam, any signal is not sent to the microcontroller. Since microcontroller is not received any signal from PC, the door remains closed. This situation is shown in figure 19.
VIII. ACKNOWLEDGEMENT
Authors would like to take this opportunity to extend her deepest gratitude to their guide Prof. Harish Gorewar, for his all round support ,encouragement ,guidance during the period of her project with a keen interest, enthusiasm, vigor and his ever-helping nature from the starting of the project till the completion of this report/synopsis. It is all because of his untiring endeavors, able guidance and valuable suggestion, that could synchronize my efforts in covering the many diverse features of the project and thus helped me for the smooth progress and success of project. Author indebted to him for the valuable time he has spared for me during this work. Authors would also like to thank Head Of Department Dr. S.P. khandait for providing the excellent facilities which . she can never forget their unconditional support and encouragement to pursue her interest. This acknowledgement would not be complete without expressing my personal belief in and gratitude towards the almighty God . Author Thank God for bring her through this experience to her the glory.
Conclusion
This face recognition system is not 100% accurate, but it works well in good light conditions. The problem with this is it can also detect faces from pictures for instance, someone can unlock the door by showing your picture from his mobile phone. We can resolve this issue by training our own cascade classifier. Face recognition-based door locking has been developed to provide better security. It is user friendly system. The use of Eigen face recognition technique makes this system more secure and faster. This system can be used where high security is required where confidential information and equipment is kept inside. For example, research institutes, banks, forensic Laboratories. This system can also be used for domestic uses for providing securities to home. This project helps to avoid the problem of thefts and frauds by victims. In case of unauthorized person\'s trying to enter then thsese system alerts authorized person with SMS and at the same time the buzzer beeps to alert people. This is a cost efficient and reliable door locking system.In this paper we have implemented a face recognition door lock system. Recognizing of faces is done by using cascade classifiers, which gets a high accuracy and will store in the database.For this testing, we have used 40 images only. Computervision is used in the IOT. For security purpose, we have implemented real timeface detection by Haar classifier. Thus this system can useful for senior citizens living alone and for mobilized people. Hence the proposed system is practically easy to construct and easy to track the path.
References
[1] Y. Januzaj, A. Luma, Y. Januzaj, V. Ramaj., \"Real time access control based on face recognition,\" in International Conference on Network Security Computer Science (-15), pp. 7-12, 2015. [2] M. Sahani, C. Nanda, A. K. Sahu, B.Pattnaik., \"Home security system based on face recognition,\" 2015 Int.Conf.Circuits, Power Comput. Technol. (ICCPCT-2015), pp. 1-6, 2015. [3] G. Senthilkumar, K. Gopala krishnan, V. S. Kumar., \"Embedded image capturing system using raspberry pi system,\" vol. 3, No. 2, pp. 213-215, 2014 [4] M. R. Mulla., \"Facial image based security system using PCA,\'pp. 548-553, 2015. [5] M. H. Jusoh & F. Bin Jamali, \"Home security system using internet of things,\" 2017. [6] S. S. Liew, M. Khalil-Hani, S. Ahmad Radzi,R.Bakhteri., \"Gender classification: A convolutional neural network approach,\" Turkish J. Electr. Eng. Comput. Sci., vol. 24, No. 3, pp. 1248-1264, 2016. [7] M.Sajjad et al., \"Raspberry pi assisted face recognition framework for enhanced law-enforcement services in smart cities,\" Futur. Gener. Comput. Syst., 2017. [8] A. R.Syafeeza, S. S. Liew, R. Bakhteri., \"Convolutional neural networks with fused layers applied to face recognition,\" Int. J. Comput. Intell. Appl., vol. 14, No. 3, 2015. [9] A.R.Syafeeza, M. Khalil-Hani, S. S. Liew, R.Bakhteri.,\"Convolutional neural network for face recognition With pose and illumination variation,\" Int. J.Eng. Technol., Vol. 6, No. 1, pp. 44-57, 2014 [10] K.Syazana-Itqan, A. R. Syafeeza, N. M. Saad, N. A. Hamid, W.H. Bin Mohd Saad., \"A review of finger-vein biometrics identification approaches,\" Indian J. Sci. Technol., vol. 9, No.32, 2016. [11] Mahender K, Kumar TA and Ramesh KS PAPR 2018 analysis of fifth generation multiple access waveforms for advanced wireless communication, International Journal of Engineering and Technology (UAE), 7(3.34 Special Issue 34) 487-490 10.2147/NBHIV.S68956_old [12] Swathi N, Padmaja Ch and Navya Jyothi G 2020 Audio assistive for blind people to identify the cloth patterns and colors Journal of Critical Reviews, 7(17) 154-158 10.31838/jcr.07.17.2 [13] Sourav Roy; Md Nasir Uddin; Md Zahirul Haque; Md Jahidul Kabir, “Design and Implementation of the Smart Door Lock System with Face Recognition Method Using the Linux Platform Raspberry Pi”, by IJCSN - International Journal of Computer Science and Network, 7(6), [14] I. Aydin and N. A. Othman, \"A new IoT combined face detection of people by using computer Vision for security application,\" International Artificial Intelligence and Data Processing Symposium (IDAP), Malatya, 2017, pp. 1-6, doi: 10.1109/IDAP.2017.8090171.ecember 2018 [15] Mohammadjaved R. Mulla; Rohita P. Patil; S. K. Shah 2015.Facial Image Based Security System using PCA. [16] P. Bhatia, S. Rajput, S. Pathak and S. Prasad, \"IOT based facial recognition system for homeSecurity using LBPH algorithm,\" 2018 3rd International Conference on Inventive Computation Technologies (ICICT), Coimbatore, India, 2018, pp. 191-193, doi: 10. [17] Ishaan Sathe, Chiman Patel,(April-2017) Prasad Mahajan, Tanmay Telang, Sejal Shah,Automatic Locking Door Using Face Recognition. International Journal of Engineering Technology Science and R [18] Nadafa, Raju A., et al. “Home Security against Human Intrusion Using Raspberry Pi.” Procedia Computer Science, 167, 2020, pp. 181120. DOI. or (Crossref), doi: 10.016/ j.procs. 2020.03.200esearch(IRJET).Volume 4, Issue 4.ISSN 2394 –3386.http://www.ijetsr.com/ [19] Dipesh Vaya1, Teena Hadpawat2, (Feb- 2018).pca based efficient face recognition technique.International Journal For Technological Research In Engineering.ISSN (Online): 2347 – 4718 [20] Arti Barde1, Swapnil Bilbile2, Shubham waghmare3, Prof. J. D. Dorve4,(Feb-2018).review on door bell notify with image capture and forward through email. International Research Journal of Engineering and Technology (IRJET).Volume: 05 Issue: 02.e-ISSN: 2395-0056,p-ISSN: 2395-0072. https://www.irjet.net/
Copyright
Copyright © 2022 Asmita Nagpure, Mayuri Sonule, Surja Chauhan, Shreya Bhowate, Kunal Meshram, Prof. H. V. Gorewar. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET40347
Publish Date : 2022-02-14
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

