Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Face Recognition Attendance System Using Open CV
Authors: Sakshi Jawale , Pranit Londhe, Rushikesh Kolekar , Sarika Jadhav, Prajwali Kadam
DOI Link: https://doi.org/10.22214/ijraset.2023.49104
Certificate: View Certificate
Abstract
According to recent data, schoolchildren are the group most susceptible to social crimes that take place anywhere in the globe, including in our own country. On their way to and from school, many of these instances take place. Other times, social offence like sexual harassment happened to them when they were riding the school bus. We suggest a real-time monitoring system based on image processing methods because of how serious the problem is. The media has made using a camera to identify a pupil more commonplace. This system monitors the bus cameras and examines the children\'s movements. The technology recognises student faces and records student ID numbers. The technology will also sound an alarm to notify the public if the situation is urgent. Technologies that can be used with Python are included in the Open CV (Open Computer Vision) package. Face detection was performed using the Haar-Cascades classifier, and face identification was performed utilising Eigen faces. Using flowcharts, the system\'s levels are represented. Furthermore, The automation attendance systems use face recognition, This eliminates the vast majority of problems that manual attendance systems.
Introduction
I. INTRODUCTION
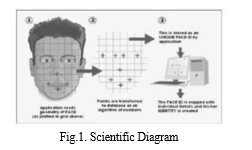
FD and Face Recognition (FR) two aspects of Computer Vision that have grown in relevance over time (CV). Practical uses include automatically labelling your friends' photos, biometric security, and so on. Because of its vast potential, several academic institutions and corporations have been researching on it. The proposed system maintains authentic and correct student attendance records, which are regularly validated, maintained, and controlled. Face recognition refers to the challenge of recognising a previously identified item. The problems of face recognition and face detection are frequently conflated. Face Recognition determines if a "face" is known or unknown. Systems for tracking students' attendance come in two flavours: automatic and manual. Manual attendance systems keep each kid's record on the school bus. This strategy seems to be problematic in sessions with a big number of students present. It takes time to manually record and compute each enrolled student's average attendance. Algorithms for identifying and detecting human faces were built into the monitoring system. The fifth revolution has begun with the Scada Relay when the fourth sensor signals the PLC that the vehicles is in the fifth unit. And the succeeding unit is closed with a similar unit this sensor now locks the conveyor, and it is over with one timer. The conveyor may use the 5th section to flip on and off when the timer's period is over. Facial recognition techniques are divided into two categories. The second method creates a priorities list of matches by comparing the specified person to the database of all other people. Whereas the first technique compares the supplied human to who they claim to be and returns a yes or no judgment[1]. The many stages of face recognition are shown in Figure.
The surveillance system employs computer vision and machine learning techniques. Deep learning approaches are utilized to solve a wide range of problems. These methods can help to reduce mistakes at each level of the process.
II. RELATED WORKS
This section discusses many studies dealing with facial recognition, detection, and template matching. The research proposes a facial recognition attendance system based on deep learning. We create CNN cascades or neural networks for face detection applications and identification. detection Face and embedding face creation are both possible applications. CNNs perform better on larger datasets than on smaller ones. The biggest difficulty was applying deep learning algorithms to limited datasets. This model might be linked into another system and used to help with monitoring.
[4] The research study It considers a student counting mechanism in a classroom as well as in a congested place. In order to accomplish face recognition tasks, both the discrete wavelet transform and the discrete cosine transform are used (DCT). Authentication is important in the field of informatics. These two strategies are used for user authentication. We implemented biometric verification and human face recognition for our video monitoring/surveillance system. A new, effective deep convolutional network (DCN) is discussed in the article [5]. This recognition faces in a range of conditions. The main challenge in most contemporary face identification systems demonstrates high runtime speed and DCN use. epsilon- Support Value Regression (SVR), a method for counting and identifying people in densely populated images and video scenes[6], is used. A novel technique to automatic student and people counting based on facial identification, when a video security camera is installed to count the number of people who enter a door [7]. The main concept is to begin with the difference in frames. Particularly sophisticated is the integration of crowd density estimation with geographic localization of specific persons. Counting people [9] discusses an exceedingly complicated subject with video surveillance. When the work is finished in real time, it gets harder. the integration of channel state data (CSI) from a WiFi network with infrared (IR) sensors. Traditional techniques provide a count but have range limitations and are only applicable in controlled contexts. Video surveillance is one of the sophisticated technologies utilised in modern life, and it is used to measure population density in a location for security and to collect demographic data on individuals. When people are moving or in motion, vision-based solutions in informatics perform effectively and a clear high-quality picture is available.
III. ARCHITECTURE PROPOSED SYSTEM
This essay suggests a revolutionary technique of monitor children on school buses. This technology monitors the visuals on the bus and recognises the children and their actions. The technology recognises student faces and records their numbers. This section describes the proposed system's system architecture, include a block diagram and a full discussion Face detection of identification and template compatibility procedures.
A. System Architecture
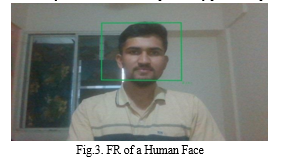
Largely free software, the Open Source Of The Computer Eyesight. used for machine learning and image processing. Additionally, real-time computer vision was a goal. The OpenCV Library was used to develop the detection component for proposed project. Real-time drawing of a rectangle around the faces of passing pupils allows the OpenCV package to recognise and highlight a face while also revealing the student's name, proving its suitability for the task. The professor could observe both students passing as their faces are recognised and from the feedback system's detection portion because this took place in a rectangular-shaped window created by the face recognition. The raw picture is the result of the low-level processing. Average level processing entails gathering additional information not previously gathered and removing areas of interest from an image's output after low-level processing.
Describes the suggested monitoring system architecture and some basic processes. Some of the fundamental processes in image processing include image acquisition techniques, which are used to get a picture from a given source and digital image acquisition. The next step should be to increase image quality so that other procedures can succeed. The image segmentation approach is then used to separate an incoming image into its constituent objects' essential parts. Image segmentation is the process of transforming raw data into a format that a computer can process. Picture description is all about extracting image characteristics.
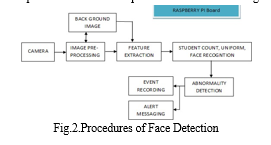
Face detection and preprocessing procedures are at the heart of the challenges with face identification. It is accurate that it brings a new technology that is error-free. Before beginning the steps of the procedure, we must first recognise their faces and define landmarks as well as extracting the face aspects. By removing background images and extracting features from the complete face, segmentation difficulties are resolved.. The camera is linked to the raspberry pi, and the processes are completed to determine the student count, uniform detection. compute the number of pupils present using facial recognition. In actuality, genuine recognition is dependent on uniforms and identification cards.
To capture the complete interior view, The board's camera will be installed inside the car in a practical place. following The applications of image processing are listed:
- Obtain a reference background by processing an interior image of an empty car.
- Take photographs in the car at regular interval; after deleting the background image, extract the specific aspects of the image.
- Count the students present and name each one.
- Identify pupils who are seated as well as those who are standing.
- Determine the pupils' uniforms.
- Incident detection and documentation
The information gathered will be sent outside the vehicle using the board's built-in Wi-Fi module for the Raspberry Pi. The CPU on board will be used for image capture and all digital signal processing. A feature-based extraction and detection technique, additionally to an image-based approach, are designed to meet the difficulty of detecting and identifying occurrences to be reported. Additionally This system's intelligence would be built on neural networks and statistical methods.
IV. IMPLEMENTATION
This project makes use of the 64-bit quad-core Broadcom BCM2837 ARMv8 processor CPU-powered Raspberry Pi 2. This microcomputer has 1GB of SDRAM and runs at 1.25 GHz.
A. Face Detection
For numerous researchers and applications, face detection is essential and intriguing, such is face recognition in video surveillance, object tracking, template matching, and expression analysis. It consists of three phases, each of which serves an important purpose. Examples include preprocessing, feature extraction, and data categorization. To begin, preprocessing is the removal of certain areas from pictures or real time web cams, which are subsequently utilised as candidate images for faces or non-face items. Second, feature extraction entails extracting the necessary characteristics from previously processed pictures.
Calculations provide the foundation of this approach. We assess a few characteristics, including nose breadth, length, height, and so forth. from pictures of the famous individuals. The facial image contained several traits that were similar to those of recognisable people.
B. Face Recognition
Figure 4 depicts a student's facial recognition. In order to identify faces using neural networks, more training data is required, as well as a large quantity of computer power. The technology is based on a deformable template and includes a component analysis method or algorithms.
V. RESULTS AND DISCUSSIONS
Facial data were seen, identified, and recognised the students' faces. We explored recognition and detection using a variety of data sets and training sets. We are testing the detection process by varying the lighting and some of the other circumstances and factors. The computational models in this project that involve some techniques and are used for processing and implementation. Python scripts were created to recognise faces in images from a specified data collection. This suggested strategy provides organisation benefits as well as the safety of children on their school bus.
Conclusion
Face detection for automatic student monitoring and identification was slow and hence inaccurate. The system\'s primary realworld applications are matching and detection. The method proposed in this research would be suitable for crowd monitoring and since retinal recognition, detection and Using the thermal spectrum for facial identification calls for extreme precision.. Implementing such technologies would boost the possibility of discovering and following up on suspects for little enforcement. This study provides a look into what the future of computer vision may hold. Face detection, identification, and template matching were all successful.
References
[1] Sunehra, D., and V. S. Goud (2016, October). System for tracking and consolidating attendance using Arduino and Raspberry Pi. The International Conference on Signal Processing, Communication, Power, and Embedded Systems (SCOPES) was held in 2016. (pp. 1240-1245). IEEE [2] E. Osuna, R. Freund, and F. Girosi (1997, June). Training support vector machines: an application to face detection. In the cvpr (p. 130). IEEE. [3] M. Arsenovic, S. Sladojevic, A. Anderla, and D. Stefanovic (2017, September). FaceTime is a facial recognition attendance system based on deep learning. In 2017 [4] S. Lukas, A. R. Mitra, R. I. Desanti, and D. Krisnadi (2016, October). Face recognition technology is used in a school attendance system. In 2016 [5] Patil, A., and M. Shukla (2014). Implementation of a facial recognition-based classroom attendance system. 7(3), 974. International Journal of Advances in Engineering and Technology. [6] S. Yang, P. Luo, C. C. Loy, and X. Tang (2015). A deep learning method to facial part responses and face identification. IEEE International Conference on Computer Vision Proceedings (pp. 3676-3684). [7] V. Chauhan, S. Kumar, and S. K. Singh (2016, December). Estimating the number of people in high-density crowd photos and videos. In 2016 [8] M. Rodriguez, I. Laptev, J. Sivic, and J. Y. Audibert (2011, November). Person recognition and tracking in crowds based on density. International Conference on Computer Vision 2011 (pp. 2423-2430). IEEE [9] B. Zhan, D. N. Monekosso, P. Remagnino, S. A. Velastin, and L. Q. Xu (2008). A survey for crowd analysis. 345-357 in Machine Vision and Applications, 19(5-6). [10] Redmon, J., Divvala, S., Girshick, R., and A. Farhadi (2016). You just need to glance once: unified, real-time item detection. Proceedings of the IEEE conference.
Copyright
Copyright © 2023 Sakshi Jawale , Pranit Londhe, Rushikesh Kolekar , Sarika Jadhav, Prajwali Kadam. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET49104
Publish Date : 2023-02-13
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

